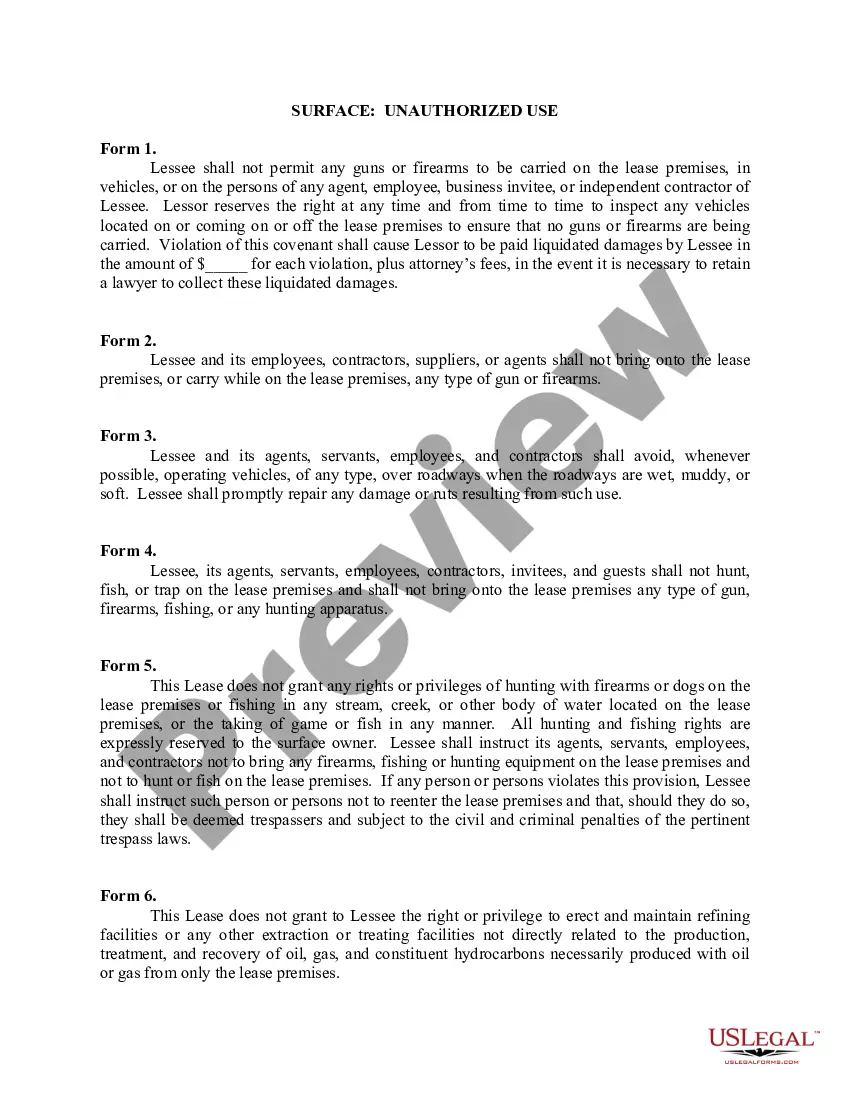
Surface - Unauthorized Use
What this document covers
The Surface - Unauthorized Use form is a lease rider that adds specific provisions to an Oil and Gas Lease. It is designed to address specific concerns regarding the use of the leased property by the Lessee, particularly concerning unauthorized activities such as the carrying of firearms and hunting rights. This document is important for surface owners who want to limit the Lessee's rights beyond the standard lease agreements.
