Theft Investigation Checklist
What is this form?
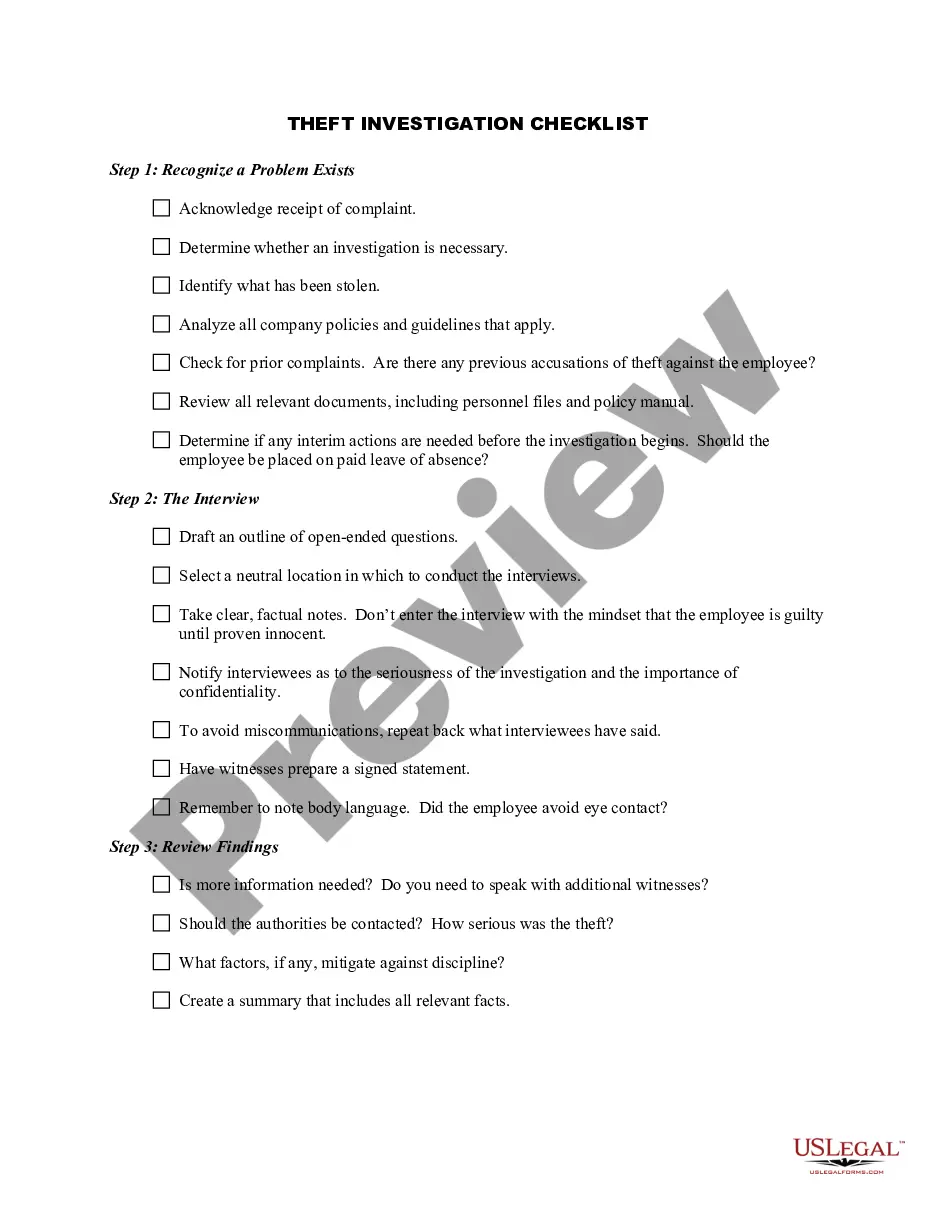
The Theft Investigation Checklist is a comprehensive tool designed to guide companies through the process of investigating theft incidents. This form ensures that all necessary steps are taken, from recognizing a problem to determining actions to be taken based on findings. The checklist is a vital resource for businesses aiming to handle theft investigations systematically and legally, ensuring that they do not overlook any critical steps or procedures.
Form components explained
- Step 1: Recognizing the problem and determining if an investigation is necessary.
- Step 2: Conducting interviews and drafting open-ended questions.
- Step 3: Reviewing findings to decide if further action is required.
