Internet Use Policy
Understanding this form
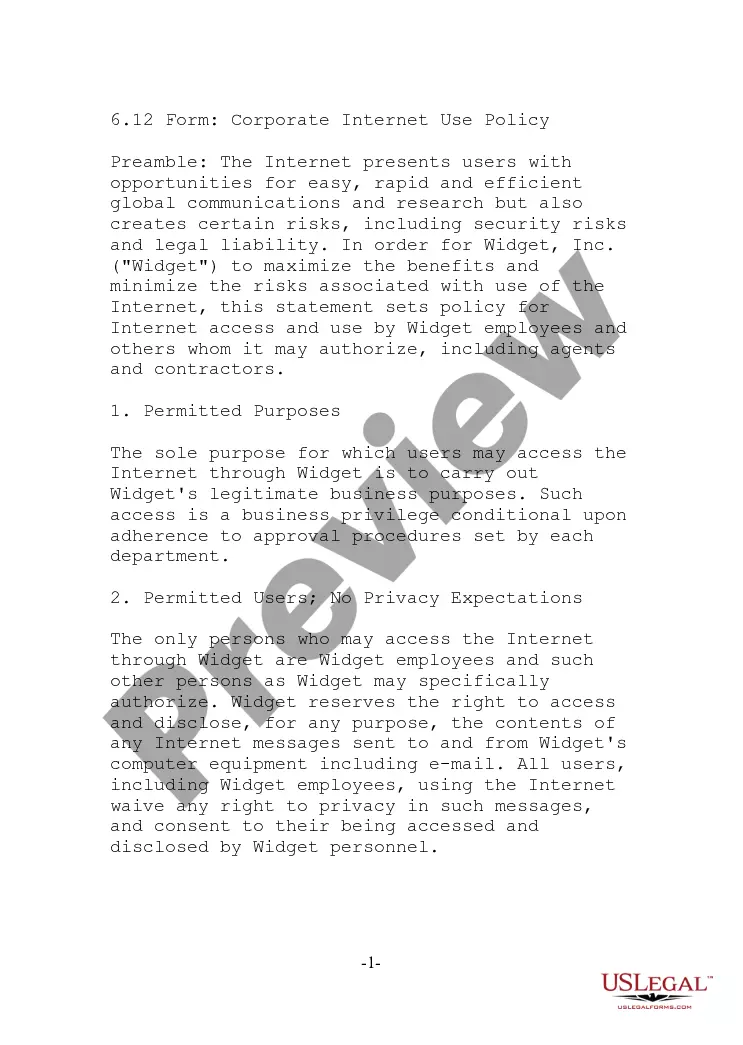
The Internet Use Policy is a legal agreement that outlines the acceptable use of the internet by employees while they are at work. This policy is crucial for defining the boundaries of personal and professional internet use, ensuring that employees understand that internet access is a privilege that can be revoked for inappropriate use. By signing this form, employees acknowledge their responsibilities regarding internet access and which activities are deemed unacceptable in a workplace setting.
Key parts of this document
- Definition of acceptable and unacceptable internet use.
- Consequences of inappropriate internet usage, including potential disciplinary action.
- Network etiquette guidelines to maintain professionalism while using the company network.
- Indemnification clause detailing employee responsibility for any legal issues arising from policy violations.
- Instructions for reporting security issues to network administrators.
When to use this document
This form is typically used when a company implements or updates its internet policies for employees. It is essential when onboarding new staff, revising current policies, or in response to internet misuse incidents. Employers must ensure that all employees sign the Internet Use Policy to protect their organization and maintain a professional work environment.
Who needs this form
- Employers looking to define internet use policies for employees.
- Human resources personnel responsible for onboarding and employee compliance.
- Team leaders or managers who need to enforce internet usage across their teams.
How to prepare this document
- Clearly state the employee's name and position on the form.
- Review the acceptable and unacceptable uses outlined in the policy.
- Have the employee read the entire agreement carefully.
- Ensure the employee signs and dates the form to acknowledge understanding and acceptance.
- File the signed agreement in the employee's personnel record for future reference.
Does this document require notarization?
This form does not typically require notarization unless specified by local law. Ensure compliance with state regulations, but most companies simply collect signed copies for their records.
