Utah Ethical Hacking Agreement for External Network Security - Unannounced Penetration Test
Description
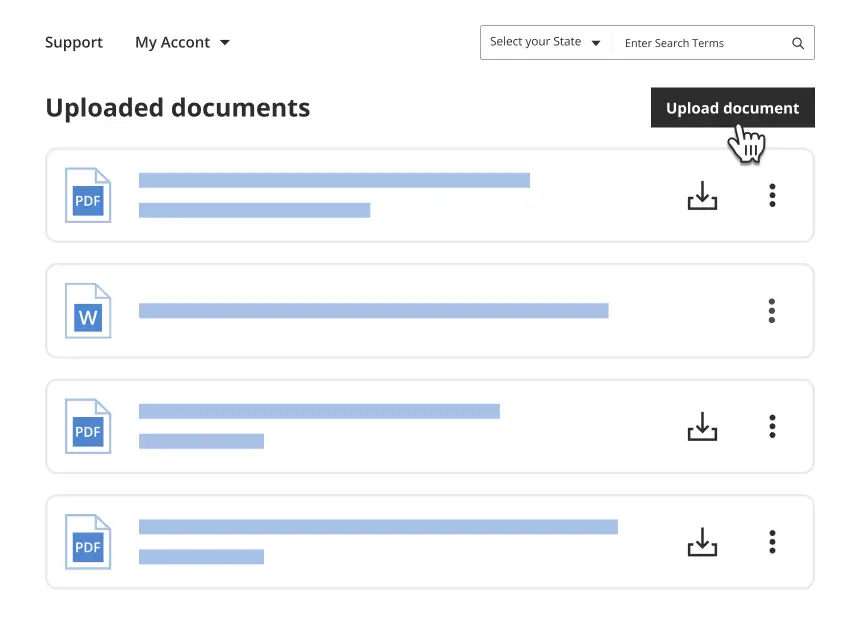
Get your form ready online
Our built-in tools help you complete, sign, share, and store your documents in one place.
Make edits, fill in missing information, and update formatting in US Legal Forms—just like you would in MS Word.
Download a copy, print it, send it by email, or mail it via USPS—whatever works best for your next step.
Sign and collect signatures with our SignNow integration. Send to multiple recipients, set reminders, and more. Go Premium to unlock E-Sign.
If this form requires notarization, complete it online through a secure video call—no need to meet a notary in person or wait for an appointment.
We protect your documents and personal data by following strict security and privacy standards.
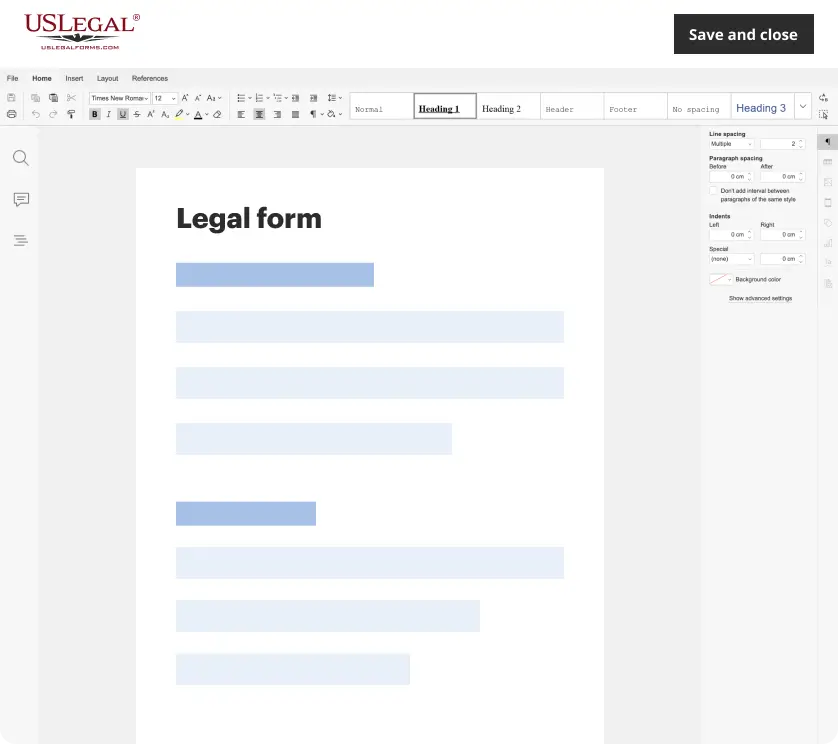
Make edits, fill in missing information, and update formatting in US Legal Forms—just like you would in MS Word.
