South Carolina Ethical Hacking Agreement for External Network Security - Unannounced Penetration Test
Description
Get your form ready online
Our built-in tools help you complete, sign, share, and store your documents in one place.
Make edits, fill in missing information, and update formatting in US Legal Forms—just like you would in MS Word.
Download a copy, print it, send it by email, or mail it via USPS—whatever works best for your next step.
Sign and collect signatures with our SignNow integration. Send to multiple recipients, set reminders, and more. Go Premium to unlock E-Sign.
If this form requires notarization, complete it online through a secure video call—no need to meet a notary in person or wait for an appointment.
We protect your documents and personal data by following strict security and privacy standards.
Make edits, fill in missing information, and update formatting in US Legal Forms—just like you would in MS Word.
Download a copy, print it, send it by email, or mail it via USPS—whatever works best for your next step.
Sign and collect signatures with our SignNow integration. Send to multiple recipients, set reminders, and more. Go Premium to unlock E-Sign.
If this form requires notarization, complete it online through a secure video call—no need to meet a notary in person or wait for an appointment.
We protect your documents and personal data by following strict security and privacy standards.
Looking for another form?
How to fill out Ethical Hacking Agreement For External Network Security - Unannounced Penetration Test?
Selecting the optimal genuine document format can be challenging.
Clearly, there are numerous templates available online, but how can you locate the authentic type you require.
Utilize the US Legal Forms website.
If you are a new user of US Legal Forms, here are easy steps for you to follow: First, ensure you have chosen the correct form for your city/region. You can browse the template using the Review button and read the form description to confirm it is indeed suitable for you.
- The service offers thousands of templates, including the South Carolina Ethical Hacking Agreement for External Network Security - Unannounced Penetration Test, that can be utilized for business and personal purposes.
- All of the documents are reviewed by professionals and comply with federal and state regulations.
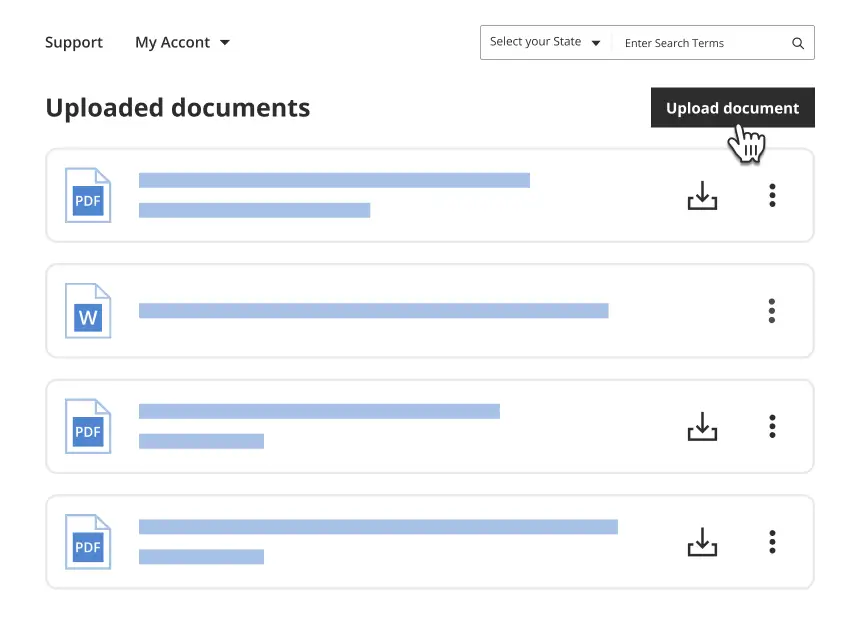
- If you are already registered, Log In to your account and click the Acquire button to find the South Carolina Ethical Hacking Agreement for External Network Security - Unannounced Penetration Test.
- Use your account to check for the legitimate forms you may have purchased previously.
- Navigate to the My documents section of your account and obtain another copy of the document you need.
Form popularity
FAQ
A blue hat hacker is an individual who is primarily a security expert but may not work as a full-time professional hacker. They often engage in external penetration testing to identify vulnerabilities within their own organization's systems. These hackers typically operate under agreements similar to the South Carolina Ethical Hacking Agreement for External Network Security - Unannounced Penetration Test, aimed at enhancing security measures. Their role is critical in preventing malicious attacks and strengthening overall network resilience.
The average salary of a white hat hacker can vary significantly based on experience, location, and expertise. In the United States, white hat hackers typically earn between $70,000 and $120,000 per year. Those engaged in specialized roles, such as conducting South Carolina Ethical Hacking Agreements for External Network Security - Unannounced Penetration Tests, may command even higher compensation. As the demand for cybersecurity professionals continues to grow, so does the earning potential in this field.
A quality test should include various aspects to ensure its effectiveness, especially in the context of the South Carolina Ethical Hacking Agreement for External Network Security - Unannounced Penetration Test. Key components are reconnaissance, vulnerability scanning, exploitation of found vulnerabilities, and thorough documentation of findings. Each aspect serves to provide a comprehensive analysis of the organization's security weaknesses and helps formulate a strategic response.
structured testing agreement typically consists of three main sections: scope of work, legal liabilities, and confidentiality clauses. The scope of work clarifies what systems or networks will be tested and the methods to be used. Legal liabilities protect both parties and set forth expectations regarding damage, while confidentiality clauses ensure that sensitive information remains secure throughout the testing process.
Ethical and legal considerations for testing involve adhering to established guidelines and laws, especially as outlined in the South Carolina Ethical Hacking Agreement for External Network Security - Unannounced Penetration Test. Ethical hackers must obtain proper authorization to avoid legal troubles, as unauthorized access can lead to severe consequences. Upholding privacy, confidentiality, and the integrity of data throughout the testing process is paramount.
A test agreement is a formal document outlining the terms and conditions for conducting a penetration test, such as the South Carolina Ethical Hacking Agreement for External Network Security - Unannounced Penetration Test. This agreement establishes the rights and responsibilities of both the organization and the ethical hacker. It also sets clear boundaries for what will be tested and ensures legal protection for both parties involved.
The test contract should include essential documents such as the South Carolina Ethical Hacking Agreement for External Network Security - Unannounced Penetration Test, Non-Disclosure Agreements (NDAs), and any necessary permissions from stakeholders. Additionally, including a clear definition of roles and responsibilities for both parties helps in minimizing confusion. Ensuring all documentation is complete fosters smoother communication.
A pentest report should comprehensively cover findings from the South Carolina Ethical Hacking Agreement for External Network Security - Unannounced Penetration Test. Key elements include an executive summary, detailed vulnerability descriptions, evidence of findings, and actionable recommendations for remediation. Conclusion and future recommendations also guide the organization in strengthening its security posture.
An ethical hacker can begin the test after all parties have signed the South Carolina Ethical Hacking Agreement for External Network Security - Unannounced Penetration Test. It is essential to ensure that all prerequisites are fulfilled, which includes a clear understanding of the schedule and logistics. The start date should also align with the agreed timeline outlined in the contract to mitigate risks.
A comprehensive South Carolina Ethical Hacking Agreement for External Network Security - Unannounced Penetration Test should include several critical components. Firstly, the scope of the test must be defined clearly to set boundaries and expectations. Additionally, clauses regarding confidentiality, liability, and reporting are vital to protect both parties and ensure compliance with legal requirements.