New Mexico Identity Theft by Known Imposter Package
Understanding this form package
The New Mexico Identity Theft by Known Imposter Package is designed to assist individuals whose identity has been stolen by someone they know. This comprehensive form package provides essential documents that enable victims to communicate effectively with creditors and other entities to rectify the consequences of identity theft. Unlike other general identity theft packages, this one focuses specifically on cases involving known imposters, ensuring that the communication and actions taken are appropriate to the situation.
Forms you’ll find in this package
- Federal Trade Commission Affidavit regarding Identity Theft
- Identity Theft Contact Table
- Identity Theft Checklist
- Sample Letter to Report False Submission of Information
- Guide for Identity Theft Victims Who Know Their Imposter
- Letter from Identity Theft Victim to Credit Issuer Regarding Known Imposter Identity Theft
- Letter from Known Imposter to Creditor Accepting Responsibility for Accounts, Charges or Debits
- Letter Agreement Between Known Imposter and Victim to Work Out Repayment Plan
- Letter to Law Enforcement to Report Identity Theft by Known Imposter
- Letter to Credit Reporting Company or Bureau Regarding Known Imposter Identity Theft
- Letter to Report Known Imposter Identity Theft to Postal Authorities
- Letter to Report Known Imposter Identity Theft to Social Security Administration
- Letter to Report Known Imposter Identity Theft to Other Entities
- Sample Letter for Request for Free Credit Report Allowed by Federal Law
Situations where these forms applies
This package is beneficial in scenarios such as:
- You have discovered that someone you know has misused your identity, leading to fraudulent accounts or debts.
- You need to formally report identity theft to creditors and law enforcement.
- You are working to resolve discrepancies in your credit reports caused by the known imposter's actions.
- You require documentation to communicate with financial institutions and gain control over your identity and financial records.
Who can use this document
- Individuals who are victims of identity theft by someone they know.
- Anyone looking to clear their name from fraudulent activities linked to their identity by a known imposter.
- Individuals seeking to communicate with creditors and law enforcement regarding identity theft cases.
- Those needing structured documentation to organize their response to identity theft.
How to prepare this document
- Review all included forms to understand each document's purpose.
- Gather necessary personal information and details about the identity theft incident.
- Complete each form by entering the required information, ensuring accuracy and clarity.
- Sign the forms where indicated, and keep copies for your records.
- Submit the completed forms to the relevant creditors, law enforcement, and other entities as outlined in the guide.
Notarization requirements for forms in this package
Notarization is not commonly needed for forms in this package. However, if your state’s laws require it, our notarization service, powered by Notarize, allows you to finalize documents online 24/7 without in-person visits.
Get your form ready online
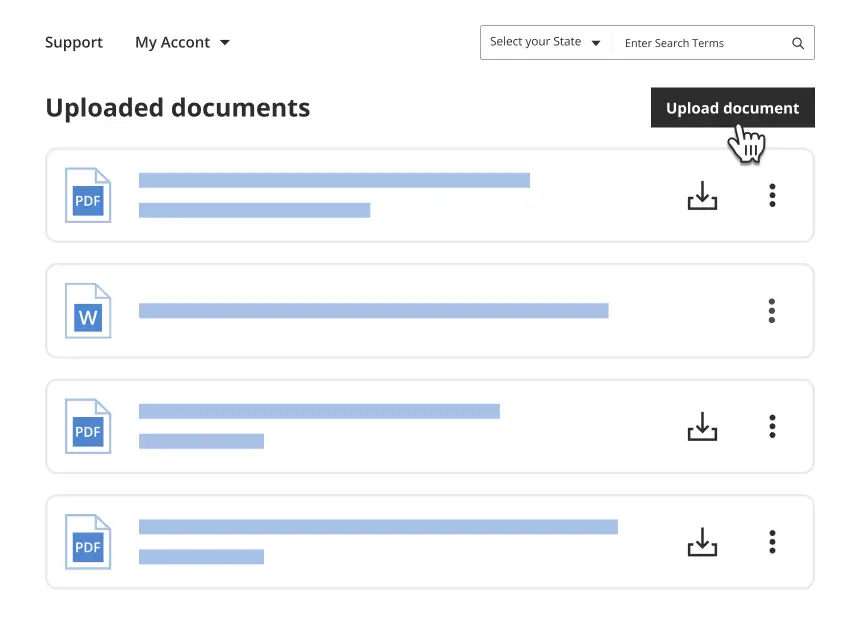
Our built-in tools help you complete, sign, share, and store your documents in one place.
