New Hampshire Ethical Hacking Agreement for External Network Security - Unannounced Penetration Test
Description
Get your form ready online
Our built-in tools help you complete, sign, share, and store your documents in one place.
Make edits, fill in missing information, and update formatting in US Legal Forms—just like you would in MS Word.
Download a copy, print it, send it by email, or mail it via USPS—whatever works best for your next step.
Sign and collect signatures with our SignNow integration. Send to multiple recipients, set reminders, and more. Go Premium to unlock E-Sign.
If this form requires notarization, complete it online through a secure video call—no need to meet a notary in person or wait for an appointment.
We protect your documents and personal data by following strict security and privacy standards.
Make edits, fill in missing information, and update formatting in US Legal Forms—just like you would in MS Word.
Download a copy, print it, send it by email, or mail it via USPS—whatever works best for your next step.
Sign and collect signatures with our SignNow integration. Send to multiple recipients, set reminders, and more. Go Premium to unlock E-Sign.
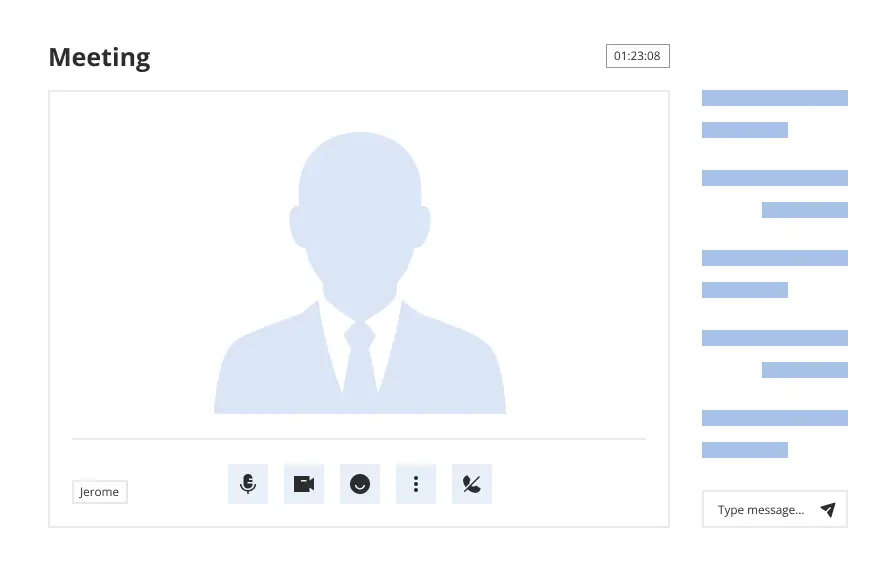
If this form requires notarization, complete it online through a secure video call—no need to meet a notary in person or wait for an appointment.
We protect your documents and personal data by following strict security and privacy standards.
Looking for another form?
How to fill out Ethical Hacking Agreement For External Network Security - Unannounced Penetration Test?
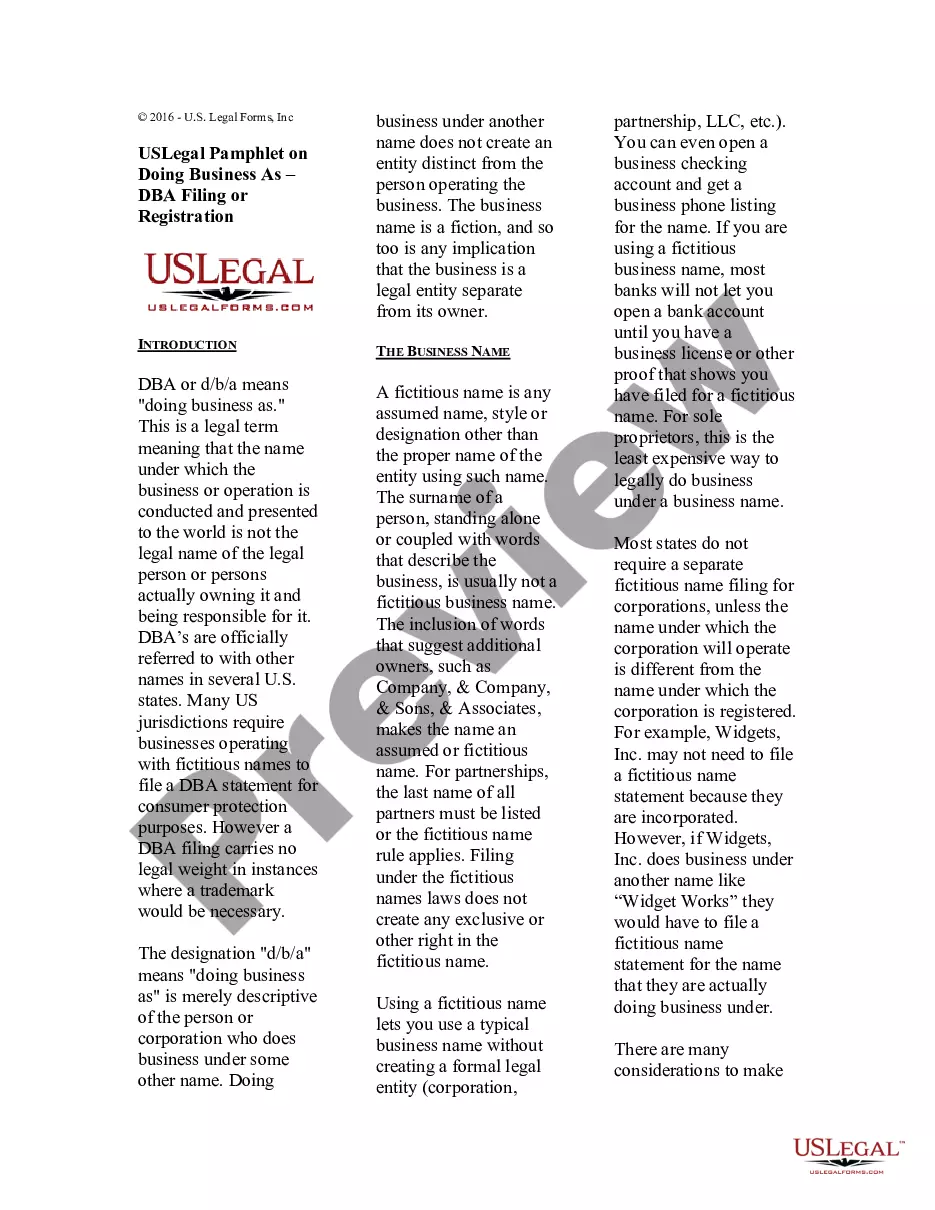
If you wish to compile, download, or print authorized document templates, utilize US Legal Forms, the largest assortment of legal documents available online.