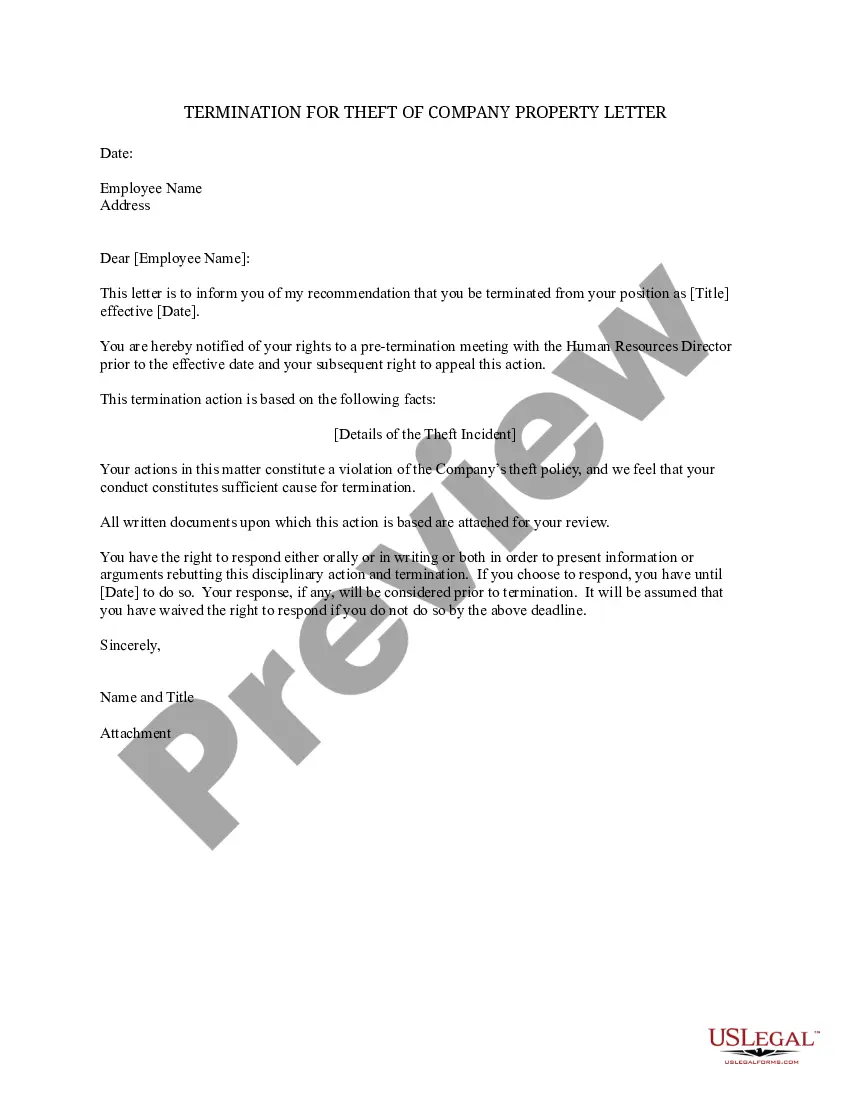
- Step 4: Recommending an appropriate course of action and notifying the decision-maker.
When to use this document
This checklist should be used whenever a business suspects theft has occurred within its operations. It is critical for ensuring that the investigation is thorough, legally compliant, and respects employee rights. This form is especially useful in cases where there are potential disputes over accusations of theft and when prior investigation guidelines need to be addressed.
Who can use this document
- Business owners and management personnel responsible for handling theft incidents.
