Michigan Identity Theft by Known Imposter Package
About this form package
The Michigan Identity Theft by Known Imposter Package includes essential forms for individuals whose identity has been stolen by someone they know. This package is specifically designed to facilitate communication between victims and creditors, as well as other entities involved in addressing the fallout of identity theft. Unlike general identity theft packages, this one specifically targets scenarios where the imposter is known to the victim, providing tailored solutions for resolution.
What’s included in this form package
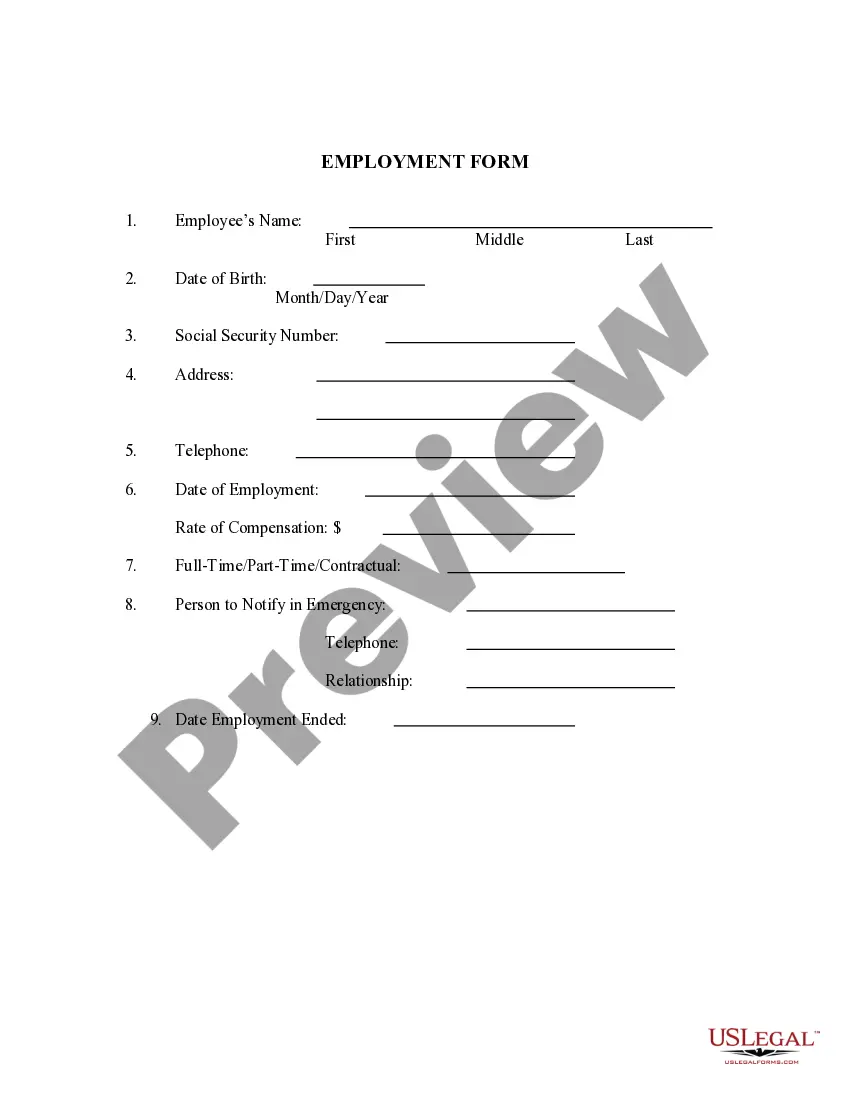
- Federal Trade Commission Affidavit regarding Identity Theft
- Identity Theft Contact Table
- Identity Theft Checklist
- Sample Letter to Report False Submission of Information
- Guide for Identity Theft Victims Who Know Their Imposter
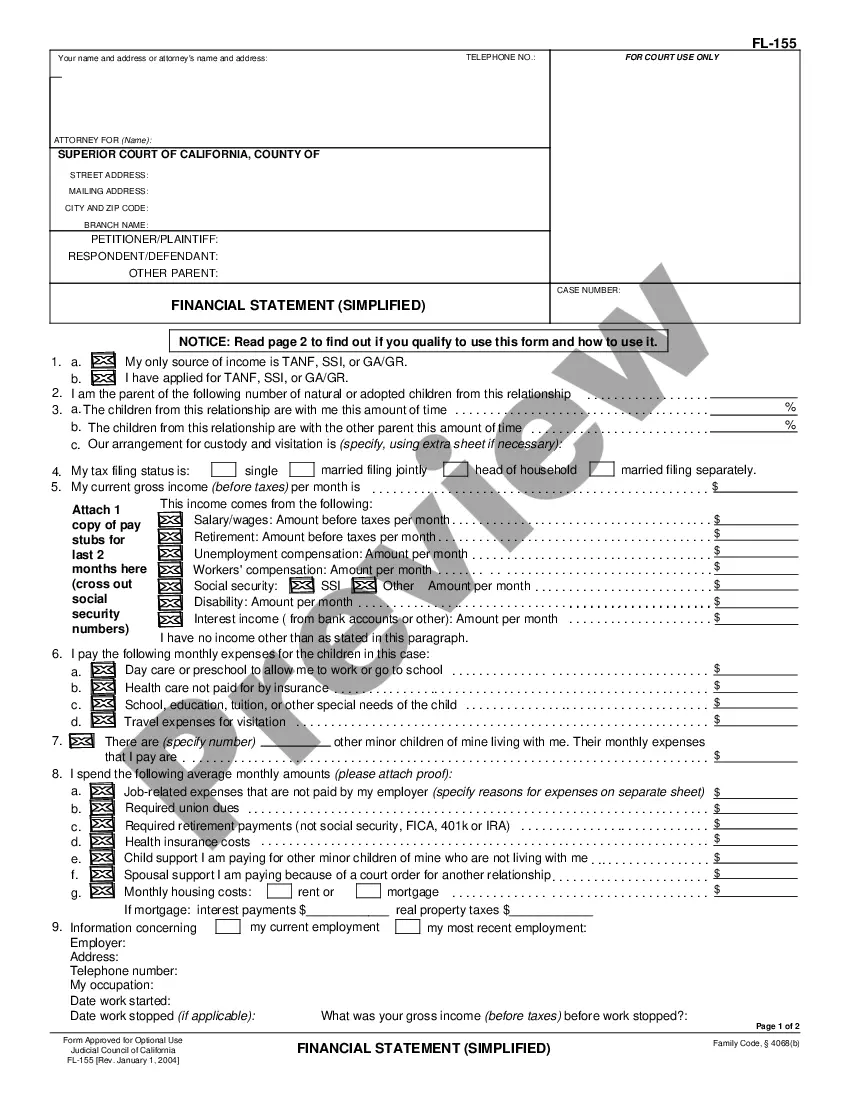
- Letter from Identity Theft Victim to Credit Issuer Regarding Known Imposter Identity Theft
- Letter from Known Imposter to Creditor Accepting Responsibility for Accounts, Charges or Debits
- Letter Agreement Between Known Imposter and Victim to Work Out Repayment Plan
- Letter to Law Enforcement to Report Identity Theft by Known Imposter
- Letter to Credit Reporting Company or Bureau Regarding Known Imposter Identity Theft
- Letter to Report Known Imposter Identity Theft to Postal Authorities
- Letter to Report Known Imposter Identity Theft to Social Security Administration
- Letter to Report Known Imposter Identity Theft to Other Entities
- Sample Letter for Request for Free Credit Report Allowed by Federal Law
Situations where these forms applies
This package is ideal for use when:
- You discover that someone you know has used your identity to open accounts or incur debts.
- You need to communicate with creditors and credit reporting agencies to dispute fraudulent charges.
- You wish to report the identity theft to law enforcement or postal authorities.
- You want to establish a repayment plan or agreement with the known imposter.
Who needs this form package
- Individuals who have been victims of identity theft by someone they know.
- Those seeking to clear their name from debts incurred by a known imposter.
- Anyone needing to communicate officially with creditors or law enforcement regarding identity theft cases.
Completing these forms step by step
- Review the included guide for identity theft victims to understand your rights and steps.
- Complete the Identity Theft Checklist to document all relevant details and steps taken.
- Fill out the needed letters to creditors and law enforcement, ensuring all information is accurate.
- Use the Identity Theft Contact Table to organize and track communications with all relevant parties.
- Sign and date your forms as required before submitting them to the appropriate organizations.
Do documents in this package require notarization?
Notarization is required for one or more forms in this package. US Legal Forms provides secure online notarization powered by Notarize, allowing you to complete the process through a verified video call.
