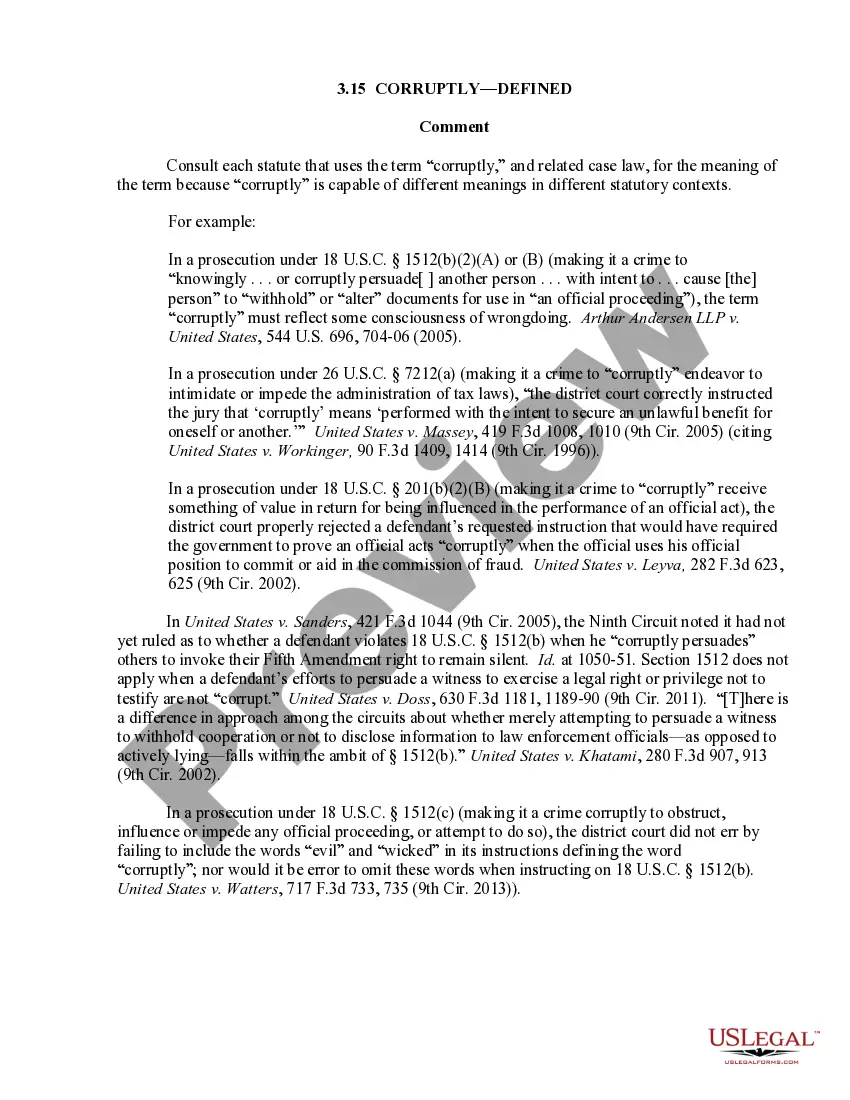
3.15 Corruptly-Defined.
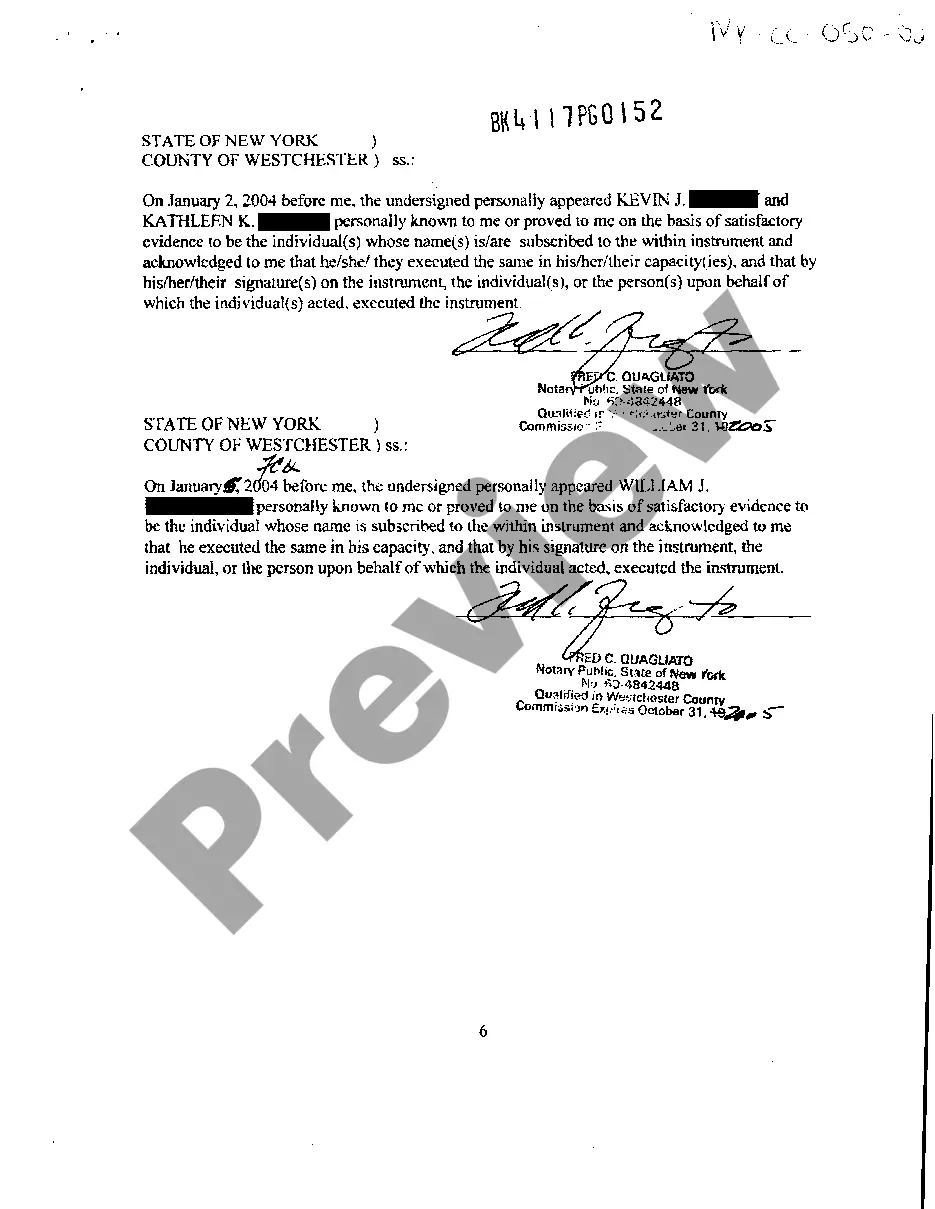
Does this form need to be notarized?
This form usually doesn’t need to be notarized. However, local laws or specific transactions may require it. Our online notarization service, powered by Notarize, lets you complete it remotely through a secure video session, available 24/7.
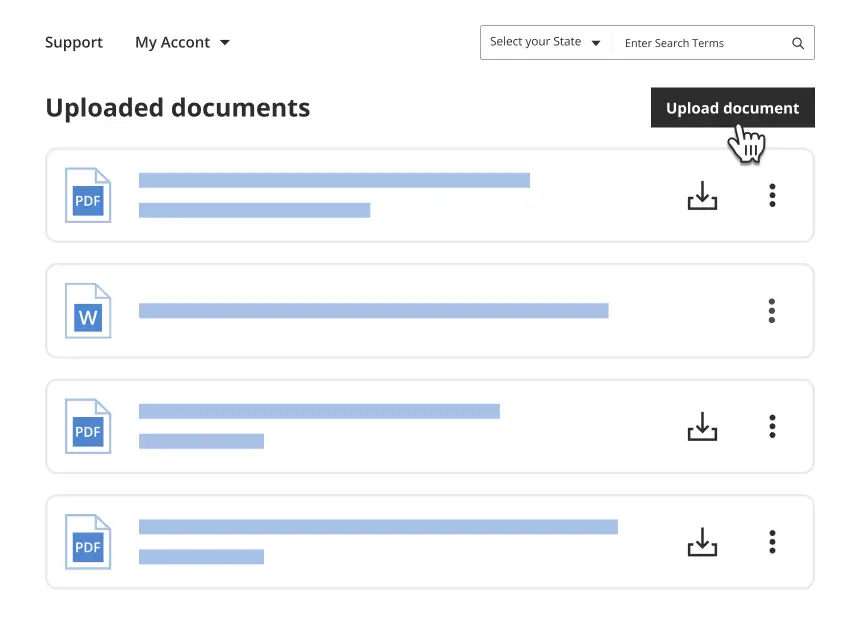
Get your form ready online
Our built-in tools help you complete, sign, share, and store your documents in one place.
Make edits, fill in missing information, and update formatting in US Legal Forms—just like you would in MS Word.
Download a copy, print it, send it by email, or mail it via USPS—whatever works best for your next step.
Sign and collect signatures with our SignNow integration. Send to multiple recipients, set reminders, and more. Go Premium to unlock E-Sign.
If this form requires notarization, complete it online through a secure video call—no need to meet a notary in person or wait for an appointment.
We protect your documents and personal data by following strict security and privacy standards.
Make edits, fill in missing information, and update formatting in US Legal Forms—just like you would in MS Word.
Download a copy, print it, send it by email, or mail it via USPS—whatever works best for your next step.