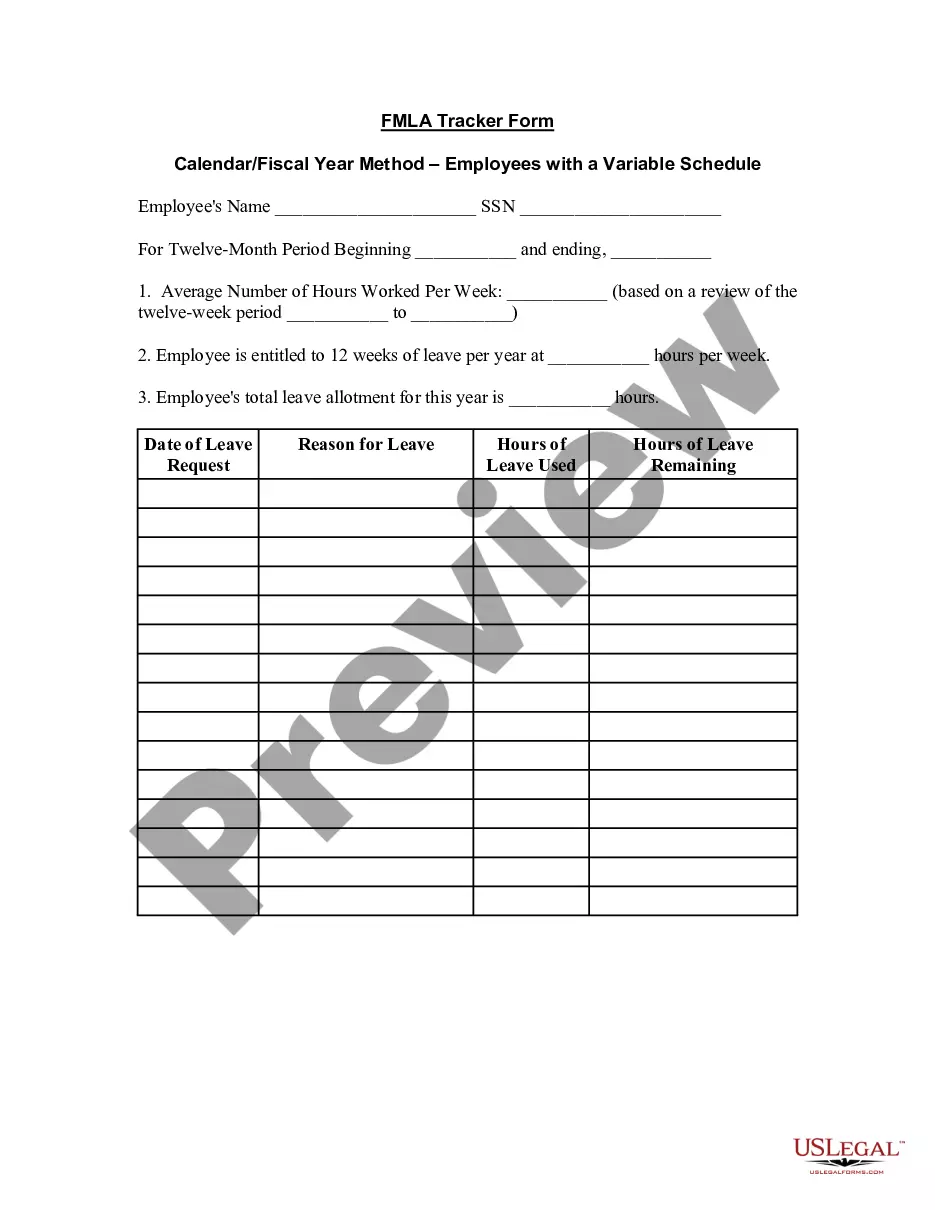
- Human resources professionals involved in employee investigations.
- Security personnel tasked with managing loss prevention.
Steps to complete this form
- Identify if there is a reason to believe theft has occurred.
- Schedule interviews with involved parties in a neutral setting.
- Document all findings and take clear notes during interviews.
- Review investigation findings comprehensively before making recommendations.
- Notify the appropriate management personnel about the findings and suggested actions.
Does this form need to be notarized?
Notarization is not commonly needed for this form. However, certain documents or local rules may make it necessary. Our notarization service, powered by Notarize, allows you to finalize it securely online anytime, day or night.
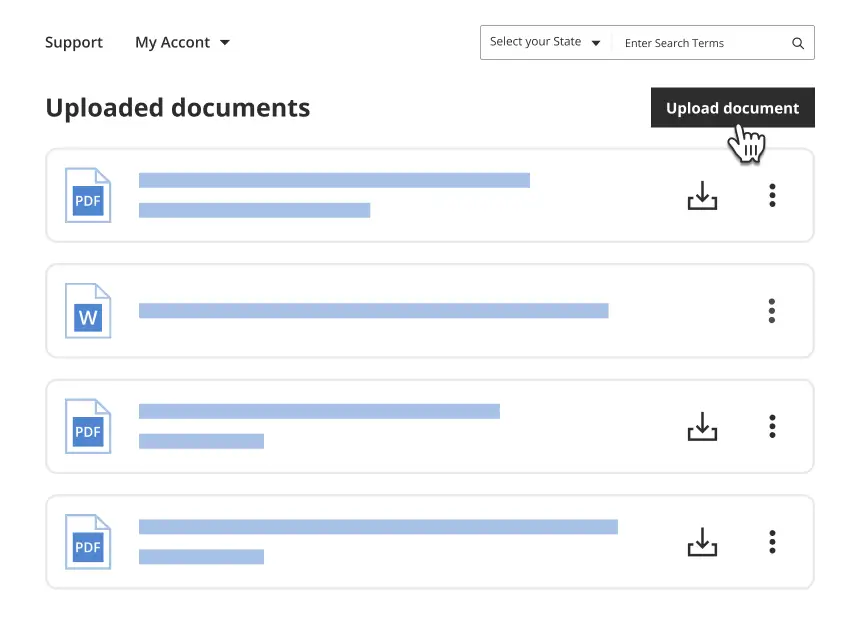
Get your form ready online
Our built-in tools help you complete, sign, share, and store your documents in one place.