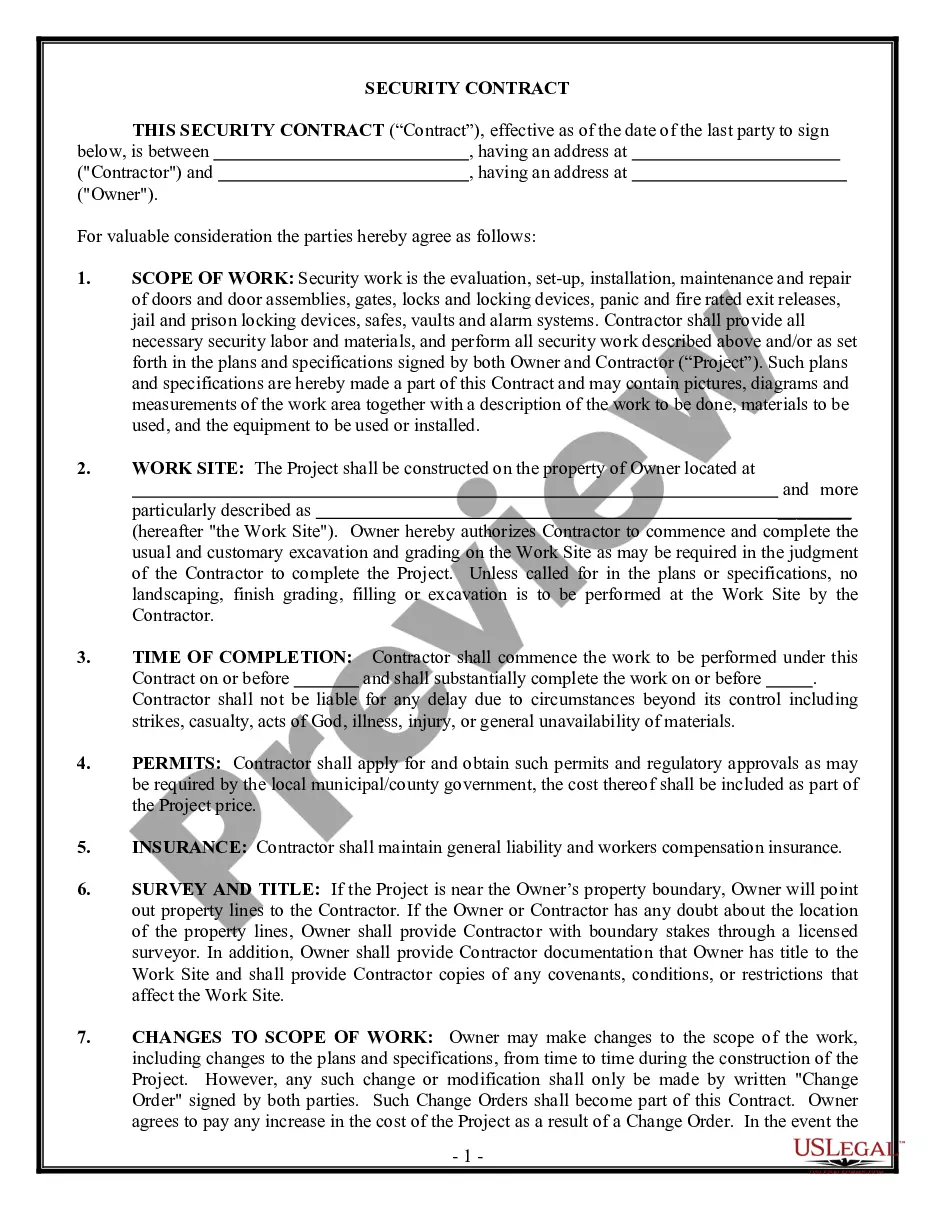
Form components explained
- Prohibition against carrying firearms on the lease premises.
- Inspection rights for the Lessor to ensure compliance with firearm restrictions.
- Requirements for Lessee to repair damages caused by vehicle use on soft ground.
- Complete restriction on hunting, fishing, or trapping on the lease premises.
- Explicit reservation of hunting and fishing rights for the surface owner.
- Limitations on the construction of facilities unrelated to oil and gas operations.
When to use this document
This form should be used when you are entering into or modifying a lease agreement for oil and gas extraction and want to enforce additional restrictions on how the Lessee can use the surface property. It is particularly relevant if you have concerns about safety, property damage, or unauthorized use of firearms and recreational activities on the leased land.
Who needs this form
- Landowners looking to lease their land for oil and gas exploration.
- Surface owners who want to maintain control over land use during a lease.
- Those who wish to protect their property rights and ensure compliance with safety standards.
- Individuals or legal entities involved in drafting or negotiating oil and gas leases.
