Oklahoma Identity Theft Recovery Package
About this form package
The Oklahoma Identity Theft Recovery Package is a comprehensive set of forms designed for victims of identity theft. This package provides essential documents to help individuals navigate the complex process of addressing fraudulent activity with creditors and government agencies. Unlike other legal form packages, this one specifically targets the unique challenges and procedures associated with identity theft recovery in Oklahoma, streamlining the process of clearing your name and protecting your financial future.
Forms provided in this package
- Identity Theft Protection Guide
- Federal Trade Commission Affidavit regarding Identity Theft
- Letter to Credit Reporting Company or Bureau regarding Identity Theft
- Letter to Creditors notifying them of Identity Theft
- Letter to Creditors Notifying Them of Identity Theft for New Accounts
- Letter Notifying Law Enforcement of Identity Theft
- Letter Notifying Postal Authorities of Identity Theft
- Letter Notifying Social Security Administration of Identity Theft
- Letter to Other Entities Notifying Them of Identity Theft
- Identity Theft Contact Table
- Identity Theft Checklist
- Sample Letter to Report False Submission of Information
- Sample Letter for Request for Free Credit Report Allowed by Federal Law
When to use this document
This package is particularly useful in the following scenarios:
- If your personal identification has been lost or stolen.
- If you discover unauthorized transactions on your credit reports.
- If you need to report identity theft to law enforcement or other entities.
- If you are facing issues such as false arrests or fraudulent employment due to identity theft.
- If you need to correct your credit report and prevent further misuse of your identity.
Who can use this document
- Victims of identity theft residing in Oklahoma.
- Individuals looking to restore their credit and personal reputation.
- Anyone needing to report identity theft to creditors and agencies.
- People seeking to prevent future financial or legal complications due to stolen identification.
Instructions for completing these forms
- Review the included forms to understand their purposes and requirements.
- Gather necessary personal information and documentation related to the identity theft.
- Fill out each form accurately, ensuring all fields are completed with the correct information.
- Review the forms for completeness and correctness before submission.
- Submit the forms to the relevant creditors, agencies, and law enforcement as required.
Notarization guidance for this package
No, forms in this package typically do not require notarization unless required by local law. Ensure you review the specific requirements for each form to confirm if notarization is necessary for your situation.
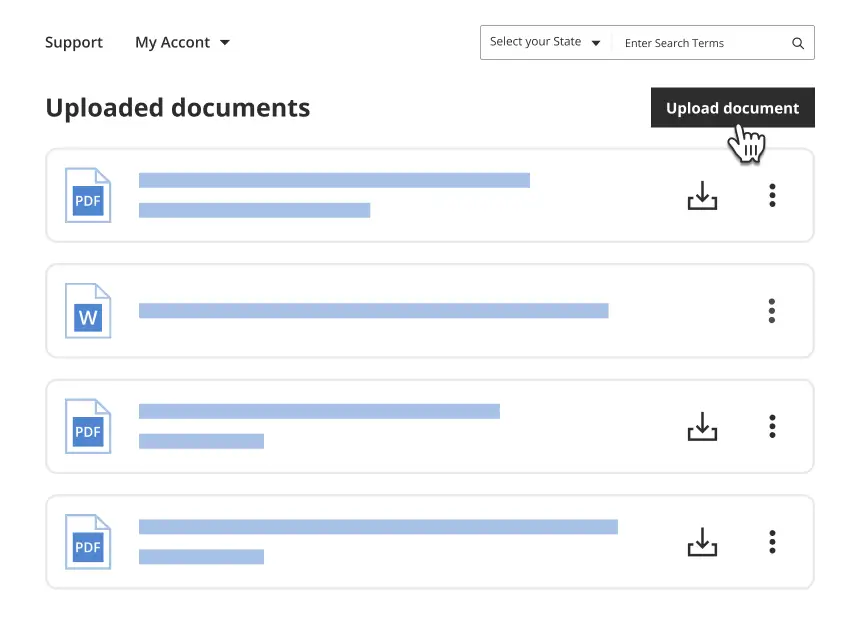
Get your form ready online
Our built-in tools help you complete, sign, share, and store your documents in one place.