Download a copy, print it, send it by email, or mail it via USPS—whatever works best for your next step.
Sign and collect signatures with our SignNow integration. Send to multiple recipients, set reminders, and more. Go Premium to unlock E-Sign.
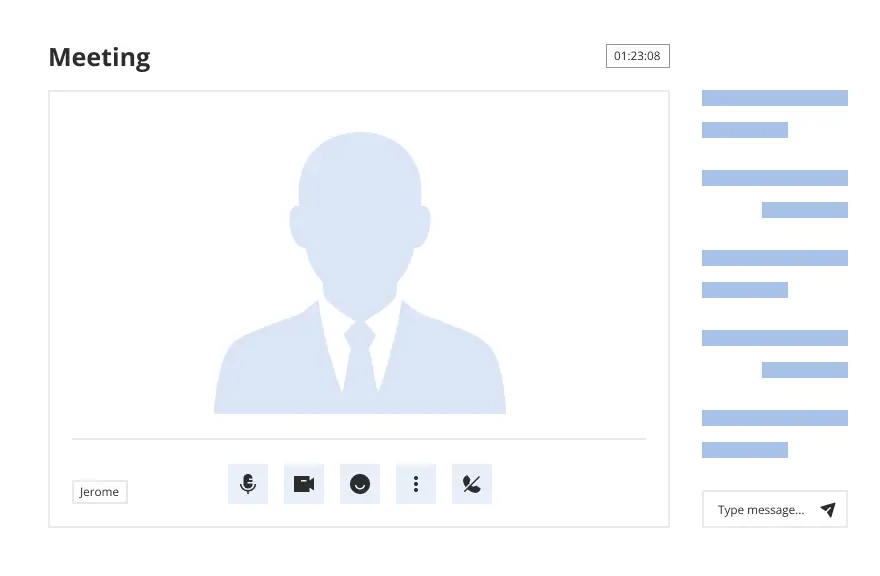
If this form requires notarization, complete it online through a secure video call—no need to meet a notary in person or wait for an appointment.
We protect your documents and personal data by following strict security and privacy standards.
Looking for another form?
How to fill out Ethical Hacking Agreement For External Network Security - Unannounced Penetration Test?
If you wish to acquire, obtain, or print formal document templates, utilize US Legal Forms, the largest selection of legal forms available online.
Take advantage of the website's user-friendly and convenient search to find the documents you need.
Various templates for business and personal purposes are categorized by types and suggestions, or keywords.
Step 5. Complete the payment. You can use your Visa or MasterCard or PayPal account to finalize the purchase.
Step 6. Select the format of the legal form and download it to your device. Step 7. Complete, modify, and print or sign the Utah Ethical Hacking Agreement for External Network Security - Unannounced Penetration Test.
- Utilize US Legal Forms to procure the Utah Ethical Hacking Agreement for External Network Security - Unannounced Penetration Test with just a few clicks.
- If you are already a US Legal Forms customer, Log In to your account and click the Download button to retrieve the Utah Ethical Hacking Agreement for External Network Security - Unannounced Penetration Test.
- You can also access forms you previously obtained in the My documents tab of your account.
- If you are utilizing US Legal Forms for the first time, follow the steps below.
- Step 1. Ensure you have selected the form for the correct state/region.