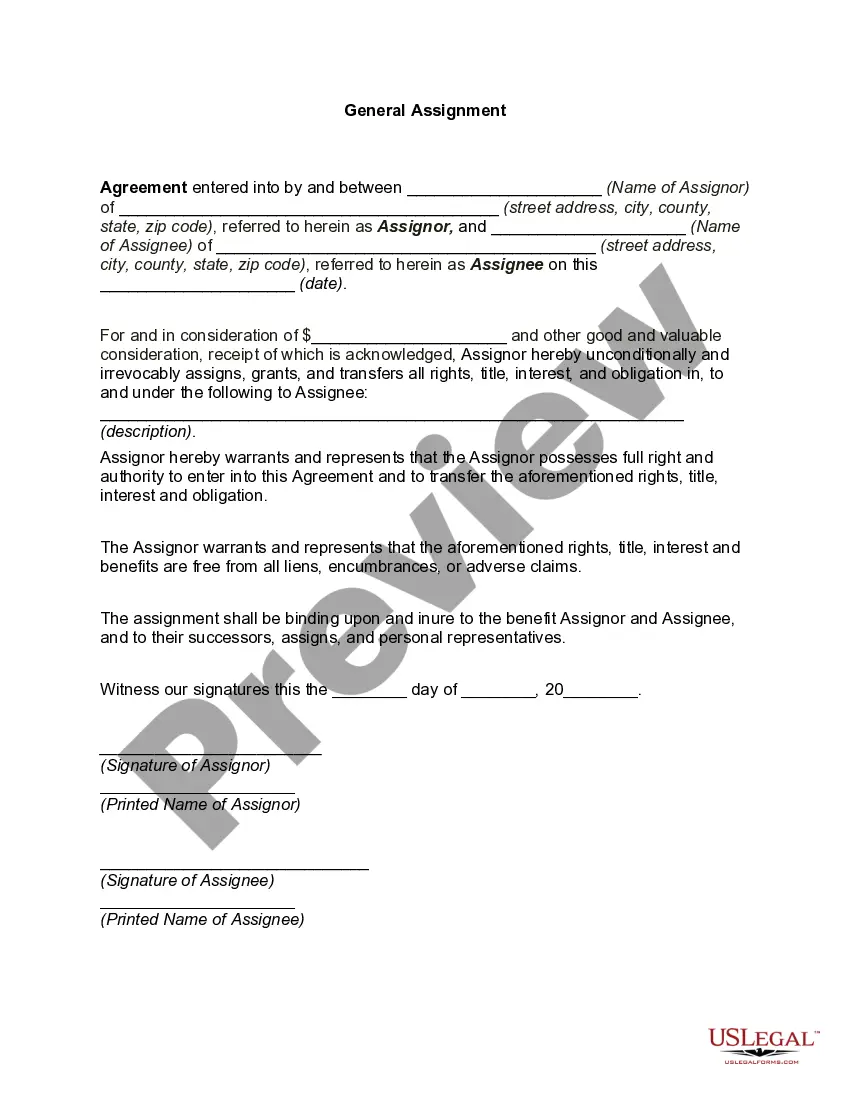
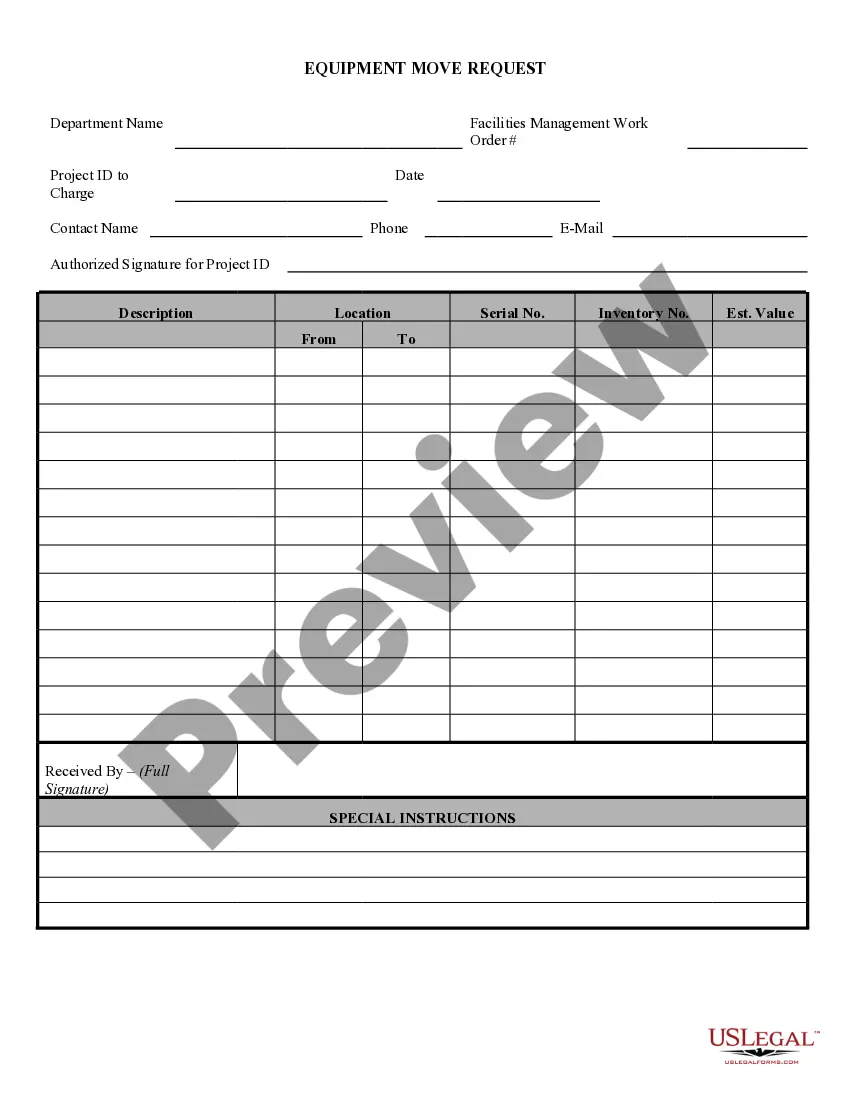
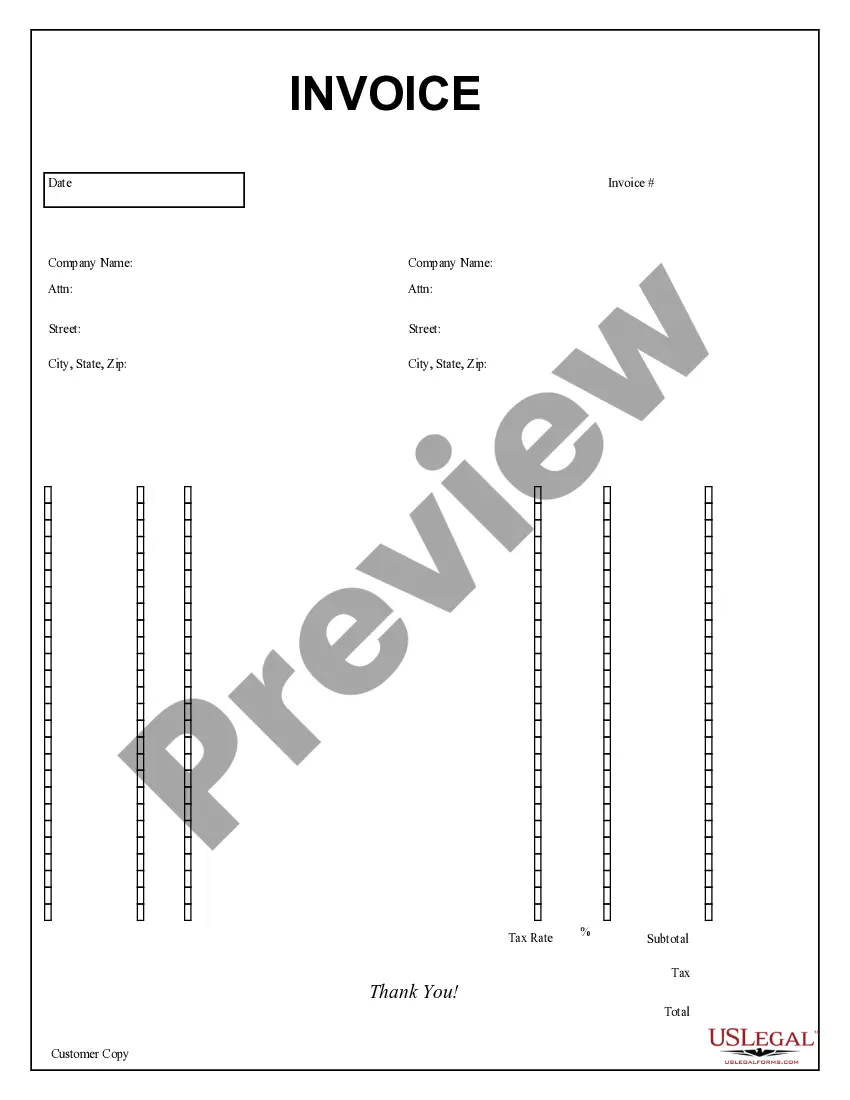
How to complete this form
- Identify the parties involved in the lease agreement (Lessor and Lessee).