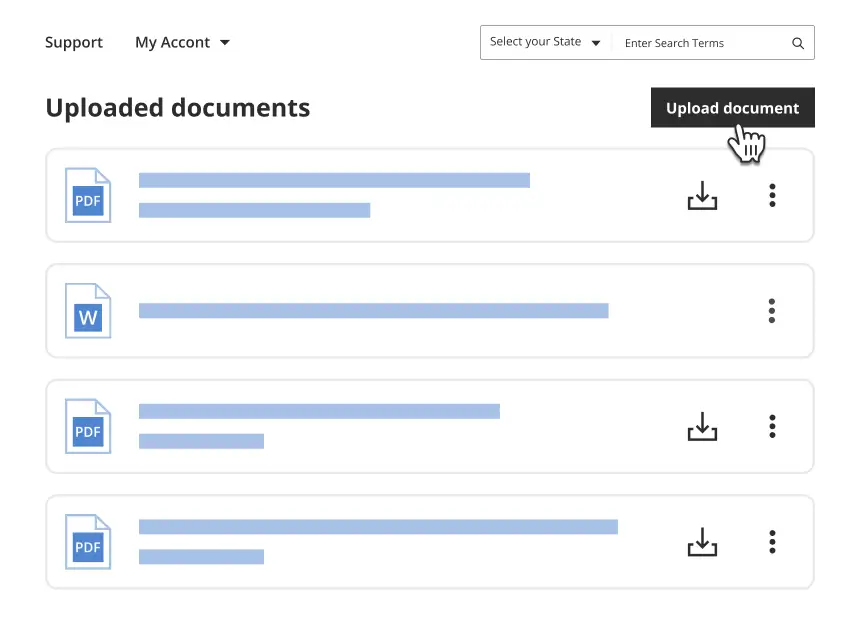
Get your form ready online
Our built-in tools help you complete, sign, share, and store your documents in one place.
Make edits, fill in missing information, and update formatting in US Legal Forms—just like you would in MS Word.
Download a copy, print it, send it by email, or mail it via USPS—whatever works best for your next step.
Sign and collect signatures with our SignNow integration. Send to multiple recipients, set reminders, and more. Go Premium to unlock E-Sign.
If this form requires notarization, complete it online through a secure video call—no need to meet a notary in person or wait for an appointment.
We protect your documents and personal data by following strict security and privacy standards.
Make edits, fill in missing information, and update formatting in US Legal Forms—just like you would in MS Word.
Download a copy, print it, send it by email, or mail it via USPS—whatever works best for your next step.
Sign and collect signatures with our SignNow integration. Send to multiple recipients, set reminders, and more. Go Premium to unlock E-Sign.
If this form requires notarization, complete it online through a secure video call—no need to meet a notary in person or wait for an appointment.
We protect your documents and personal data by following strict security and privacy standards.
Avoid these common issues
- Failing to provide a clear explanation of unacceptable uses before asking employees to sign.
- Not keeping signed documents on file for future reference.
- Neglecting to update the policy as technology and legal requirements evolve.
Why complete this form online
- Convenience of downloading and printing the form as needed.
- Quick access to updates when organizational policies change.
- Ability to tailor the policy for specific workplace requirements easily.
Legal use & context
- The Internet Use Policy is a legally binding document that helps protect the company's assets and maintain a disciplined work environment.
- This policy can be enforced through disciplinary measures if employees violate the terms outlined in the agreement.
- Clear documentation of internet usage policies can aid in defending the company against potential legal claims related to internet misuse.
Summary of main points
- Establishes clear guidelines for acceptable and unacceptable internet use in the workplace.
- Helps protect company resources and maintain professionalism among employees.
- Signed agreement is legally binding and indicates understanding of the policy.
- Should be used during onboarding and updated as necessary to reflect current practices.
Looking for another form?
Form popularity
FAQ
A computer usage policy is a document that provides employees with guidelines on how to appropriately use company equipment and the internet on your work computer network.This kind of policy can minimize the risk of computer misuse whether in the university library or a business office.
Home User. In an increasing number of homes, the computer is a basic necessity. Small Office/Home Office User. Computer assist small business and home office users in managing their resources effectively. Mobile User. Power User. Enterprise User.
A computer security policy defines the goals and elements of an organization's computer systems.Security policies are enforced by organizational policies or security mechanisms. A technical implementation defines whether a computer system is secure or insecure.