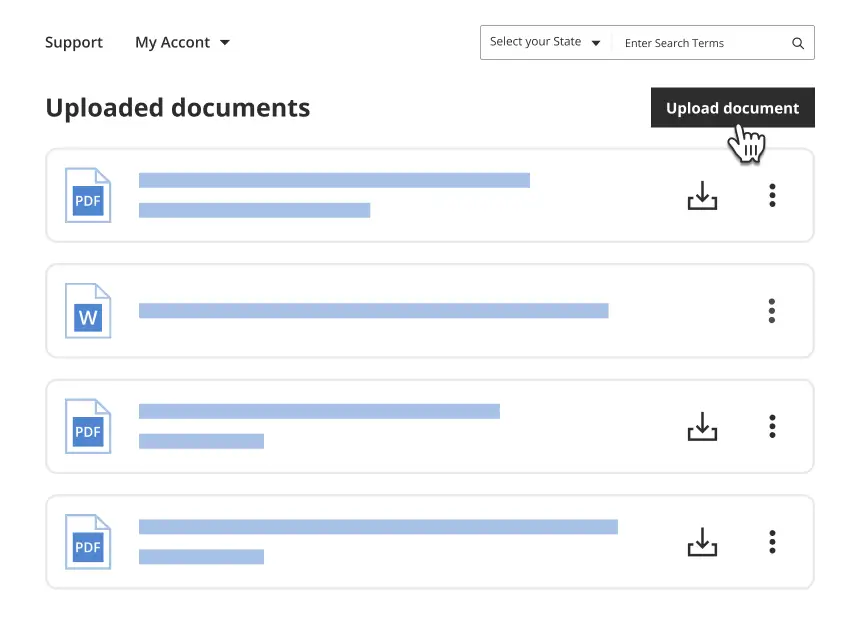
Get your form ready online
Our built-in tools help you complete, sign, share, and store your documents in one place.
Make edits, fill in missing information, and update formatting in US Legal Forms—just like you would in MS Word.
Download a copy, print it, send it by email, or mail it via USPS—whatever works best for your next step.
Sign and collect signatures with our SignNow integration. Send to multiple recipients, set reminders, and more. Go Premium to unlock E-Sign.
If this form requires notarization, complete it online through a secure video call—no need to meet a notary in person or wait for an appointment.
We protect your documents and personal data by following strict security and privacy standards.
Make edits, fill in missing information, and update formatting in US Legal Forms—just like you would in MS Word.
Download a copy, print it, send it by email, or mail it via USPS—whatever works best for your next step.
Sign and collect signatures with our SignNow integration. Send to multiple recipients, set reminders, and more. Go Premium to unlock E-Sign.
If this form requires notarization, complete it online through a secure video call—no need to meet a notary in person or wait for an appointment.
We protect your documents and personal data by following strict security and privacy standards.
Mistakes to watch out for
- Failing to document communications with creditors, which can hinder your case.
- Not providing enough detail in the letters, leading to delays in resolution.
- Overlooking to notify all relevant entities, such as credit bureaus and law enforcement.
Why use this package online
- Convenience of downloading forms at any time.
- Editable documents that allow for customization according to your specific situation.
- Reliable templates drafted by licensed attorneys to ensure legal validity.
Main things to remember
- The Michigan Identity Theft by Known Imposter Package is essential for those dealing with identity theft by acquaintances.
- The package provides a comprehensive set of tools for effective communication with creditors and authorities.
- Proper completion and documentation are vital to resolving issues related to identity theft efficiently.
Looking for another form?
