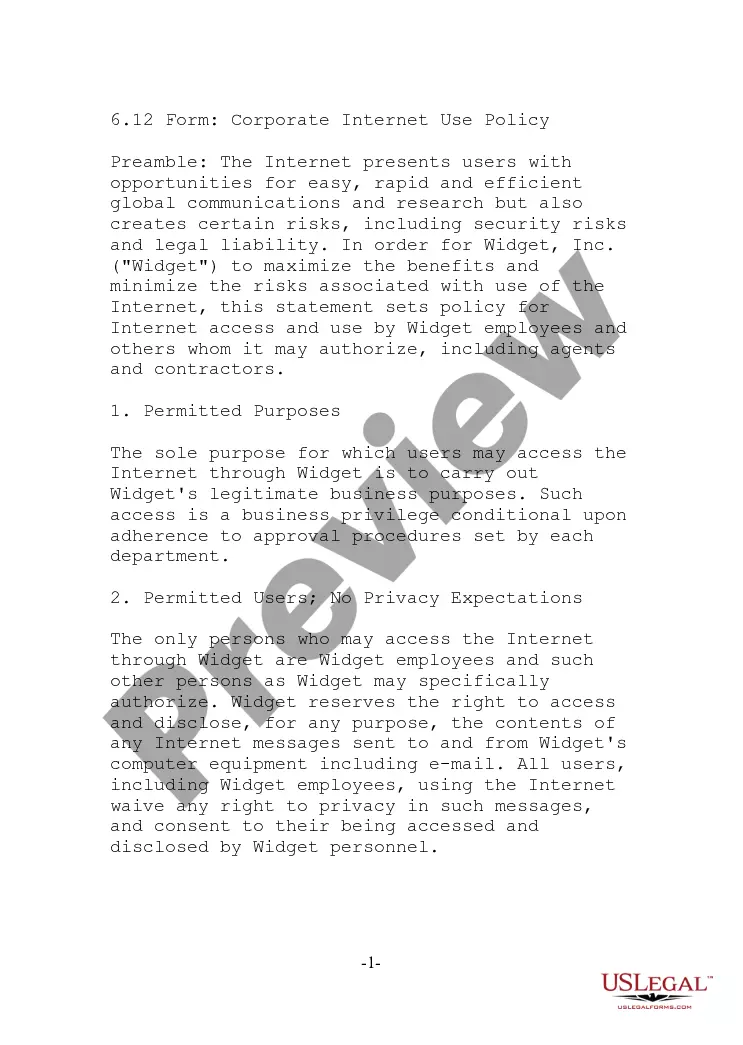
Employee Policy for Information Security
What is this form?
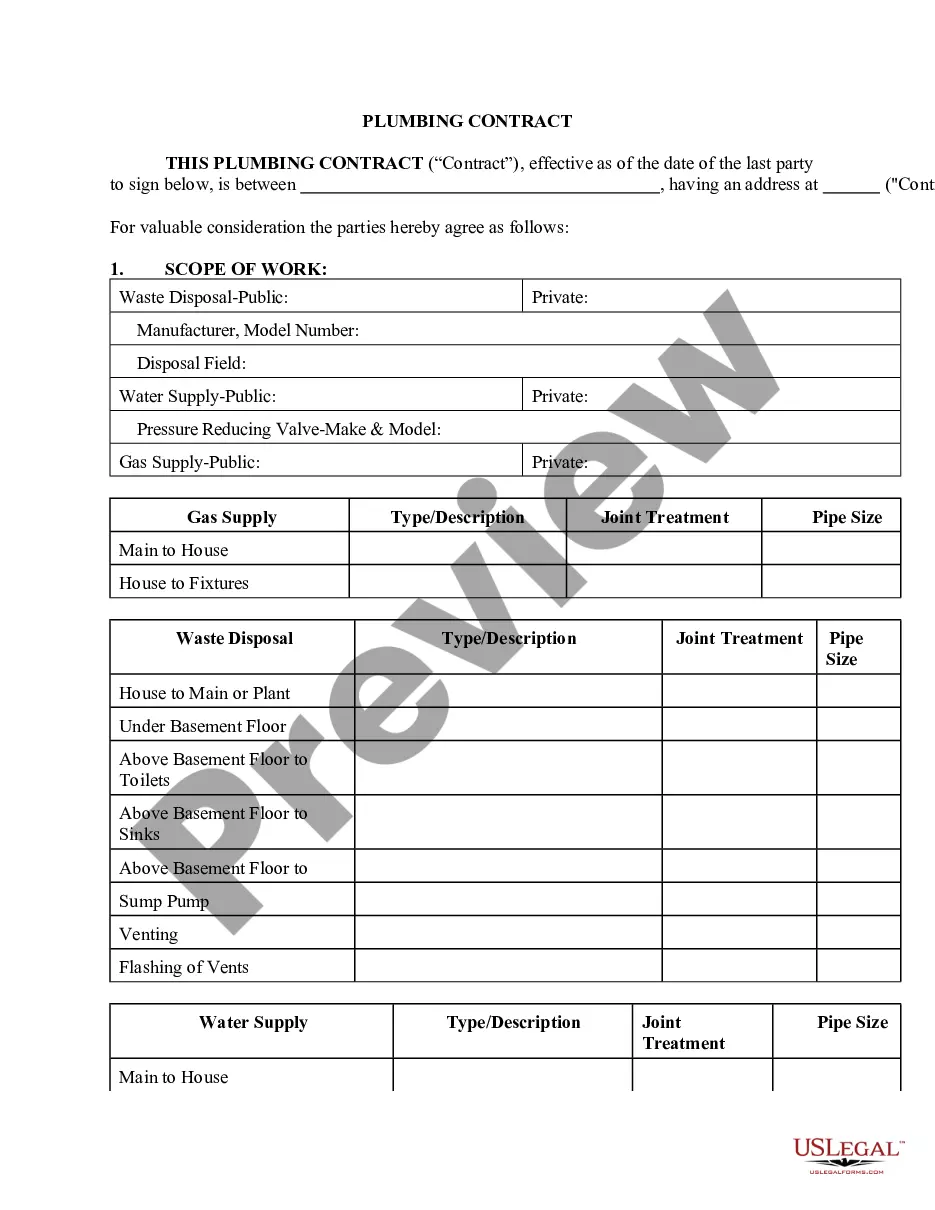
The Employee Policy for Information Security is a comprehensive document designed to safeguard a company's information assets and IT resources. This form establishes essential guidelines regarding the protection of sensitive information, including business development, employee data, and operational details. Unlike general policies, this specific employee policy emphasizes employee responsibility and roles in maintaining information security, ensuring that all team members are aware of their obligations to protect company data.
What’s included in this form
- Introduction: Importance of information security and overview of the policy's purpose.
- Scope: Applicability to all employees and information assets regardless of location or position.
- Information handling: Guidelines on managing sensitive data, including password creation and email usage.
- Adherence: Consequences of policy violations and the process for deviations.
- Definitions: Clarification of key terminology used throughout the document.
When to use this document
This form is essential when establishing or updating an organization's information security policies. It should be used during onboarding of new employees, periodic policy reviews, or when there are significant changes in information technology or business practices. Additionally, it serves as a vital reference for training sessions on security measures and protocols within the organization.
Who needs this form
Intended users of this form include:
- Human resources teams responsible for onboarding and training employees.
- Information technology departments managing data security protocols.
- Management teams ensuring compliance with security guidelines.
- All employees who need to understand their role in safeguarding sensitive company information.
How to prepare this document
- Review the document to understand its content and implications for your role.
- Complete the Employee Policy for Information Security Acceptance Agreement to confirm acknowledgment of the policy.
- Submit the signed acceptance form to your supervisor or human resources.
- Participate in any required training sessions related to information security.
- Regularly refer to the policy for guidance on handling sensitive information as part of your daily tasks.
Notarization guidance
This form does not typically require notarization unless specified by local law. It is advisable to check company policy or jurisdictional requirements for any stipulations regarding notarization.