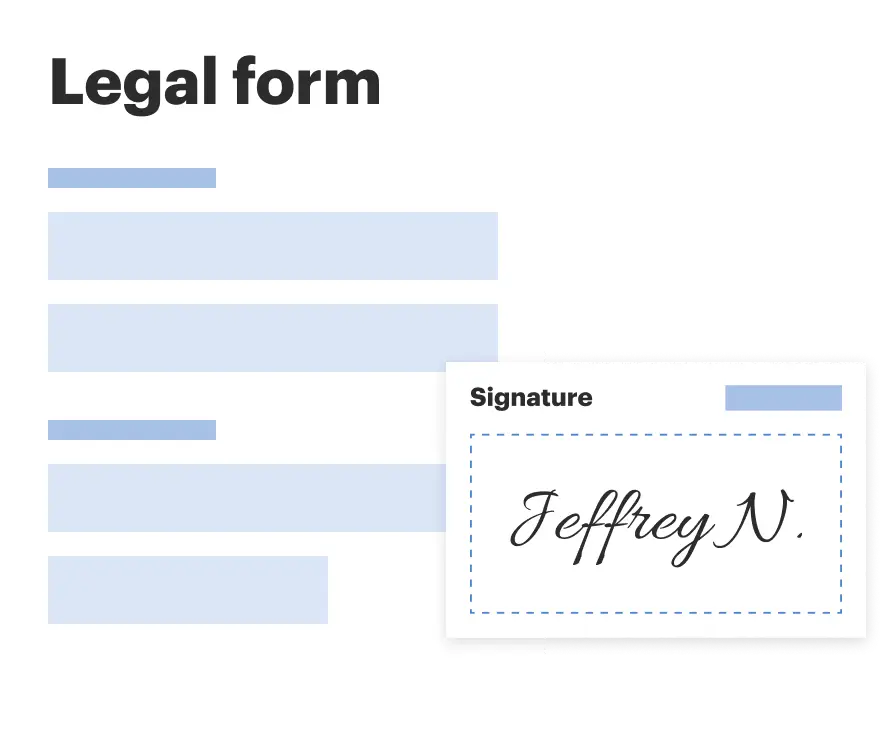
Sign and collect signatures with our SignNow integration. Send to multiple recipients, set reminders, and more. Go Premium to unlock E-Sign.
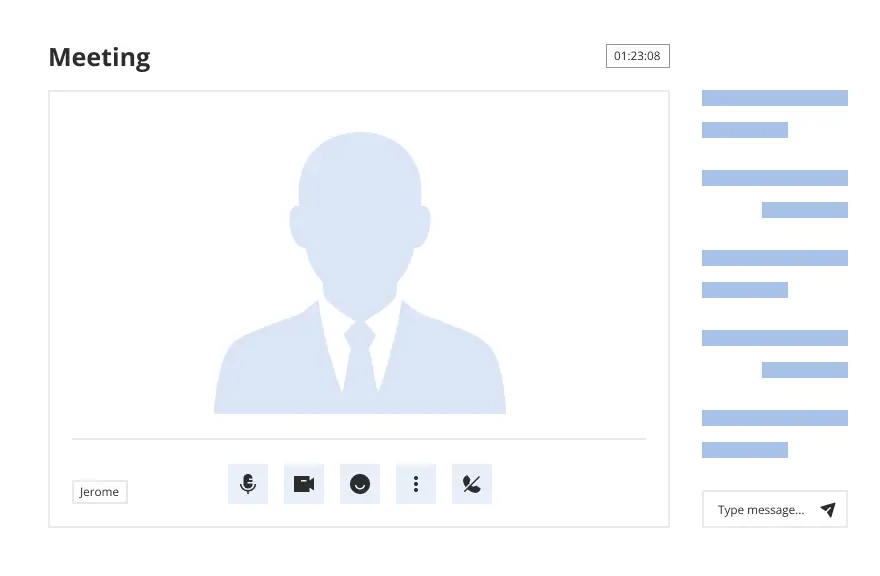
If this form requires notarization, complete it online through a secure video call—no need to meet a notary in person or wait for an appointment.
We protect your documents and personal data by following strict security and privacy standards.
Looking for another form?
Form popularity
FAQ
Generally, a defendant may be found guilty under section 1505 if the government establishes that: (1) there was a proceeding pending before a department or agency of the United States; (2) the defendant knew of or had a reasonably founded belief that the proceeding was pending; and (3) the defendant corruptly
/k??r?ptli/ ?in a way that is not honest or moral, in return for money or to get an advantage. corruptly elected officials.
§ 1503, provides: Whoever . . . corruptly or by threats or force, or by any threatening letter or communication, influences, obstructs, or impedes, or endeavors to influence, obstruct, or impede, the due administration of justice, shall be (guilty of an offense).
Section 1515. 1515. A refusal by a creditor to accept performance, made before an offer thereof, is equivalent to an offer and refusal, unless, before performance is actually due, he gives notice to the debtor of his willingness to accept it.
To show constructive possession, the government must prove a connection between the defendant and the firearm or ammunition sufficient "to support the inference that the defendant exercised dominion and control over" it. United States v. Carrasco, 257 F. 3d 1045, 1049 (9th Cir.
Misleading and ?deceptive? shall mean deceptive as that term is interpreted under the Federal Trade Commission Act.
As used in section 1505, the term ?corruptly? means acting with an improper purpose, personally or by influencing another, including making a false or misleading statement, or withholding, concealing, altering, or destroying a document or other information.