Vendor's Obligation to Protect Nonpublic Confidential Information
Overview of this form
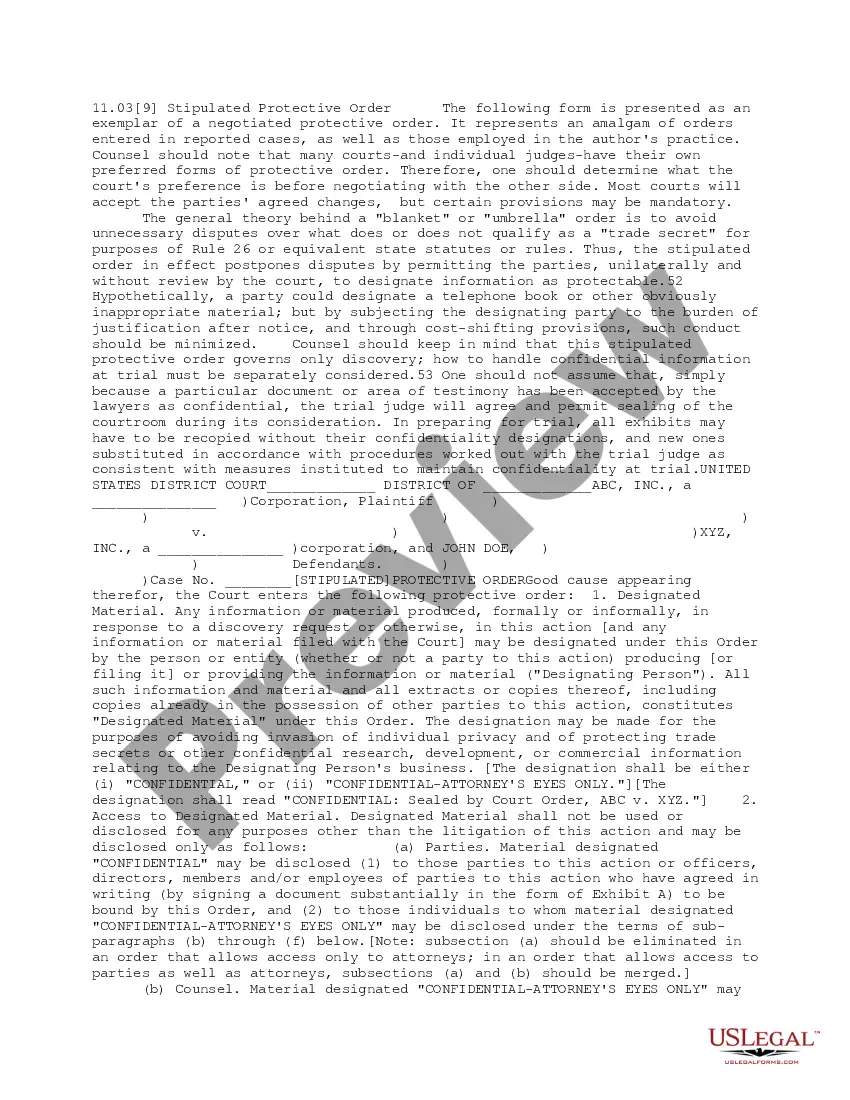
The Vendor's Obligation to Protect Nonpublic Confidential Information form is a legal agreement that establishes a vendor's duty to protect sensitive information acquired during the course of its business relationship with a client. This form is crucial in ensuring that personal or confidential information remains secure, distinguishing it from other general vendor agreements by explicitly addressing nonpublic confidential information and compliance with relevant laws such as the Gramm-Leach-Bliley Act.
Key parts of this document
- Definition of nonpublic personal information (NPI) and its legal significance.
- Vendor's obligation to maintain confidentiality and implement security measures for NPI.
- Procedures for notifying the client of any breaches or unauthorized access to NPI.
- Right of the client to review the vendor's security policies and procedures.
- Instructions for the return and destruction of NPI upon termination of the agreement.
Situations where this form applies
This form should be used when a business engages a vendor who will have access to sensitive client information. It is particularly important for companies in sectors such as finance, healthcare, and legal services, where protecting personal information is crucial for compliance with federal laws and building trust with clients.
Who can use this document
- Businesses working with third-party vendors that handle sensitive client information.
- Organizations in regulated industries such as banking, insurance, and healthcare.
- Any company seeking to solidify legal protections related to nonpublic confidential information.