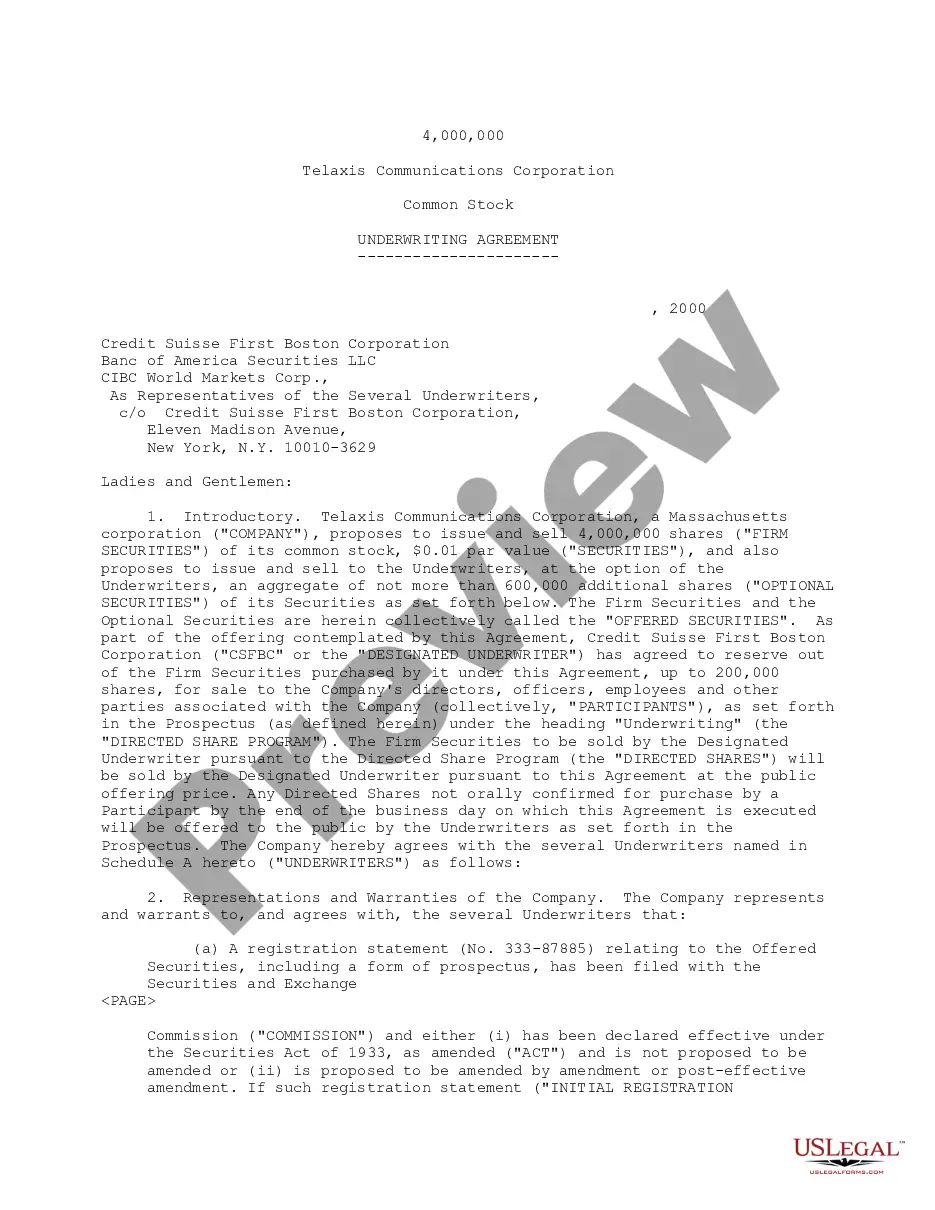
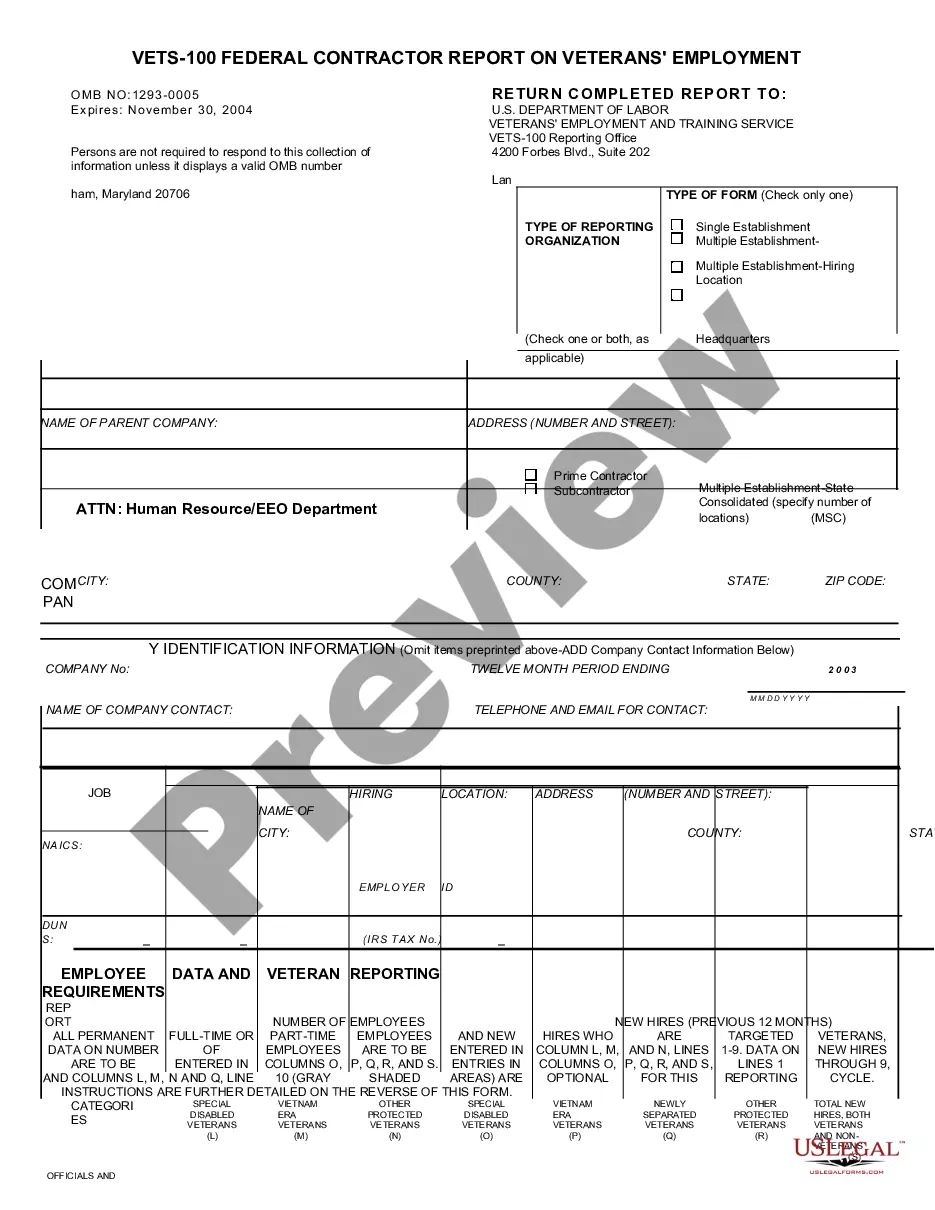
