Wyoming Identity Theft by Known Imposter Package
What is this form package?
The Wyoming Identity Theft by Known Imposter Package is a collection of essential legal forms designed to assist individuals who have fallen victim to identity theft by someone they know. This package empowers you to communicate effectively with creditors and various entities to restore your good name and resolve issues stemming from identity theft. Unlike other identity theft packages, this one specifically addresses situations involving known imposters, providing tailored resources and documents to navigate the recovery process.
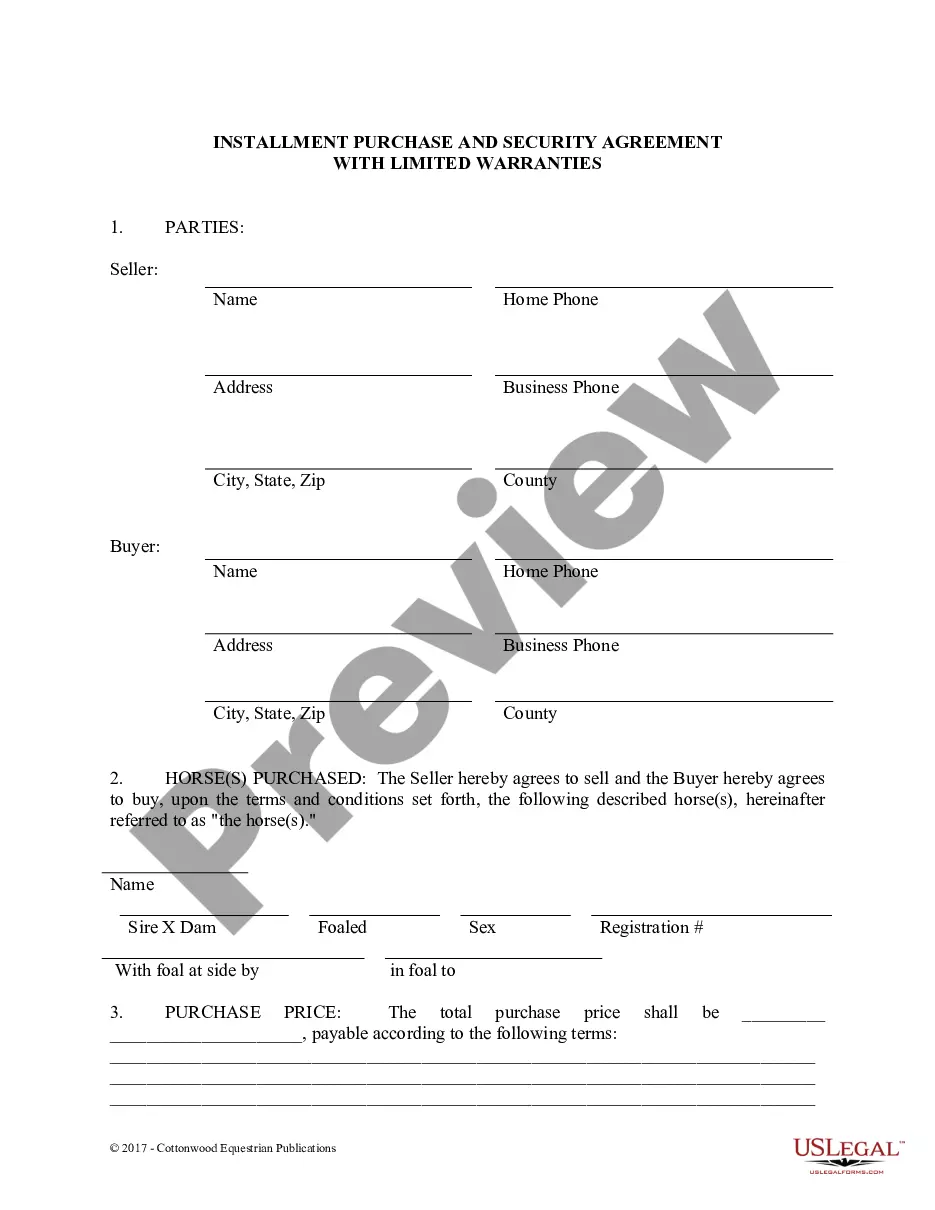
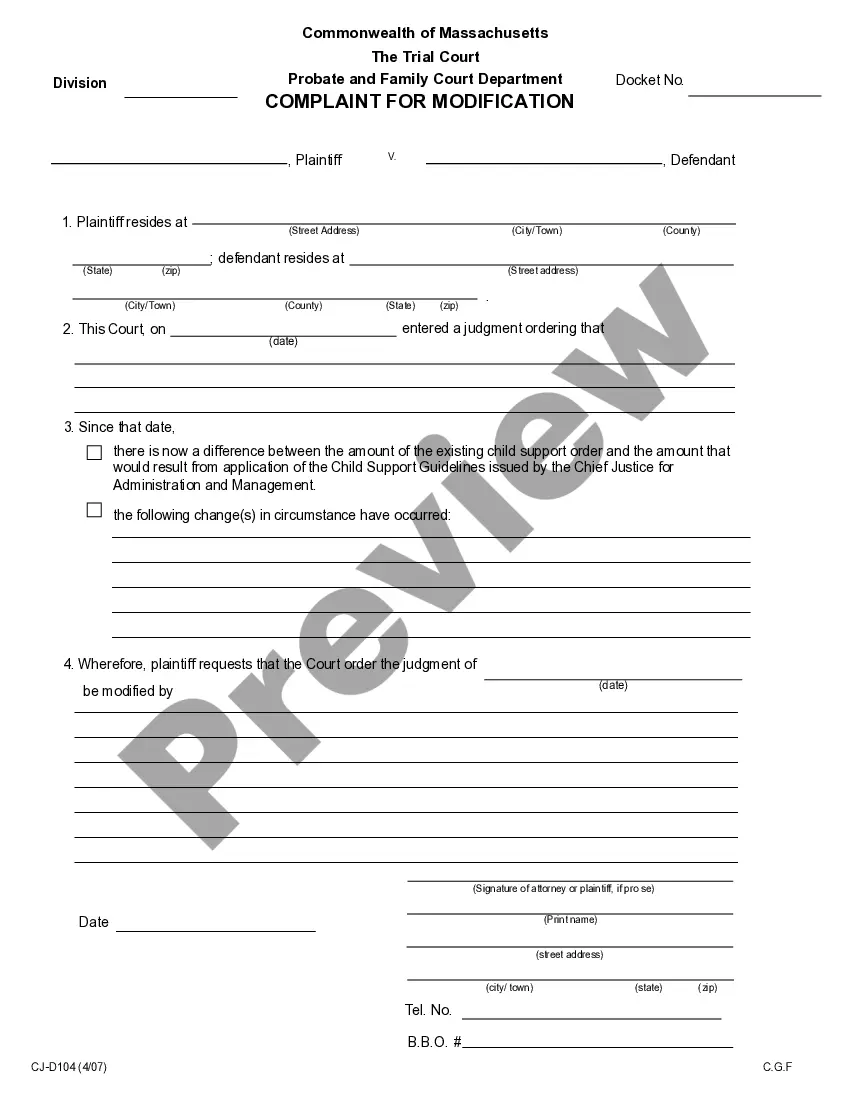
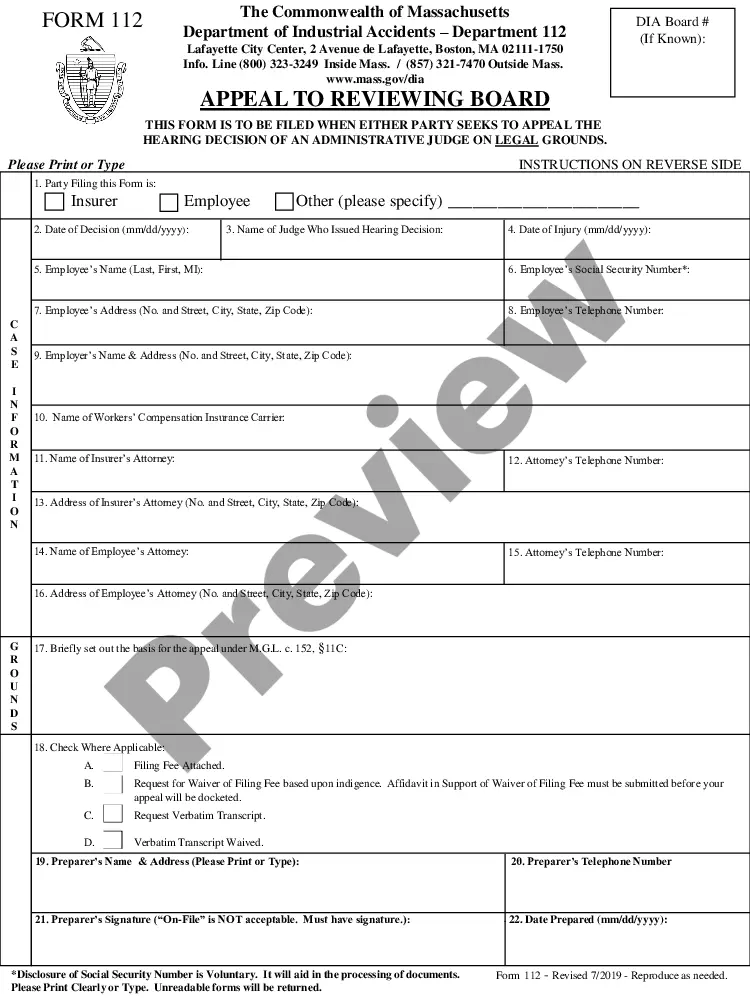
What’s included in this form package
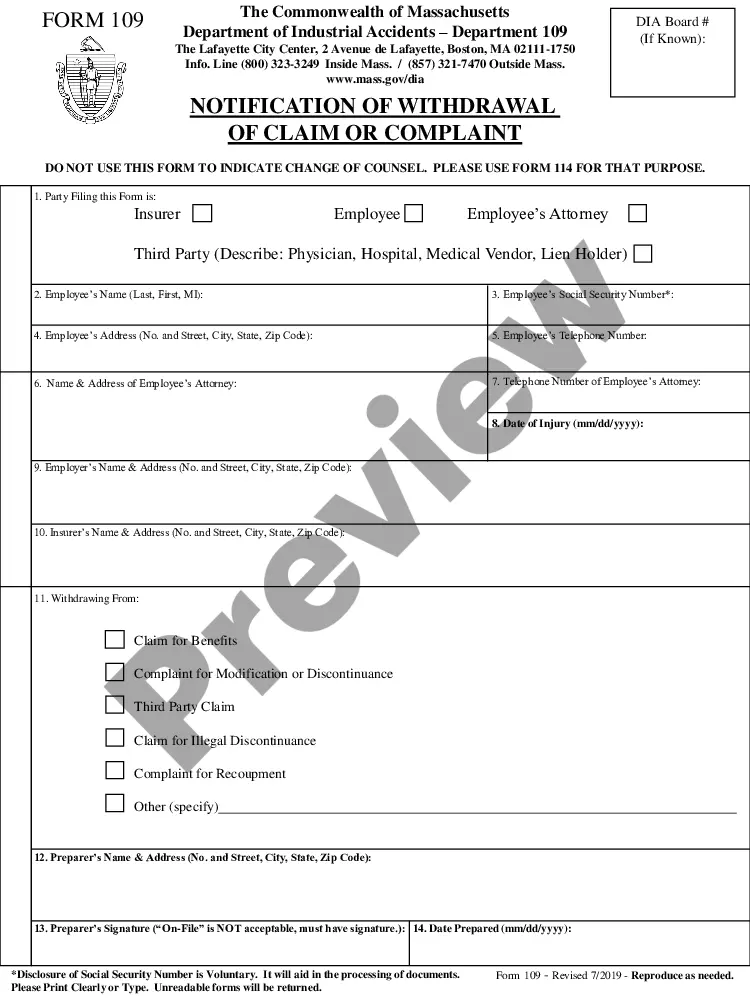