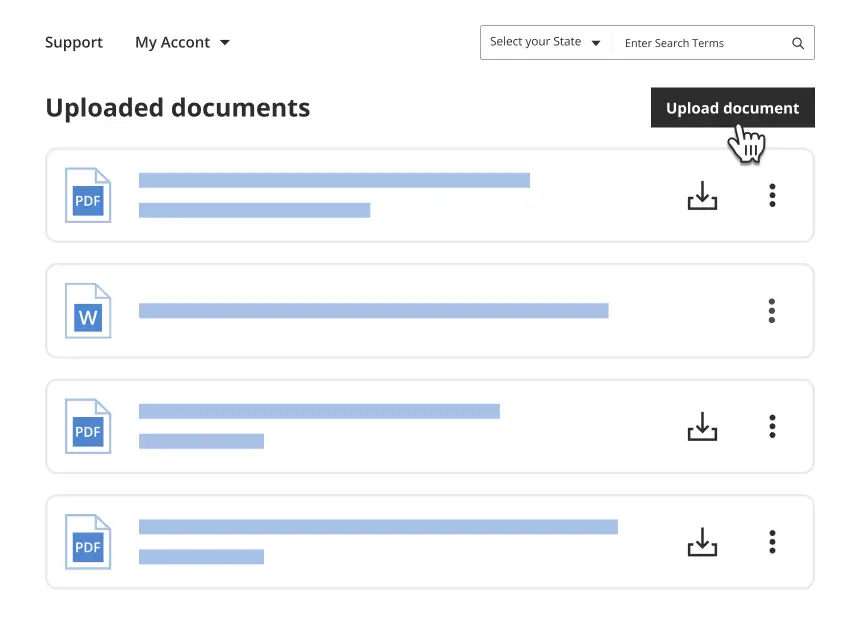
Get your form ready online
Our built-in tools help you complete, sign, share, and store your documents in one place.
Make edits, fill in missing information, and update formatting in US Legal Forms—just like you would in MS Word.
Download a copy, print it, send it by email, or mail it via USPS—whatever works best for your next step.
Sign and collect signatures with our SignNow integration. Send to multiple recipients, set reminders, and more. Go Premium to unlock E-Sign.
If this form requires notarization, complete it online through a secure video call—no need to meet a notary in person or wait for an appointment.
We protect your documents and personal data by following strict security and privacy standards.
Make edits, fill in missing information, and update formatting in US Legal Forms—just like you would in MS Word.
Download a copy, print it, send it by email, or mail it via USPS—whatever works best for your next step.
Sign and collect signatures with our SignNow integration. Send to multiple recipients, set reminders, and more. Go Premium to unlock E-Sign.
If this form requires notarization, complete it online through a secure video call—no need to meet a notary in person or wait for an appointment.
We protect your documents and personal data by following strict security and privacy standards.
Avoid these common issues
- Failing to sign the acceptance agreement, leading to confusion about security responsibilities.
- Not regularly reviewing the policy, which may result in outdated practices.
- Ignoring specific sections regarding handling sensitive information, potentially leading to security breaches.
Advantages of online completion
- Convenience: Easily accessible for download and distribution to employees.
- Editability: Tailor the policy to meet specific organizational needs and practices.
- Reliability: Contains expert-drafted content that adheres to relevant legal standards.
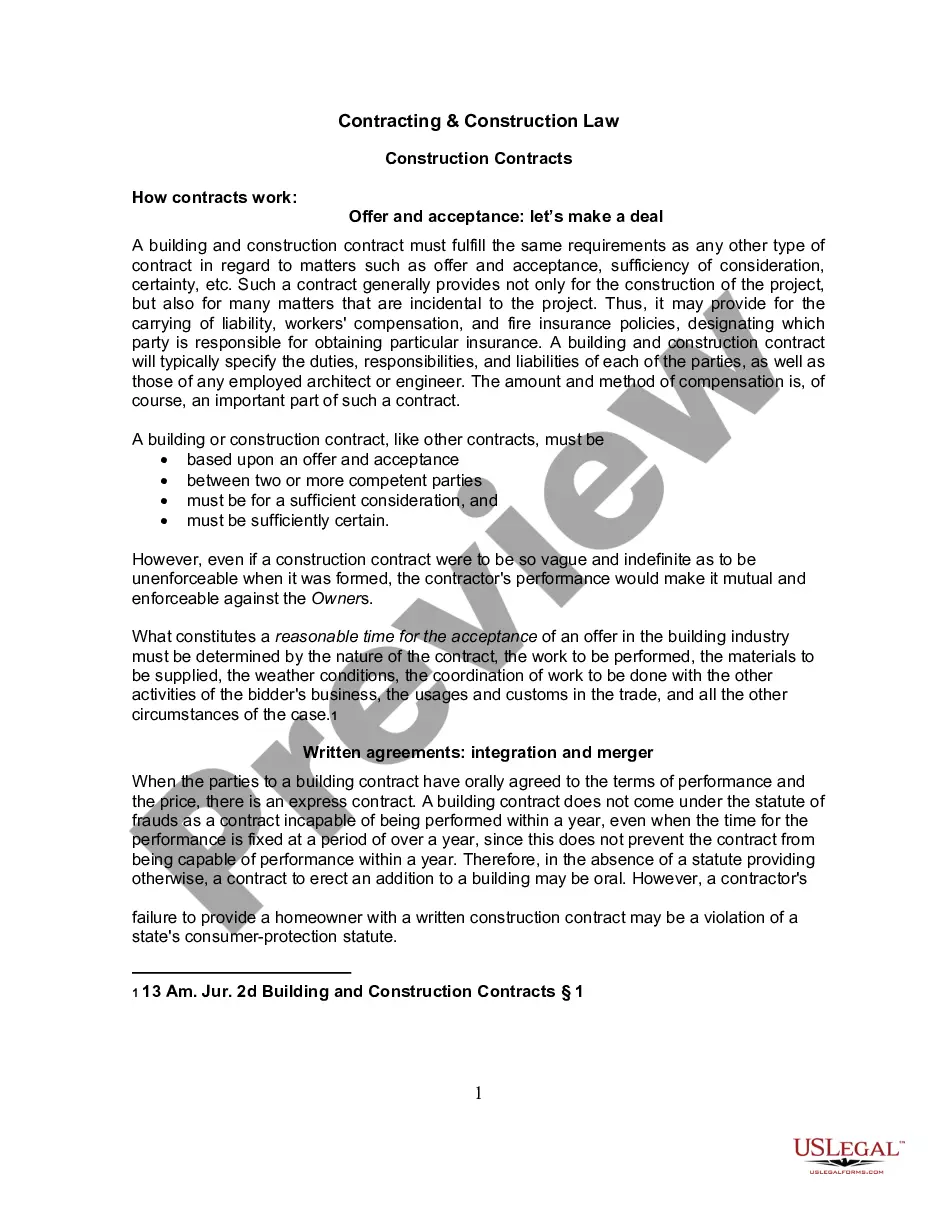
Legal use & context
The Employee Policy for Information Security is legally binding once implemented and acknowledged by employees. It serves to establish clear responsibilities and expectations regarding the handling of sensitive information, thereby mitigating legal liabilities. Adherence to this policy is critical for business operations to ensure compliance with local and federal regulations governing data protection.
- All employees are responsible for adhering to the Employee Policy for Information Security.
- Understanding the types of information that need protection is crucial for compliance.
- Regular training and updates are essential to maintain security awareness among staff.
- Information assets: Hardware and software used to store and process company data.