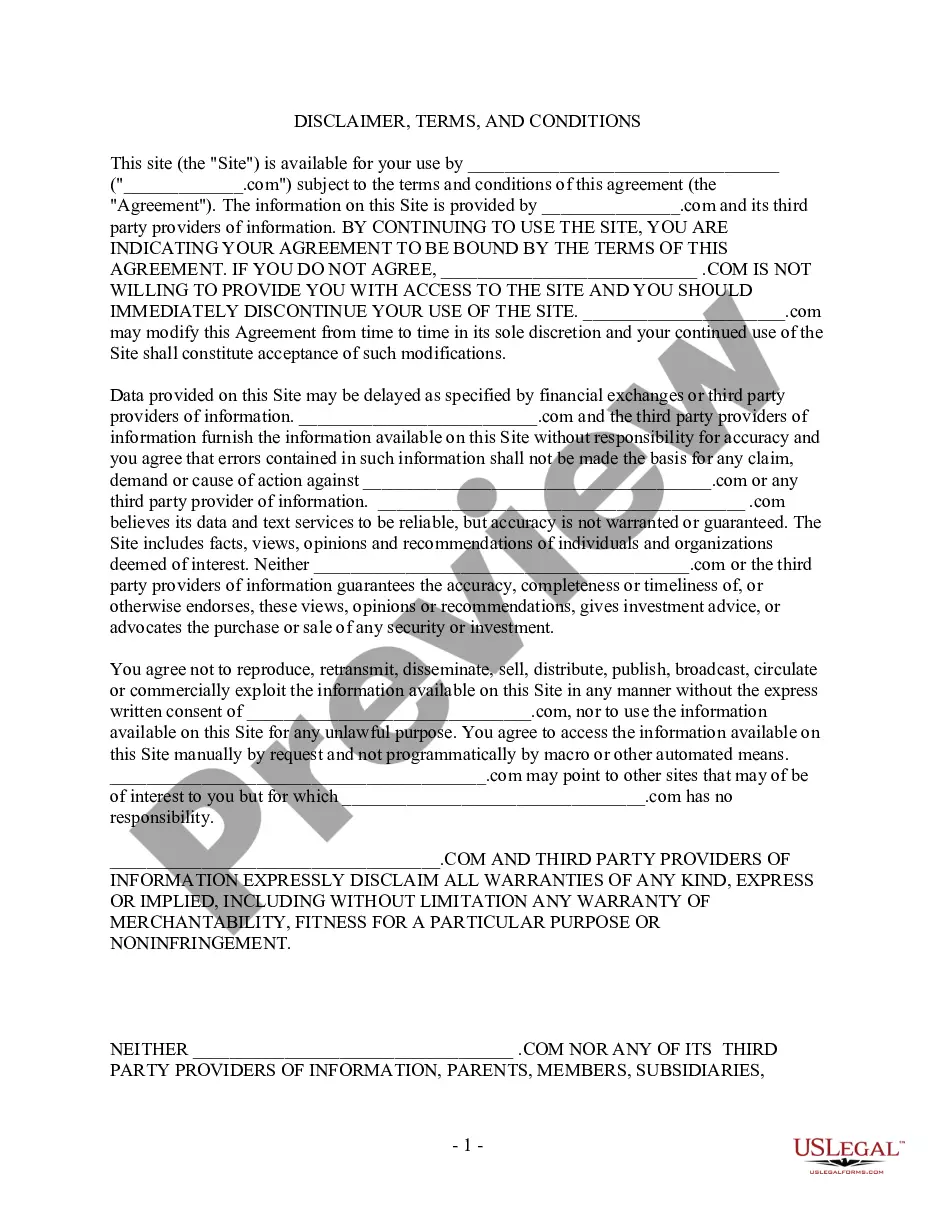
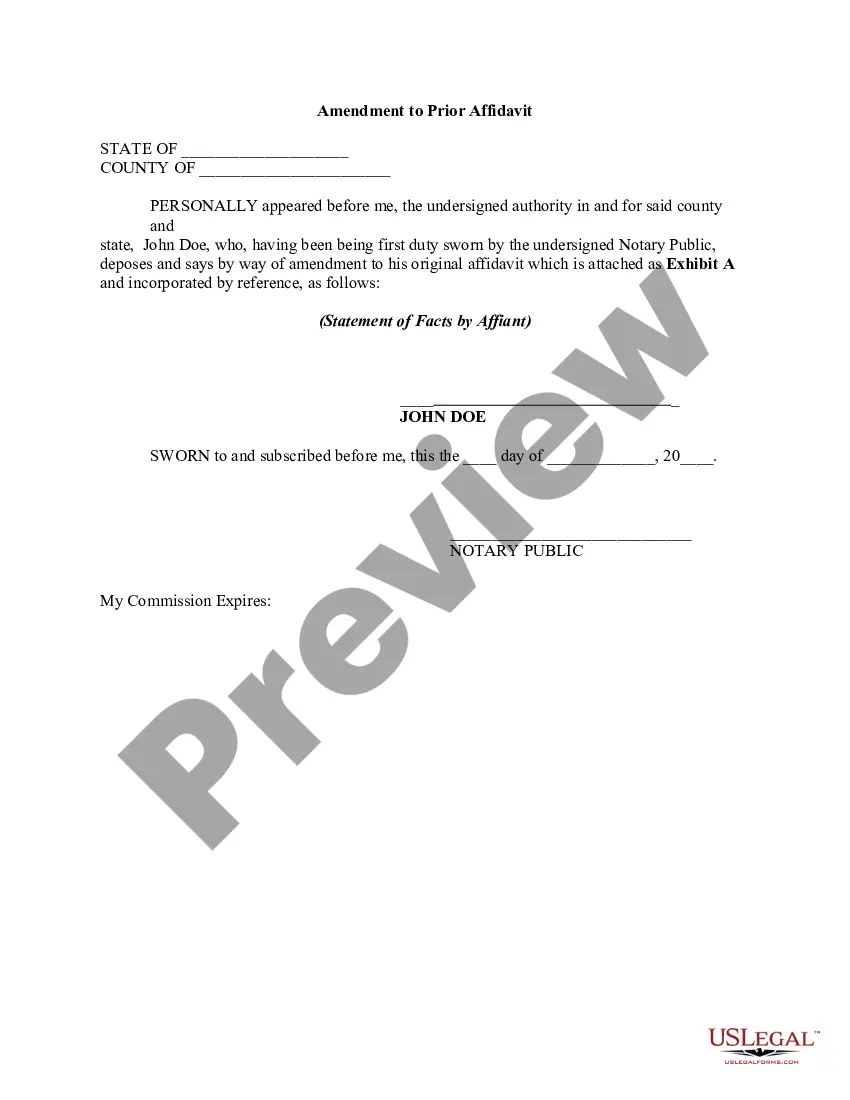