Make edits, fill in missing information, and update formatting in US Legal Forms—just like you would in MS Word.
Download a copy, print it, send it by email, or mail it via USPS—whatever works best for your next step.
Sign and collect signatures with our SignNow integration. Send to multiple recipients, set reminders, and more. Go Premium to unlock E-Sign.
If this form requires notarization, complete it online through a secure video call—no need to meet a notary in person or wait for an appointment.
We protect your documents and personal data by following strict security and privacy standards.
Make edits, fill in missing information, and update formatting in US Legal Forms—just like you would in MS Word.
Download a copy, print it, send it by email, or mail it via USPS—whatever works best for your next step.
Sign and collect signatures with our SignNow integration. Send to multiple recipients, set reminders, and more. Go Premium to unlock E-Sign.
If this form requires notarization, complete it online through a secure video call—no need to meet a notary in person or wait for an appointment.
We protect your documents and personal data by following strict security and privacy standards.
Typical mistakes to avoid
- Failing to document conversations and findings accurately.
- Not conducting interviews in a neutral environment.
- Overlooking the importance of confidentiality during the investigation.
Why complete this form online
- Convenience of accessing the form anytime to ensure timely investigations.
- Editability to customize the checklist to specific business needs.
- Reliable format ensuring all necessary components are included for a thorough investigation.
Legal use & context
- This checklist is not a legal document in itself but serves as a guideline for conducting theft investigations.
- Ensure compliance with labor laws and regulations pertaining to employee rights during investigations.
- Consulting with legal professionals may enhance the validity of the investigation results.
Main things to remember
- Theft investigations require systematic and documented approaches.
- Utilizing a checklist ensures important steps are not overlooked.
- This form is crucial in maintaining fairness and legality during investigations.
Looking for another form?
Form popularity
FAQ
What happened? What was the date, time and duration of the incident or behavior? How many times did this happen? Where did it happen? How did it happen? Did anyone else see it happen? Was there physical contact?
Decide whether to investigate. Take immediate action, if necessary. Choose an investigator. Plan the investigation. Conduct interviews. Gather documents and other evidence. Evaluate the evidence. Take action.
There are three types of field investigationsdescriptive, comparative, and correlative. Descriptive field investigations involve describing parts of a natural system.
Information to Identify the Case: Begin the report with case specific information that identifies the case the report is related to. Referral Source: Allegation Details: Information About the Subject: Investigation Scope/ Purpose: Case Notes: Interview Summaries: Interview Reports:
Identify Scene Dimensions. Locate the focal point of the scene. Establish Security. Tape around the perimeter. Create a Plan & Communicate. Determine the type of crime that occurred. Conduct Primary Survey. Identify potential evidence. Document and Process Scene. Conduct Secondary Survey. Record and Preserve Evidence.
Preserve and Document the Incident Scene. Collecting Information. Determine Root Causes. Implement Corrective Actions.
Follow Company Policies. Assign an Investigator. Emphasize Confidentiality. Begin the Investigation ASAP. Gather Evidence, Conduct Interviews, and Trace Assets. Notify the Police. Discipline or Terminate the Employee. Recover Losses.
Step 1: Ensure Confidentiality. Step 2: Provide Interim Protection. Step 3: Select the investigator. Step 4: Create a Plan for the Investigation. Step 5: Develop Interview Questions. Step 6: Conduct Interviews.
The investigative process is a progression of activities or steps moving from evidence gathering tasks, to information analysis, to theory development and validation, to forming reasonable ground to believe, and finally to the arrest and charge of a suspect.