- Federal Trade Commission Affidavit regarding Identity Theft
- Identity Theft Contact Table
- Identity Theft Checklist
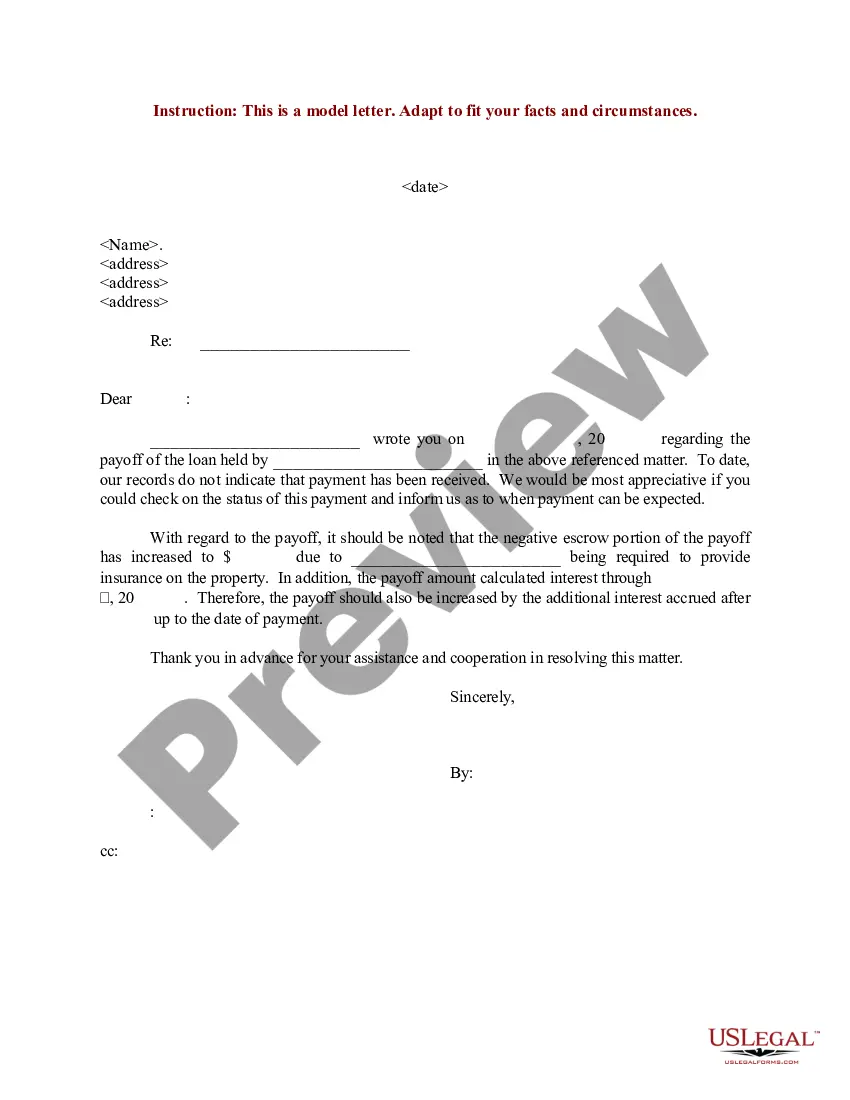
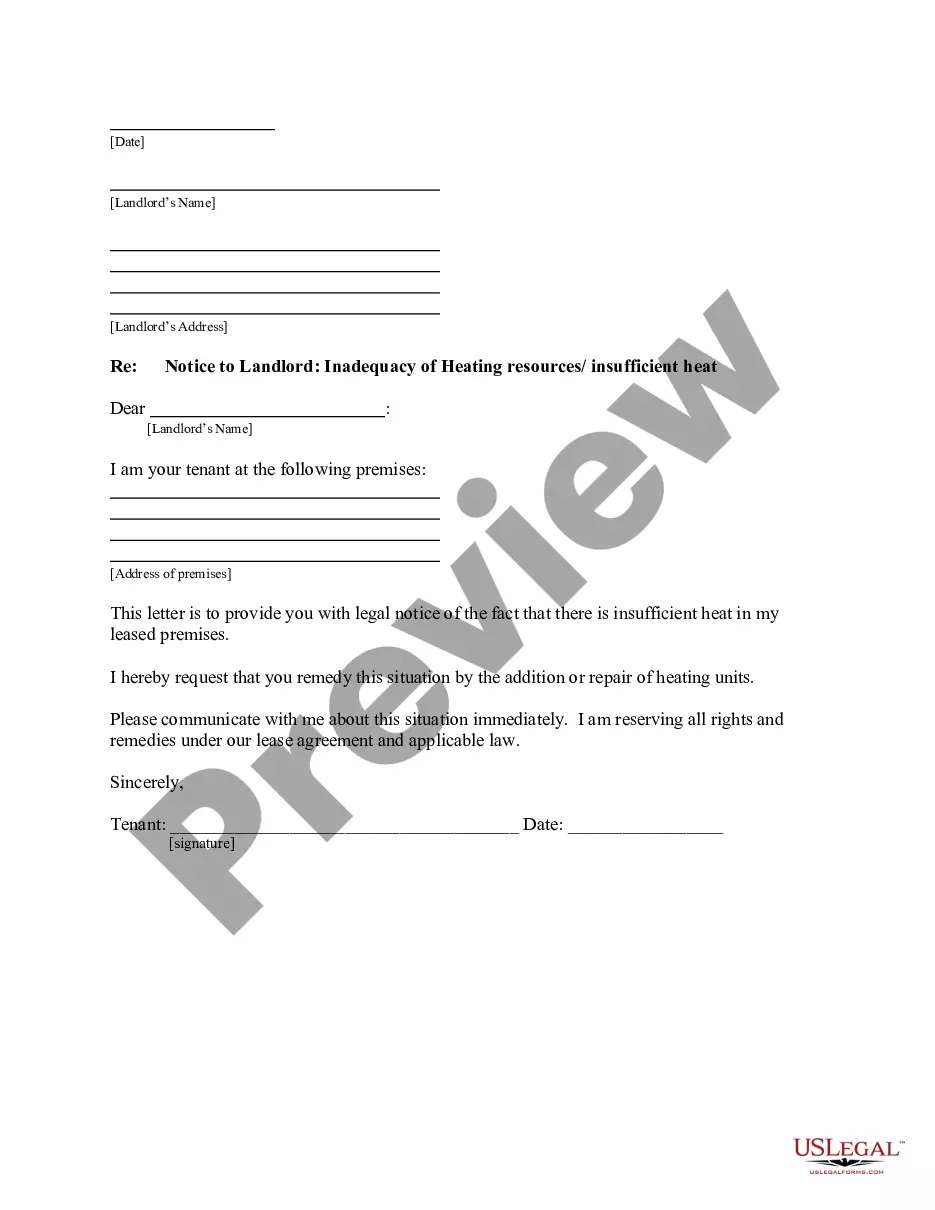
- Sample Letter to Report False Submission of Information
- Guide for Identity Theft Victims Who Know Their Imposter
- Letter from Identity Theft Victim to Credit Issuer Regarding Known Imposter Identity Theft
- Letter from Known Imposter to Creditor Accepting Responsibility for Accounts, Charges or Debits
- Letter Agreement Between Known Imposter and Victim to Work Out Repayment Plan
- Letter to Law Enforcement to Report Identity Theft by Known Imposter
- Letter to Credit Reporting Company or Bureau Regarding Known Imposter Identity Theft
- Letter to Report Known Imposter Identity Theft to Postal Authorities
- Letter to Report Known Imposter Identity Theft to Social Security Administration
- Letter to Report Known Imposter Identity Theft to Other Entities
- Sample Letter for Request for Free Credit Report Allowed by Federal Law
Common use cases
This package is useful in the following scenarios:
- When you discover that someone you know has stolen your personal information.