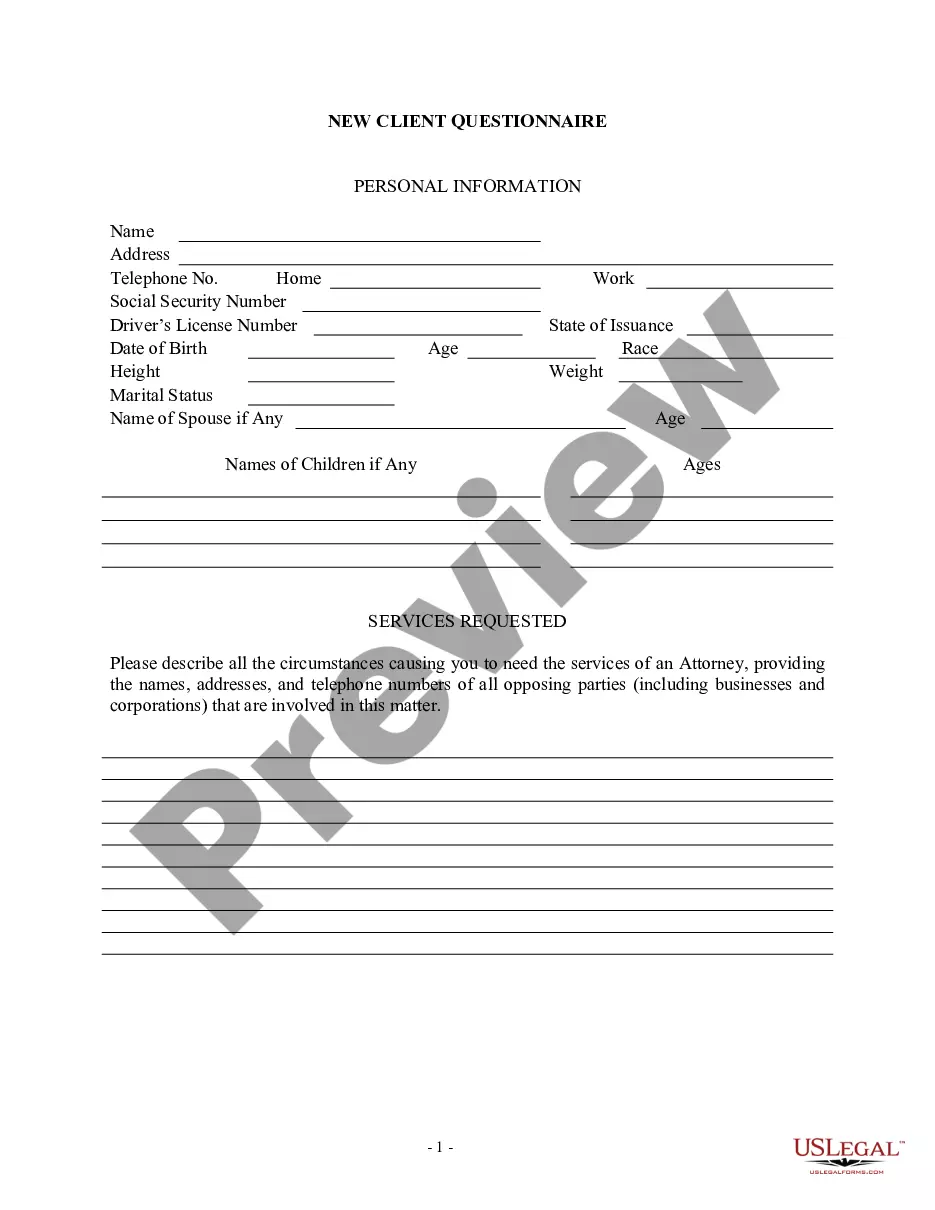
- Step 2. Utilize the Preview option to review the form's content. Make sure to read the summary.