Instructions for completing this form
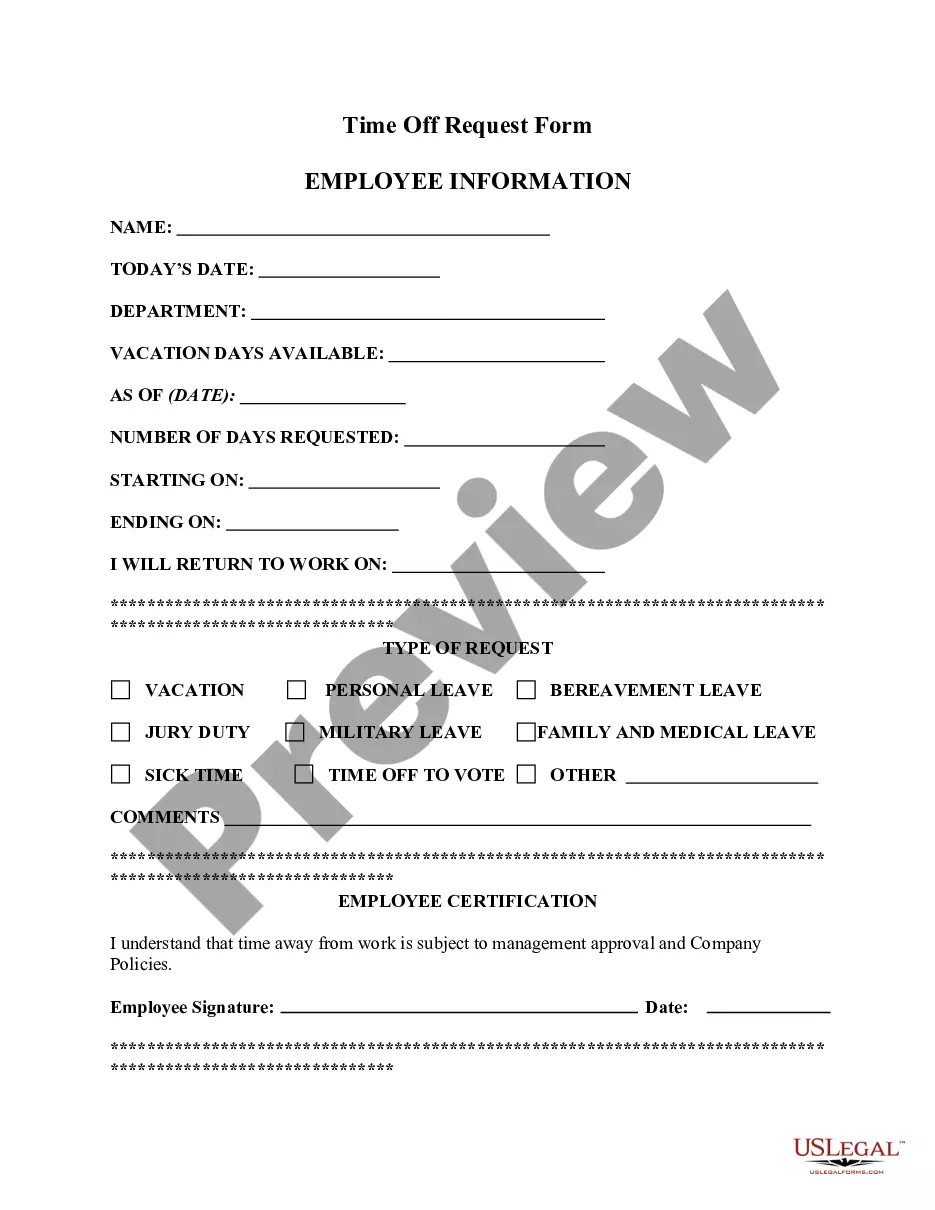
- Identify the parties involved in the agreementânamely the vendor and the client.
- Review and understand the definition of nonpublic personal information as it pertains to your business operations.
- Fill in the necessary terms regarding confidentiality and security measures for the vendor.
- Specify procedures for breach notifications and the timeframe for acting on such notifications.
- Ensure both parties sign and date the form to finalize the agreement.
Notarization requirements for this form
Notarization is not commonly needed for this form. However, certain documents or local rules may make it necessary. Our notarization service, powered by Notarize, allows you to finalize it securely online anytime, day or night.