Make edits, fill in missing information, and update formatting in US Legal Forms—just like you would in MS Word.
Download a copy, print it, send it by email, or mail it via USPS—whatever works best for your next step.
Sign and collect signatures with our SignNow integration. Send to multiple recipients, set reminders, and more. Go Premium to unlock E-Sign.
If this form requires notarization, complete it online through a secure video call—no need to meet a notary in person or wait for an appointment.
We protect your documents and personal data by following strict security and privacy standards.
Make edits, fill in missing information, and update formatting in US Legal Forms—just like you would in MS Word.
Download a copy, print it, send it by email, or mail it via USPS—whatever works best for your next step.
Sign and collect signatures with our SignNow integration. Send to multiple recipients, set reminders, and more. Go Premium to unlock E-Sign.
If this form requires notarization, complete it online through a secure video call—no need to meet a notary in person or wait for an appointment.
We protect your documents and personal data by following strict security and privacy standards.
Typical mistakes to avoid
- Failing to provide complete and accurate information on the forms.
- Not keeping copies of submitted documents for personal records.
- Neglecting to follow up with creditors and agencies after submitting forms.
- Overlooking specific instructions that may vary by entity regarding submission formats.
Benefits of using this package online
- Convenience of downloading and completing forms from home.
- Editability, allowing you to make adjustments easily before submission.
- Reliable access to forms drafted by licensed attorneys, ensuring legal validity.
- Comprehensive resources that guide you through each step of the identity theft resolution process.
Legal use & context
- These forms are legally recognized tools to address identity theft and communicate with involved parties.
- Correct usage of these forms can help victims reclaim their identities and mitigate financial damages.
- It is important to adhere to the state-level regulations to ensure the documents hold weight in legal contexts.
What to keep in mind
- This form package is essential for individuals facing identity theft by a known imposter in New Mexico.
- Completing these forms correctly is crucial for managing and mitigating the impact of identity theft.
- Utilizing online resources offers convenience and access to professionally drafted forms tailored for your needs.
Looking for another form?
Form popularity
FAQ
Report Identity Theft. Report identity (ID) theft to the Federal Trade Commission (FTC) online at IdentityTheft.gov or by phone at 1-877-438-4338.
You can call the Federal Trade Commission (FTC) at 1-877-438-4338 or TDD at 1-866-653-4261, or online at http://www.consumer.ftc.gov/features/feature-0014-identity-theft to report identity theft.
Go to your local police office with: Tell the police someone stole your identity and you need to file a report.
Identity thieves can also obtain your personal information by stealing your wallet or purse. When this occurs, we recommend that you immediately contact credit card companies, bank, and credit bureaus to let them know of your situation.
The FTC cannot resolve individual complaints, but it can provide information about what steps to take. The FTC says that complaints can help it and its law enforcement partners detect patterns of fraud and abuse, which may lead to investigations and stopping unfair business practices.
File a claim with your identity theft insurance, if applicable. Notify companies of your stolen identity. File a report with the FTC. Contact your local police department. Place a fraud alert on your credit reports. Freeze your credit. Sign up for a credit monitoring service, if offered.
The FTC's IdentityTheft.gov can assist attorneys who counsel identity theft victims. The site provides victims with a personal recovery plan, walking through each step to take. It also provides pre-filed letters and forms to send to credit bureaus, businesses, and debt collectors.
You may be able to have your identity theft charges dropped if: You didn't obtain use a person's information unlawfully If you did not obtain or use someone else's personal information unlawfully, you are not guilty of identity theft.
Skimmer devices. Thieves can copy your credit card information using a hand held device called a skimmer. Dumpster diving. Printed documents that state private information should be shredded before being thrown away. Mail theft. Internet. Phishing. Pretext Calling. Shoulder Surfing. Card Verification Value Code Requests.