- Specify the geographical boundaries of the lease premises.
- Incorporate specific clauses regarding firearm restrictions and hunting rights.
- Detail the obligations of the Lessee to repair any damage caused on the property.
- Provide space for signatures and dates to formalize the agreement.
Is notarization required?
This form usually doesn’t need to be notarized. However, local laws or specific transactions may require it. Our online notarization service, powered by Notarize, lets you complete it remotely through a secure video session, available 24/7.
Get your form ready online
Our built-in tools help you complete, sign, share, and store your documents in one place.
Make edits, fill in missing information, and update formatting in US Legal Forms—just like you would in MS Word.
Download a copy, print it, send it by email, or mail it via USPS—whatever works best for your next step.
Sign and collect signatures with our SignNow integration. Send to multiple recipients, set reminders, and more. Go Premium to unlock E-Sign.
If this form requires notarization, complete it online through a secure video call—no need to meet a notary in person or wait for an appointment.
We protect your documents and personal data by following strict security and privacy standards.
Make edits, fill in missing information, and update formatting in US Legal Forms—just like you would in MS Word.
Download a copy, print it, send it by email, or mail it via USPS—whatever works best for your next step.
Sign and collect signatures with our SignNow integration. Send to multiple recipients, set reminders, and more. Go Premium to unlock E-Sign.
If this form requires notarization, complete it online through a secure video call—no need to meet a notary in person or wait for an appointment.
We protect your documents and personal data by following strict security and privacy standards.
Avoid these common issues
- Failing to specify exact boundaries of the lease premises.
- Neglecting to clearly state restrictions on firearms and hunting activities.
- Omitting obligations for maintenance and repair duties of the Lessee.
- Using vague language that can lead to misinterpretation of rights and responsibilities.
- Not ensuring all parties sign the document to validate it.
Benefits of using this form online
- Convenient access to legal forms that can be downloaded anytime.
- Editability allows customization to fit specific lease terms.
- Reliability with forms drafted by licensed attorneys, ensuring legal soundness.
Legal use & context
- The form serves as a legally binding document to enforce specific uses of the property.
- Violations can lead to liquidated damages and potential legal action for remedies.
- Rights reserved for surface owners provide significant protection against misuse by Lessees.
Key takeaways
- The Surface - Unauthorized Use form is crucial for protecting surface owner rights.
- It helps regulate activities on leased land, ensuring safety and compliance.
- Clear language and specific provisions are essential to prevent misunderstandings.
Looking for another form?
Form popularity
FAQ
An attack surface is the total sum of vulnerabilities that can be exploited to carry out a security attack. Attack surfaces can be physical or digital. The term attack surface is often confused with the term attack vector, but they are not the same thing.
If you believe that you have unauthorized charges, change your Microsoft account password and contact your bank or card issuer to report potential unauthorized use of your bank, credit or debit card.
The attack surface of a software environment is the sum of the different points (for "attack vectors") where an unauthorized user (the "attacker") can try to enter data to or extract data from an environment. Keeping the attack surface as small as possible is a basic security measure.
What's an attack surface? the combined sum of all attack vectors in a system or network; The attack surface describes all possible ways that an attacker could interact and exploit potential vulnerabilities in the network and connected systems.
An attack surface is the entire area of an organization or system that is susceptible to hacking. It's made up of all the points of access that an unauthorized person could use to enter the system. Once inside your network, that user could cause damage by manipulating or downloading data.
The charges may be for a Microsoft subscription with recurring billing, such as Xbox, Office or OneDrive that you or a family member owns, or for a recent free trial subscription that rolled into a paid subscription.
Brute-force attack. Under this attack, cybercriminals use the trial and error approach to guess the password successfully. Credential Stuffing. Phishing and Spear Phishing. Malware attacks.
Abbreviation(s) and Synonym(s): Definition(s): The set of points on the boundary of a system, a system element, or an environment where an attacker can try to enter, cause an effect on, or extract data from, that system, system element, or environment.
US$99 is the price of the Office 365 Home subscription. To install your 365 on another device just sign in to your Microsoft account, Installs page on the computer you want to install on, and choose Install Office. .This page provides an overview of licenses and / or subscriptions you have associated with your email.