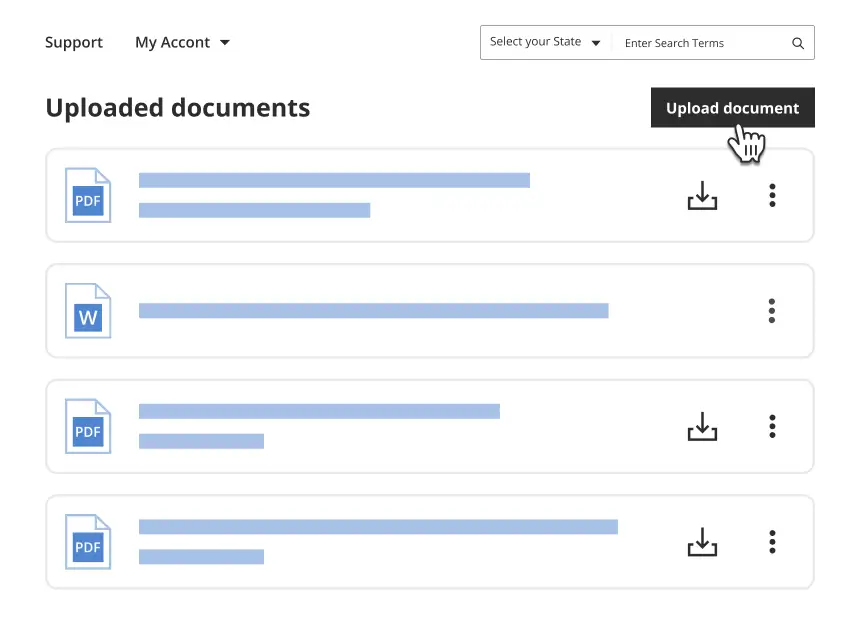
Get your form ready online
Our built-in tools help you complete, sign, share, and store your documents in one place.
Make edits, fill in missing information, and update formatting in US Legal Forms—just like you would in MS Word.
Download a copy, print it, send it by email, or mail it via USPS—whatever works best for your next step.
Sign and collect signatures with our SignNow integration. Send to multiple recipients, set reminders, and more. Go Premium to unlock E-Sign.
If this form requires notarization, complete it online through a secure video call—no need to meet a notary in person or wait for an appointment.
We protect your documents and personal data by following strict security and privacy standards.
Make edits, fill in missing information, and update formatting in US Legal Forms—just like you would in MS Word.
Download a copy, print it, send it by email, or mail it via USPS—whatever works best for your next step.
Sign and collect signatures with our SignNow integration. Send to multiple recipients, set reminders, and more. Go Premium to unlock E-Sign.
If this form requires notarization, complete it online through a secure video call—no need to meet a notary in person or wait for an appointment.
We protect your documents and personal data by following strict security and privacy standards.
Avoid these common issues
- Failing to clearly define what constitutes nonpublic personal information.
- Not including adequate security measures that the vendor must implement.
- Neglecting to specify the notification process for breaches of confidentiality.
- Overlooking the requirement for both parties' signatures, which may invalidate the agreement.
Why use this form online
- Convenience of downloading and editing the form to meet specific business needs.
- Access to legal templates drafted by licensed attorneys for accuracy and compliance.
- Time-saving, as the online format allows for quick completion and record-keeping.
Legal use & context
- The form establishes clear responsibilities and obligations for vendors, which is crucial for enforcing data protection standards.
- Using this form can protect your organization against data breaches and associated legal liabilities.
What to keep in mind
- The Vendor's Obligation to Protect Nonpublic Confidential Information form is essential for safeguarding sensitive client data.
- Compliance with applicable laws, such as the Gramm-Leach-Bliley Act, is critical for vendors handling personal information.
- Clear procedures and definitions in the agreement help mitigate risks associated with data breaches.
Looking for another form?
Form popularity
FAQ
As part of your GLBA compliance requirement, you are required to meet the three sections of the Act. These sections include The Financial Rule, The Safeguards Rule, and The Pretexting Provisions.
The Act consists of three sections: The Financial Privacy Rule, which regulates the collection and disclosure of private financial information; the Safeguards Rule, which stipulates that financial institutions must implement security programs to protect such information; and the Pretexting provisions, which prohibit
Routine Precautions to Protect Confidentiality. Certificates of Confidentiality. Waivers of Documentation of Informed Consent. Data Use and Materials Transfer Agreements. IRB Review of Confidentiality Protections. Unauthorized Disclosure of Information.
2606Proper labelling. 2606Insert non-disclosure provisions in employment agreements. 2606Check out other agreements for confidentiality provisions. 2606Limit access.
All confidential documents should be stored in locked file cabinets or rooms accessible only to those who have a business need-to-know.All confidential information should be disposed of properly (e.g., employees should not print out a confidential document and then throw it away without shredding it first.)
Know who you are disclosing information to. Clearly label all confidential information as confidential. Use passwords and encrypted files for electronic documents. Provide initial and ongoing advice to individuals. Keep records of what information has been disclosed.
The Gramm-Leach-Bliley Act requires financial institutions companies that offer consumers financial products or services like loans, financial or investment advice, or insurance to explain their information-sharing practices to their customers and to safeguard sensitive data.
Proper labelling. Insert non-disclosure provisions in employment agreements. Check out other agreements for confidentiality provisions. Limit access. Add a confidentiality policy to the employee handbook. Exit interview for departing employees. Consider notifying the new employer.
Under the law, agencies enforce the Financial Privacy Rule, which governs how financial institutions can collect and disclose customers' personal financial information; the Safeguards Rule, which requires all financial institutions to maintain safeguards to protect customer information; and another provision designed