Ethical Hacking Agreement for External Network Security - Unannounced Penetration Test
Overview of this form
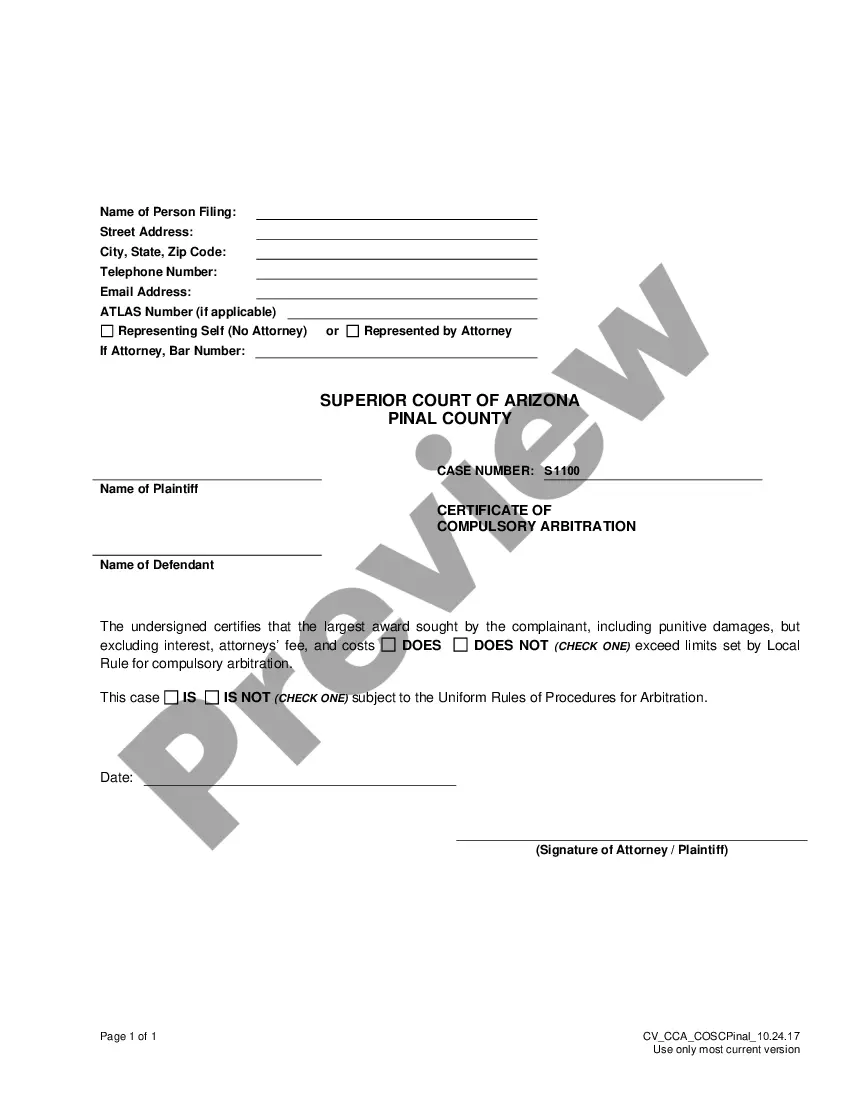
The Ethical Hacking Agreement for External Network Security - Unannounced Penetration Test is a legal document that facilitates a consultant's evaluation of a company's computer security systems without prior notice. This form outlines the terms and conditions under which the consultant will conduct penetration testing to discover vulnerabilities, allowing the company to mitigate security risks. Unlike other agreements, this contract specifically caters to ethical hacking contexts, ensuring that both parties understand the scope and legality of the testing process.
Main sections of this form
- Date and parties involved: Basic information about the consultant and the company.
- Services to be performed: Detailed description of the penetration testing services and associated fees.
- Confidentiality obligations: Clauses ensuring that sensitive information remains protected.
- Status of the consultant: Clarification that the consultant acts as an independent contractor.
- Resolution of disputes: Provision for arbitration in case of disagreements related to the agreement.
- Governing law: Specifies which stateâs laws will apply to the agreement.
Common use cases
This form should be used when a company hires an external consultant to conduct an unannounced penetration test of its network security. This might occur in various scenarios, such as when a company wants to identify potential security weaknesses before a data breach occurs, when fulfilling regulatory compliance requirements, or when the company is proactively seeking to improve its cybersecurity posture.
Who should use this form
This form is intended for:
- Businesses and organizations looking to test their cybersecurity defenses.
- IT professionals and security consultants offering penetration testing services.