- Sensitive information: Data that must be protected to prevent unauthorized access.
- Computing devices: Any device used for processing information, including PCs and laptops.
Looking for another form?
Form popularity
FAQ
Purpose. First state the purpose of the policy which may be to: Audience. Information security objectives. Authority and access control policy. Data classification. Data support and operations. Security awareness and behavior. Responsibilities, rights, and duties of personnel.
Identify your risks. What are your risks from inappropriate use? Learn from others. Make sure the policy conforms to legal requirements. Level of security = level of risk. Include staff in policy development. Train your employees. Get it in writing. Set clear penalties and enforce them.
1Purpose.2Audience.3Information security objectives.4Authority and access control policy.5Data classification.6Data support and operations.7Security awareness training.8Responsibilities and duties of employees.What is an Information Security Policy? UpGuard\nwww.upguard.com > blog > information-security-policy
1Provide information security direction for your organisation;2Include information security objectives;3Include information on how you will meet business, contractual, legal or regulatory requirements; and.How to write an information security policy with template example\nwww.itgovernance.eu > blog > how-to-write-an-information-security-polic...
The fundamental principles (tenets) of information security are confidentiality, integrity, and availability. Every element of an information security program (and every security control put in place by an entity) should be designed to achieve one or more of these principles. Together, they are called the CIA Triad.
Information security policy is a set of policies issued by an organization to ensure that all information technology users within the domain of the organization or its networks comply with rules and guidelines related to the security of the information stored digitally at any point in the network or within the
A security policy is a written document in an organization outlining how to protect the organization from threats, including computer security threats, and how to handle situations when they do occur. A security policy must identify all of a company's assets as well as all the potential threats to those assets.
It relies on five major elements: confidentiality, integrity, availability, authenticity, and non-repudiation.
It needs to define the framework for setting information security objectives basically, the policy needs to define how the objectives are proposed, how they are approved, and how they are reviewed. See also: ISO 27001 control objectives Why are they important?