Make edits, fill in missing information, and update formatting in US Legal Forms—just like you would in MS Word.
Download a copy, print it, send it by email, or mail it via USPS—whatever works best for your next step.
Sign and collect signatures with our SignNow integration. Send to multiple recipients, set reminders, and more. Go Premium to unlock E-Sign.
If this form requires notarization, complete it online through a secure video call—no need to meet a notary in person or wait for an appointment.
We protect your documents and personal data by following strict security and privacy standards.
Make edits, fill in missing information, and update formatting in US Legal Forms—just like you would in MS Word.
Download a copy, print it, send it by email, or mail it via USPS—whatever works best for your next step.
Sign and collect signatures with our SignNow integration. Send to multiple recipients, set reminders, and more. Go Premium to unlock E-Sign.
If this form requires notarization, complete it online through a secure video call—no need to meet a notary in person or wait for an appointment.
We protect your documents and personal data by following strict security and privacy standards.
Common mistakes to avoid
- Failing to attach supporting documents when submitting forms.
- Not keeping copies of all correspondence for personal records.
- Missing deadlines for notifying creditors or agencies.
- Overlooking details while filling out forms, which can result in delays.
Advantages of online completion
- Convenience of accessing and completing forms from your own home.
- Forms are editable, allowing you to tailor each document to your specific situation.
- Reliable support through professionally drafted documents created by licensed attorneys.
- Cost savings compared to purchasing forms individually.
Legal use & context
- The forms are designed to comply with Oklahoma laws regarding identity theft recovery.
- Using these forms aids in establishing a legal record of your identity theft experience.
- Successfully completing and submitting these forms can initiate protective measures against future incidents.
Quick recap
- The Oklahoma Identity Theft Recovery Package provides essential forms for victims.
- Understanding when and how to use these forms can facilitate faster recovery from identity theft.
- Taking proactive steps with these documents is crucial in protecting your financial assets and personal reputation.
Looking for another form?
Form popularity
FAQ
Step 1: Call the companies where you know fraud occurred. Call the fraud department. Step 2: Place a fraud alert and get your credit reports. Place a free, one-year fraud alert by contacting one of the three credit bureaus. Step 3: Report identity theft to the FTC.
A typical case can take about 180 days to resolve, and the IRS is working to reduce that time period. If you have an open identity theft case that is being worked by the IRS, you need to continue to file your tax returns during this period.
On average, it can take between 100 and 200 hours and six months to fix. But in some cases, it can take thousands of hours and years to resolve fully. Several key factors determine the length of the recovery process, but before we review those, let's look at the steps involved in resolving identity theft.
The FTC's IdentityTheft.gov can assist attorneys who counsel identity theft victims. The site provides victims with a personal recovery plan, walking through each step to take. It also provides pre-filed letters and forms to send to credit bureaus, businesses, and debt collectors.
Check your credit card statements and bank account. If you notice any suspicious activity, alert your bank or credit union right away. Run a credit report. U.S. citizens are entitled to a free one every 12 months. Monitor your finances closely.
Identity thieves can also obtain your personal information by stealing your wallet or purse. When this occurs, we recommend that you immediately contact credit card companies, bank, and credit bureaus to let them know of your situation.
Skimmer devices. Thieves can copy your credit card information using a hand held device called a skimmer. Dumpster diving. Printed documents that state private information should be shredded before being thrown away. Mail theft. Internet. Phishing. Pretext Calling. Shoulder Surfing. Card Verification Value Code Requests.
The identified categories are: Physical Theft: examples of this would be dumpster diving, mail theft, skimming, change of address, reshipping, government records, identity consolidation. Technology-Based: examples of this are phishing, pharming, DNS Cache Poisoning, wardriving, spyware, malware and viruses.