Computer Fraud: Causing Damage to Computer or Program
What is this form?
The Computer Fraud: Causing Damage to Computer or Program form outlines the legal parameters surrounding the federal crime of intentionally transmitting harmful programs, codes, or commands to a protected computer system. This form is essential for understanding the specific legal requirements and conditions under which someone can be held liable for computer-related fraud, distinguishing it from other types of fraud and computer offenses.
Key parts of this document
- Definition of a "protected computer" and its significance in legal contexts.
- Criteria for proving guilt, including intent and resulting damages.
- Details on what constitutes "damage" to a computer or program.
- Clarification of terms like "interstate commerce" and "foreign commerce".
- Specifications on the minimum loss value for prosecuting damages.
Common use cases
This form is utilized in scenarios where an individual or entity has experienced damages due to unauthorized and harmful transmissions to their computer systems. It is pertinent in cases involving cybercrimes, particularly where significant financial loss or threats to public safety occurred. This form serves as a legal guide for prosecution or defense in cases involving computer fraud.
Who can use this document
Individuals or entities who should consider using this form include:
- Prosecutors seeking to bring charges against individuals accused of computer fraud.
- Defense attorneys representing individuals charged with causing damage to computer systems.
- IT professionals or organizations that have suffered attacks or damages from harmful code.
- Victims of cybercrime who need to understand legal implications and steps to take.
How to complete this form
- Identify the defendant and the protected computer involved.
- Document the harmful program, information, code, or command that was transmitted.
- Specify the intent of the defendant and how it relates to unauthorized access.
- Provide details of the damage that resulted, including financial losses or impacts on health.
- Ensure all criteria for proving guilt are supported by evidence.
Notarization requirements for this form
This form does not typically require notarization unless specified by local law. However, it's always advisable to check any jurisdiction-specific rules that may apply when filing legal documents.
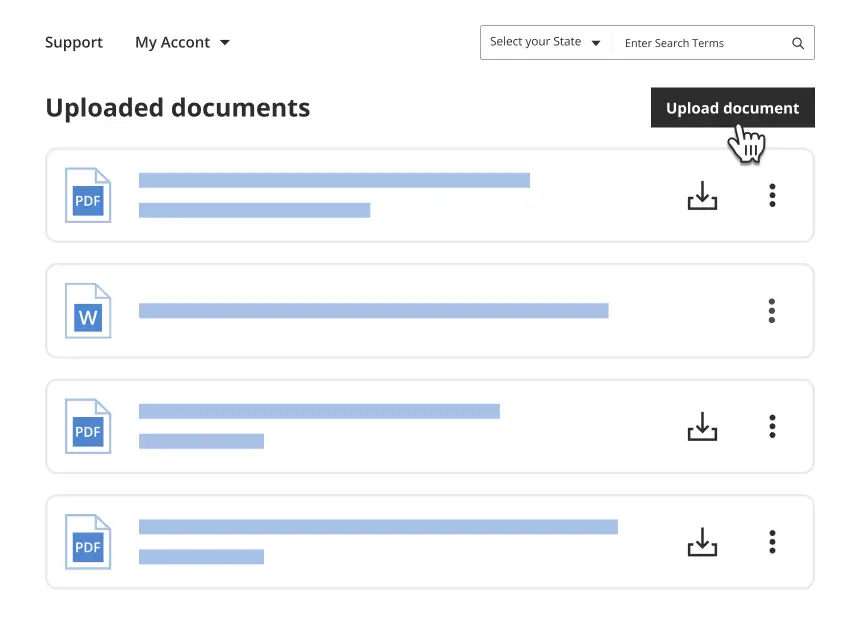
Get your form ready online
Our built-in tools help you complete, sign, share, and store your documents in one place.
Make edits, fill in missing information, and update formatting in US Legal Forms—just like you would in MS Word.
Download a copy, print it, send it by email, or mail it via USPS—whatever works best for your next step.
Sign and collect signatures with our SignNow integration. Send to multiple recipients, set reminders, and more. Go Premium to unlock E-Sign.
If this form requires notarization, complete it online through a secure video call—no need to meet a notary in person or wait for an appointment.
We protect your documents and personal data by following strict security and privacy standards.
Make edits, fill in missing information, and update formatting in US Legal Forms—just like you would in MS Word.
Download a copy, print it, send it by email, or mail it via USPS—whatever works best for your next step.
Sign and collect signatures with our SignNow integration. Send to multiple recipients, set reminders, and more. Go Premium to unlock E-Sign.
If this form requires notarization, complete it online through a secure video call—no need to meet a notary in person or wait for an appointment.
We protect your documents and personal data by following strict security and privacy standards.
Common mistakes to avoid
- Failing to adequately document all instances of unauthorized access.
- Overlooking the requirement to prove intent and knowledge of wrongdoing.
- Neglecting to provide detailed evidence of the damages incurred.
- Misunderstanding the definitions of terms such as "protected computer".
Why use this form online
- Convenient access to legal templates drafted by licensed attorneys.
- Edit and customize the document to fit your specific circumstances.
- Ability to download and save your completed form for your records.
- Guidance through each step of the form-filling process.
Legal use & context
- This form serves as a foundational guideline for federal prosecutions involving computer fraud.