- Step 3. If you are dissatisfied with the form, use the Search field at the top of the screen to find other versions of the legal form template.
- Step 4. After locating the form you desire, click the Buy now button. Choose the payment plan you prefer and enter your details to register for an account.
Form popularity
FAQ
The 7 steps of testing in the context of a Utah Ethical Hacking Agreement for External Network Security - Unannounced Penetration Test include planning, information gathering, threat modeling, vulnerability analysis, exploitation, post-exploitation, and reporting. During planning, identify the scope and objectives of your test. Information gathering follows, where you collect data about the target system, allowing for thorough assessment. Next, you model potential threats, analyze vulnerabilities, exploit weaknesses, and finally, compile a detailed report outlining findings and recommendations, ensuring a comprehensive approach to improving security.
Testing in the context of ethical hacking refers to the process of assessing a system's security through various methods and techniques. It involves simulating potential cyber-attack scenarios to uncover vulnerabilities that could be exploited. A Utah Ethical Hacking Agreement for External Network Security - Unannounced Penetration Test provides the framework for this assessment, ensuring it is both legal and effective. Successful testing helps organizations not only identify and fix these vulnerabilities but also enhance their overall security strategy.
Yes, ethical hackers perform testing to identify vulnerabilities in systems, networks, and applications. By conducting a thorough assessment with a Utah Ethical Hacking Agreement for External Network Security - Unannounced Penetration Test, they help organizations strengthen their security posture. Their testing simulates what a malicious attacker might do, allowing businesses to address weaknesses before they can be exploited. This proactive approach not only safeguards sensitive data but also builds trust with customers.
To engage in an ethical hack legally, an ethical hacker must obtain a signed Utah Ethical Hacking Agreement for External Network Security - Unannounced Penetration Test from the organization being tested. This agreement outlines the scope of the test, the systems involved, and the security protocols to be followed. It ensures that both parties understand the objectives and limits of the testing process. Without this formal consent, any testing conducted may be considered unauthorized, leading to potential legal issues.
Becoming an ethical hacker typically requires a mix of education, technical skills, and certifications. While formal education in cybersecurity is beneficial, hands-on experience in networking, programming, and system administration is equally important. Additionally, certifications like Certified Ethical Hacker (CEH) can bolster credibility. A strong understanding of the Utah Ethical Hacking Agreement for External Network Security - Unannounced Penetration Test also enhances one’s ability to navigate legal and ethical boundaries.
An ethical hacker can commence testing once all necessary legal agreements are in place, such as the Utah Ethical Hacking Agreement for External Network Security - Unannounced Penetration Test. This includes obtaining permission from the organization whose systems are being tested and ensuring that all parties understand the parameters of the test. It's essential to establish timelines and communicate effectively to avoid disruptions or misunderstandings during the process.
Ethical hacking is a proactive approach to security, where professionals simulate attacks to identify vulnerabilities, whereas testing often refers to the specific procedures used during that assessment. In the context of a Utah Ethical Hacking Agreement for External Network Security - Unannounced Penetration Test, ethical hacking encompasses the entire process, including planning, executing, and reporting findings. Understanding these differences helps clarify expectations and objectives for both clients and hackers.
When engaging in a Utah Ethical Hacking Agreement for External Network Security - Unannounced Penetration Test, it is crucial to understand both ethical and legal aspects. Ethical hackers must respect privacy, defend personal data, and ensure they have explicit permission to conduct tests. Legal frameworks, such as laws governing unauthorized access, must also be considered to avoid potential penalties. A well-drafted agreement helps address these concerns, guiding ethical hackers in their responsibilities.
An effective test contract should include the Utah Ethical Hacking Agreement for External Network Security - Unannounced Penetration Test, project timelines, and non-disclosure agreements. These documents ensure both parties are aligned on objectives and the protection of sensitive information. Proper documentation helps in maintaining transparency and sets the foundation for a successful engagement.
structured pentest contract should include definitions, the scope of work, confidentiality clauses, and terms regarding liability and indemnification. Definitions clarify technical terms, while the scope outlines the testing parameters. Including confidentiality and liability terms protects sensitive information and delineates responsibility in case of issues.