- Legal teams overseeing compliance and risk management within their organizations.
Instructions for completing this form
- Identify the parties: Fill in the names and addresses of the consultant and the company.
- Specify the services: Clearly outline the type of penetration testing to be performed.
- Set the fees: Indicate the hourly rate for the consultantâs services and the payment terms.
- Define hours and location: Note where the services will be performed and the expected hours of work.
- Sign the agreement: Ensure both parties review and sign the document to make it legally binding.
Does this document require notarization?
This form does not typically require notarization unless specified by local law. However, obtaining notarization can enhance the documentâs authenticity and acceptance, especially in legal proceedings.
Get your form ready online
Our built-in tools help you complete, sign, share, and store your documents in one place.
Make edits, fill in missing information, and update formatting in US Legal Forms—just like you would in MS Word.
Download a copy, print it, send it by email, or mail it via USPS—whatever works best for your next step.
Sign and collect signatures with our SignNow integration. Send to multiple recipients, set reminders, and more. Go Premium to unlock E-Sign.
If this form requires notarization, complete it online through a secure video call—no need to meet a notary in person or wait for an appointment.
We protect your documents and personal data by following strict security and privacy standards.
Make edits, fill in missing information, and update formatting in US Legal Forms—just like you would in MS Word.
Download a copy, print it, send it by email, or mail it via USPS—whatever works best for your next step.
Sign and collect signatures with our SignNow integration. Send to multiple recipients, set reminders, and more. Go Premium to unlock E-Sign.
If this form requires notarization, complete it online through a secure video call—no need to meet a notary in person or wait for an appointment.
We protect your documents and personal data by following strict security and privacy standards.
Common mistakes
- Failing to clearly specify the scope of the penetration test, leading to misunderstandings about what is included.
- Omitting important terms regarding confidentiality and data protection.
- Not including the governing law, which can affect the enforceability of the agreement.
- Neglecting to include payment terms, which can lead to disputes over compensation.
Benefits of using this form online
- Convenience: Downloadable format allows for easy access and completion at any time.
- Editability: Customizable fields let users tailor the agreement to specific needs and circumstances.
- Reliability: Legal forms are drafted by licensed attorneys, ensuring compliance with applicable laws.
Legal use & context
- The agreement is legally binding once signed by both parties.
- Using this form provides a framework that can help in legal dispute resolution.
- Understanding the legal context ensures compliance with cybersecurity laws.
Main things to remember
- This agreement is crucial for conducting unannounced penetration tests to identify network vulnerabilities.
- It clearly outlines the roles and responsibilities of both the consultant and the company.
- Proper completion and execution ensure legal protection and clarity in cybersecurity assessments.
Looking for another form?
Form popularity
FAQ
Ethical hacking involves an authorized attempt to gain unauthorized access to a computer system, application, or data. Carrying out an ethical hack involves duplicating strategies and actions of malicious attackers.Also known as white hats, ethical hackers are security experts that perform these assessments.
Ethical hacking (also known as pen testing or penetration testing) is a term that covers the intruding practices aiming to discover any threats and significant cyber security vulnerabilities that can be found and exploited by an ill-intended attacker.
The purpose of ethical hacking is to evaluate the security of and identify vulnerabilities in systems, networks or system infrastructure. It includes finding and attempting to exploit any vulnerabilities to determine whether unauthorized access or other malicious activities are possible.
They are also known as ethical hackers or penetration testers. Ethical hacking is completely legal and is one of the highest paid, fastest growing professions in information technology today. Often, an ethical hacker would work as an employee in an organization, a security firm or as an independent security consultant.
Ethical Hacking is an authorized practice of bypassing system security to identify potential data breaches and threats in a network. The company that owns the system or network allows Cyber Security engineers to perform such activities in order to test the system's defenses.
What is penetration testing? Penetration testing is a specific type of ethical hacking, in which an organisation hires a certified professional to assess the strength of its cyber security defences.
A penetration test, colloquially known as a pen test, pentest or ethical hacking, is an authorized simulated cyberattack on a computer system, performed to evaluate the security of the system; this is not to be confused with a vulnerability assessment.
It aims to encompass various attacks through different hacking techniques to find security flaws. Penetration testing focuses on the security of the specific area defined for testing. Ethical hacking is a comprehensive term and penetration testing is one of the functions of the ethical hacker.
The practice of breaking into, or bypassing an online system or network in order to expose its flaws for further improvement is entirely ethical (and you can make a nice living doing it too.) Examples of ethical hacking include exploiting or exposing a website in order to discover its weak points.