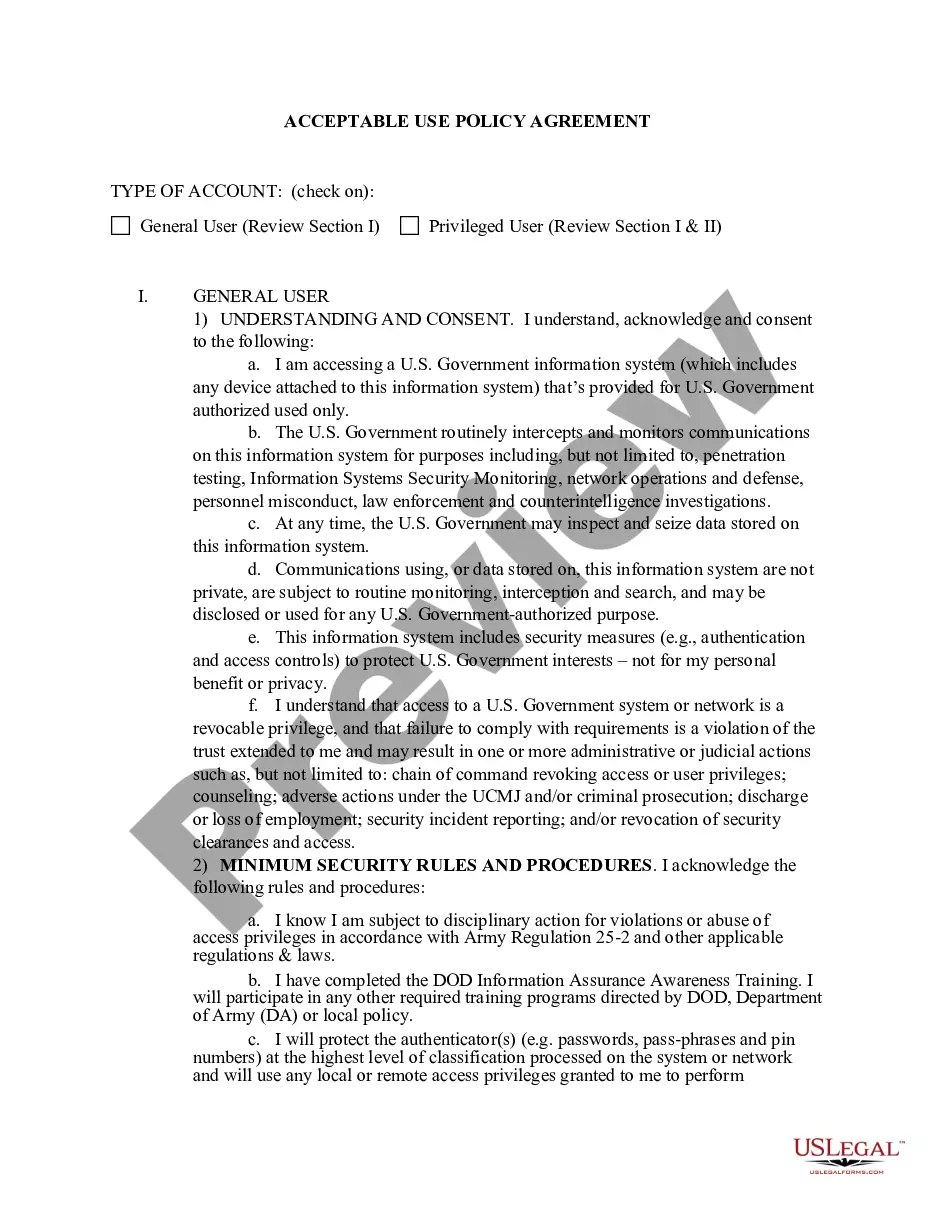
An acceptable use policy (AUP) is a document stipulating constraints and practices that a user must agree to for access to a corporate network or the Internet. Many businesses and educational facilities require that employees or students sign an acceptable use policy before being granted a network ID.
A preamble, a definition section, a policy statement, an acceptable uses section, an unacceptable uses section, and. a violations/sanctions section.
An acceptable use policy (AUP) is a document stipulating constraints and practices that a user must agree to for access to a corporate network or the Internet.Not attempting to break the security of any computer network or user. Not posting commercial messages to Usenet groups without prior permission.
An Acceptable Use Policy is a series of rules that define what end users may or may not do with their technology. Usually, this policy requires some kind of acknowledgment that the rules are well understood, including potential consequences of violation, before issuing any kind of log into the system.
Encryption policies not be part of an acceptable use policy.