Form popularity
FAQ
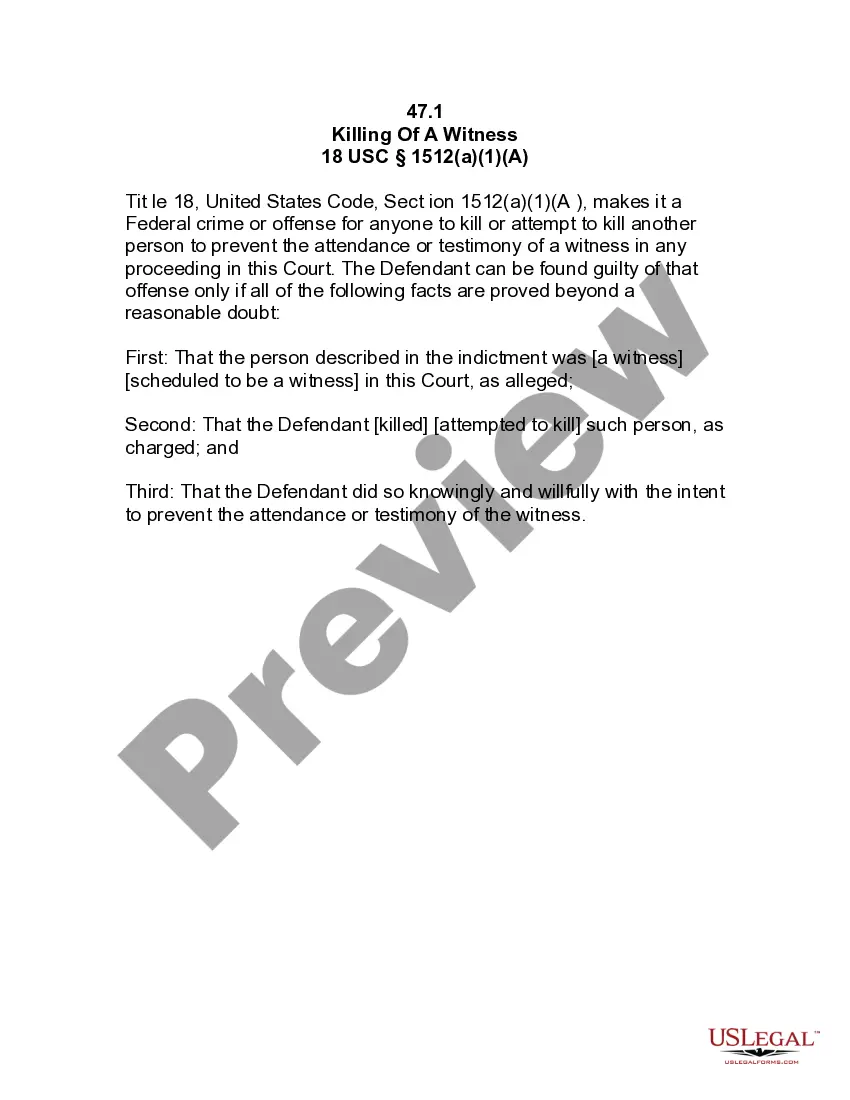
Proving identity theft can often be challenging, but it is not impossible. The difficulty lies in collecting the right evidence and demonstrating clear patterns of misuse of your identity. The Michigan Identity Theft by Known Imposter Package simplifies this process by helping you identify what materials you need to compile, making it easier for you to present your case effectively. When you are organized and methodical in your approach, you increase your chances of successfully proving identity theft.
In cases of identity theft, you’ll need various forms of evidence to substantiate your claim. Essential documents include bank statements displaying unauthorized transactions, credit reports indicating unfamiliar accounts, and any communication with financial institutions regarding fraudulent activity. Utilizing the Michigan Identity Theft by Known Imposter Package can streamline the process of collecting and organizing your evidence, ensuring you present a comprehensive case to the authorities.
Writing an identity theft statement involves clearly detailing the circumstances of the theft and how it has impacted you. Start by outlining your personal information, the actions taken by the imposter, and any financial losses you've experienced. Be concise, yet thorough, in your description. Using the Michigan Identity Theft by Known Imposter Package can simplify this process, providing you with a structured approach to create a strong statement.
You need to fill out the identity theft affidavit form designed specifically for your situation. This form documents the details of the identity theft incident and is essential for any legal claims. It's important to provide all relevant information to ensure your case is strong. Consider using the Michigan Identity Theft by Known Imposter Package as it offers the necessary forms and guidance for your situation.
Yes, you should fill out an identity theft affidavit if you believe you are a victim of identity theft. This affidavit serves as a formal declaration that your identity was used without your permission. By completing this form, you can take important steps to protect your financial future and support your claims. The Michigan Identity Theft by Known Imposter Package will help guide you through this process.
Falsely claiming identity theft can lead to serious consequences, including potential legal action or penalties. It may damage your reputation and affect your financial standing. If you face such a situation, the Michigan Identity Theft by Known Imposter Package can assist you in navigating the complexities of identity theft claims and help you establish your genuine case.
You can verify if you are a victim of identity theft by reviewing your credit reports regularly, monitoring your financial statements, and looking for unusual activity. It's essential to act promptly if you notice any discrepancies, as this could indicate that someone is misusing your information. The Michigan Identity Theft by Known Imposter Package includes resources that guide you through the process of monitoring and protecting your identity.
To ensure compliance with the Red Flag rule, your identity theft prevention program must include risk assessment, policies for detecting warning signs, written procedures for responding to red flags, and a program evaluation process. Focusing on these aspects can help protect you from identity theft. The Michigan Identity Theft by Known Imposter Package is designed to help you establish and maintain such a program effectively.