- Understand that state laws may vary, but the federal definition of computer fraud is consistent.
- Awareness of the legal definitions can help in accurately assessing damages and possible penalties.
Key takeaways
- The Computer Fraud form is crucial for understanding federal laws surrounding computer-related crimes.
- Proving intent and damage is essential for a successful legal case.
- Utilize this form to document occurrences of cyber fraud accurately and systematically.
Looking for another form?
Form popularity
FAQ
Cybercrime is criminal activity that either targets or uses a computer, a computer network or a networked device. Most cybercrime is committed by cybercriminals or hackers who want to make money. However, occasionally cybercrime aims to damage computers or networks for reasons other than profit.
Emails attempting to gather personal information such as account numbers, Social Security numbers, and passwords; also known as phishing. Using someone else's computer to access personal information with the intent to use it fraudulently.
Cyber-bullying, hacking, identity theft, and even using a work PC for personal business are all examples of computer abuse. While not always enforced, acts that constitute computer abuse was codified in the 1984 Computer Fraud and Abuse Act (CFAA) which is enforceable at the federal level.
The Computer Fraud and Abuse Act, 18 U.S.C. §1030 (the CFAA), imposes criminal and civil liability on individuals who access a computer without authorization or exceed authorized access.
The Computer Fraud and Abuse Act of 1986 makes it a crime for anyone to access without authorization a computer or computer system used by a financial institution, US government agency, or any organization or individual involved in interstate or foreign commerce or communication.
The CFAA prohibits intentionally accessing a computer without authorization or in excess of authorization, but fails to define what ?without authorization? means.
Computer abuse refers to a broad category of activities wherein a computer is used to improperly or illegally cause harm to somebody else or their property. Cyber-bullying, hacking, identity theft, and even using a work PC for personal business are all examples of computer abuse.
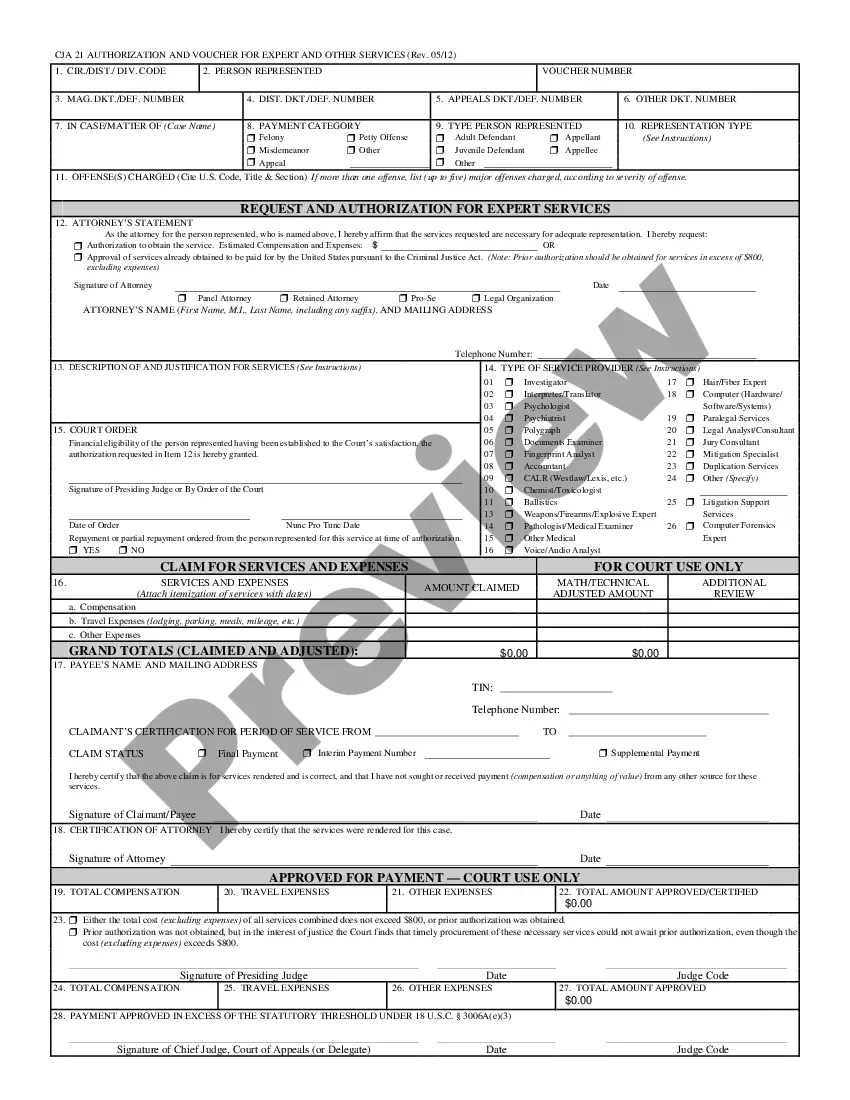
Provisions of the Computer Fraud & Abuse Act 18 U.S.C. § 1030 OffenseSectionAccessing a Computer and Obtaining Information(a)(2)Trespassing in a Government Computer(a)(3)Accessing a Computer to Defraud and Obtain Value(a)(4)Intentionally Damaging by Knowing Transmission(a)(5)(A)6 more rows