- If you need to alert creditors or financial institutions about fraudulent charges made in your name.
- When you require formal communication with law enforcement regarding identity theft issues.
- If you want to work out a repayment plan with the known imposter.
- When you need to report identity theft to credit reporting agencies or other relevant entities.
Who this form package is for
- Individuals who have experienced identity theft by someone they know.
- Victims looking to communicate with creditors and financial institutions.
- Persons wanting to establish a repayment plan with an imposter.
- Individuals who need to report identity theft incidents to law enforcement or government agencies.
- Anyone seeking to restore their credit after identity theft issues.
How to prepare this document
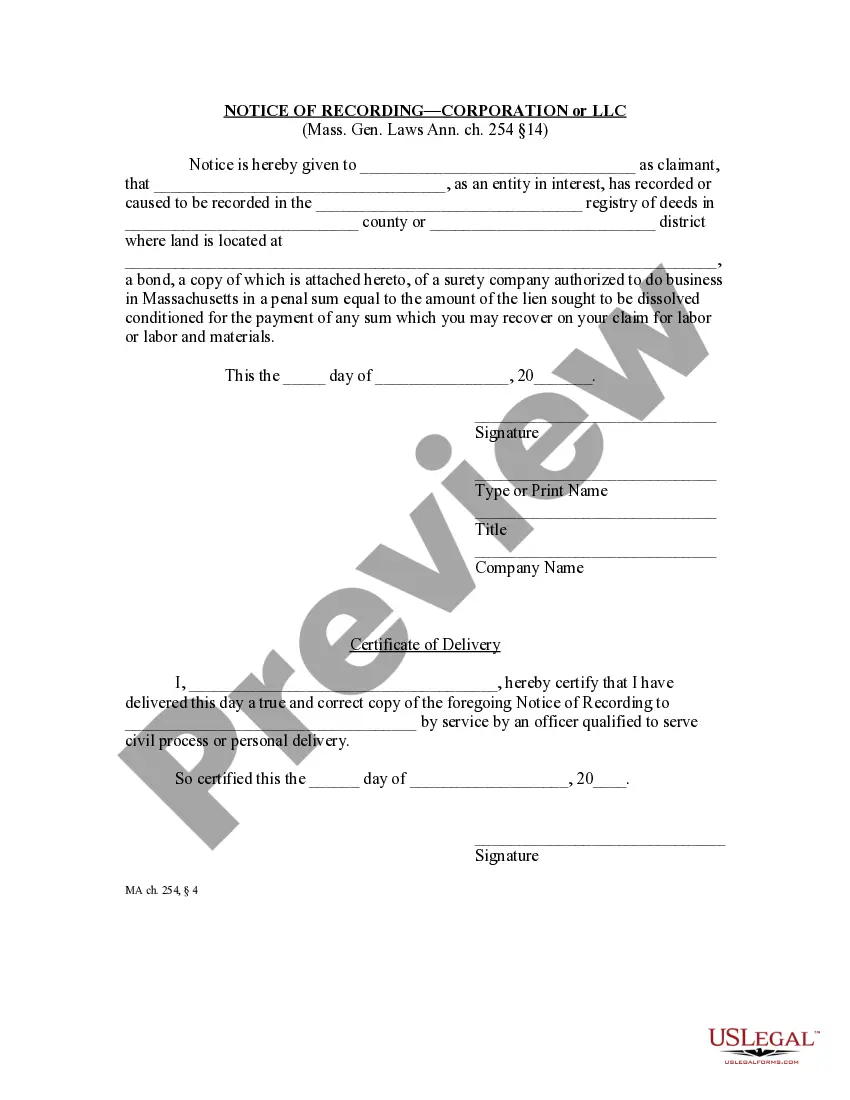
- Review all included forms carefully to understand their purpose and requirements.
- Identify the parties involved, including the imposter and relevant creditors.
- Complete the necessary forms with accurate and detailed information.
- Sign and date applicable documents as required.
- Send the completed forms to the appropriate entities, such as creditors and law enforcement, ensuring you keep copies for your records.
Notarization details for included forms
Some forms in this package need notarization to be legally binding. Our online notarization service, powered by Notarize, lets you verify and sign documents remotely through an encrypted video session, available 24/7.
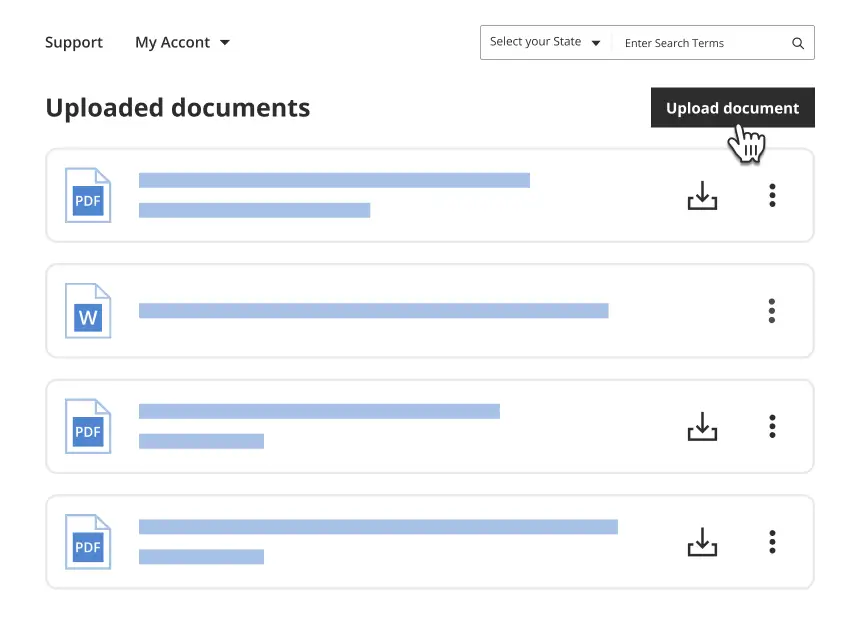
Get your form ready online
Our built-in tools help you complete, sign, share, and store your documents in one place.
Make edits, fill in missing information, and update formatting in US Legal Forms—just like you would in MS Word.
Download a copy, print it, send it by email, or mail it via USPS—whatever works best for your next step.
Sign and collect signatures with our SignNow integration. Send to multiple recipients, set reminders, and more. Go Premium to unlock E-Sign.
If this form requires notarization, complete it online through a secure video call—no need to meet a notary in person or wait for an appointment.
We protect your documents and personal data by following strict security and privacy standards.
Make edits, fill in missing information, and update formatting in US Legal Forms—just like you would in MS Word.
Download a copy, print it, send it by email, or mail it via USPS—whatever works best for your next step.
Sign and collect signatures with our SignNow integration. Send to multiple recipients, set reminders, and more. Go Premium to unlock E-Sign.
If this form requires notarization, complete it online through a secure video call—no need to meet a notary in person or wait for an appointment.
We protect your documents and personal data by following strict security and privacy standards.
Avoid these common issues
- Failing to provide complete and accurate information in forms.
- Not keeping copies of all correspondence and completed forms.
- Overlooking deadlines for reporting identity theft.
- Neglecting to follow up with creditors or agencies after submissions.
- Assuming all forms do not require signatures or notarization when applicable.
Why complete this package online
- Convenient access to legally vetted documents tailored to your needs.
- Editable forms allow you to customize documents as needed for your specific situation.
- Immediate availability for download, eliminating wait times.
- Support from licensed attorneys who draft the forms, ensuring reliability.