Leverage the site’s simple and user-friendly search to locate the paperwork you require.
A variety of templates for business and personal purposes are organized by categories and jurisdictions, or keywords.
Step 5. Process the transaction. You may use your Visa or MasterCard or PayPal account to complete the transaction.
Step 6. Choose the format of the legal form and download it to your device.Step 7. Fill out, edit, and print or sign the New Hampshire Ethical Hacking Agreement for External Network Security - Unannounced Penetration Test.
- Utilize US Legal Forms to locate the New Hampshire Ethical Hacking Agreement for External Network Security - Unannounced Penetration Test with just a few clicks.
- If you are already a US Legal Forms user, Log In to your account and click on the Download button to receive the New Hampshire Ethical Hacking Agreement for External Network Security - Unannounced Penetration Test.
- You can also access documents you previously downloaded within the My documents tab of your account.
- If you are using US Legal Forms for the first time, follow the instructions below.
- Step 1. Ensure you have chosen the form for the appropriate city/state.
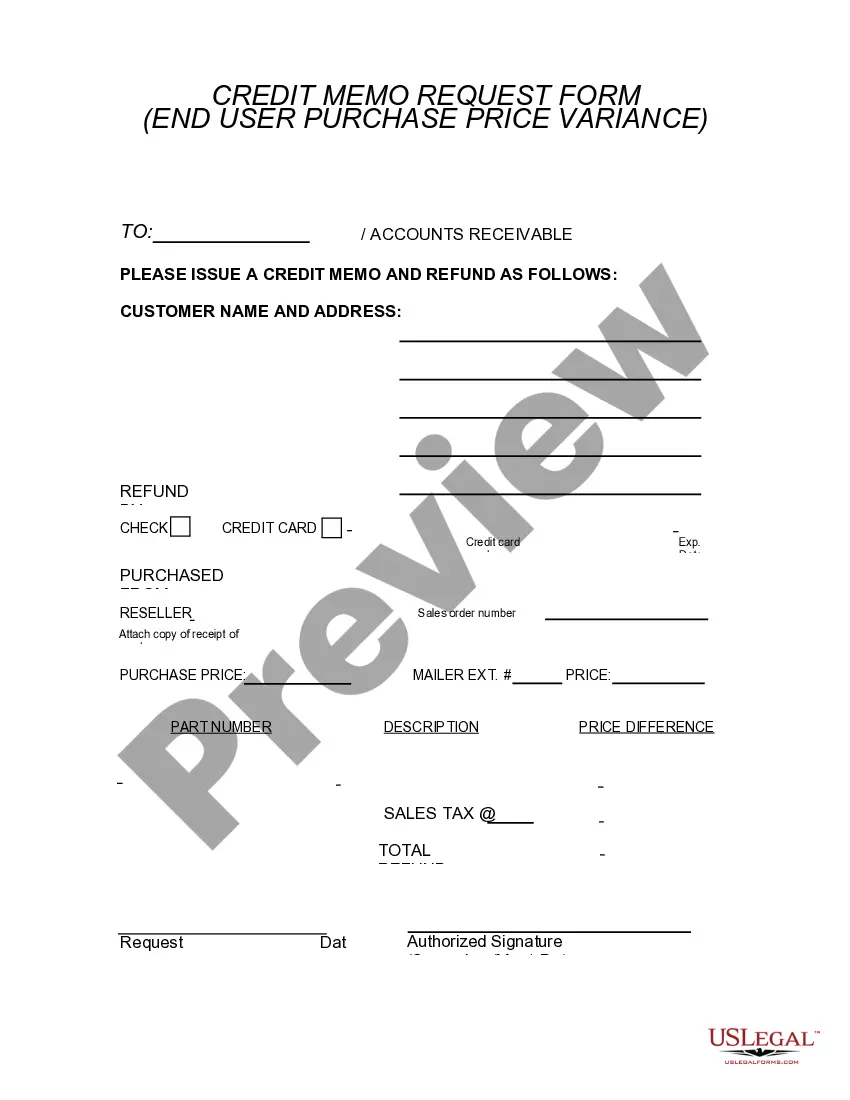
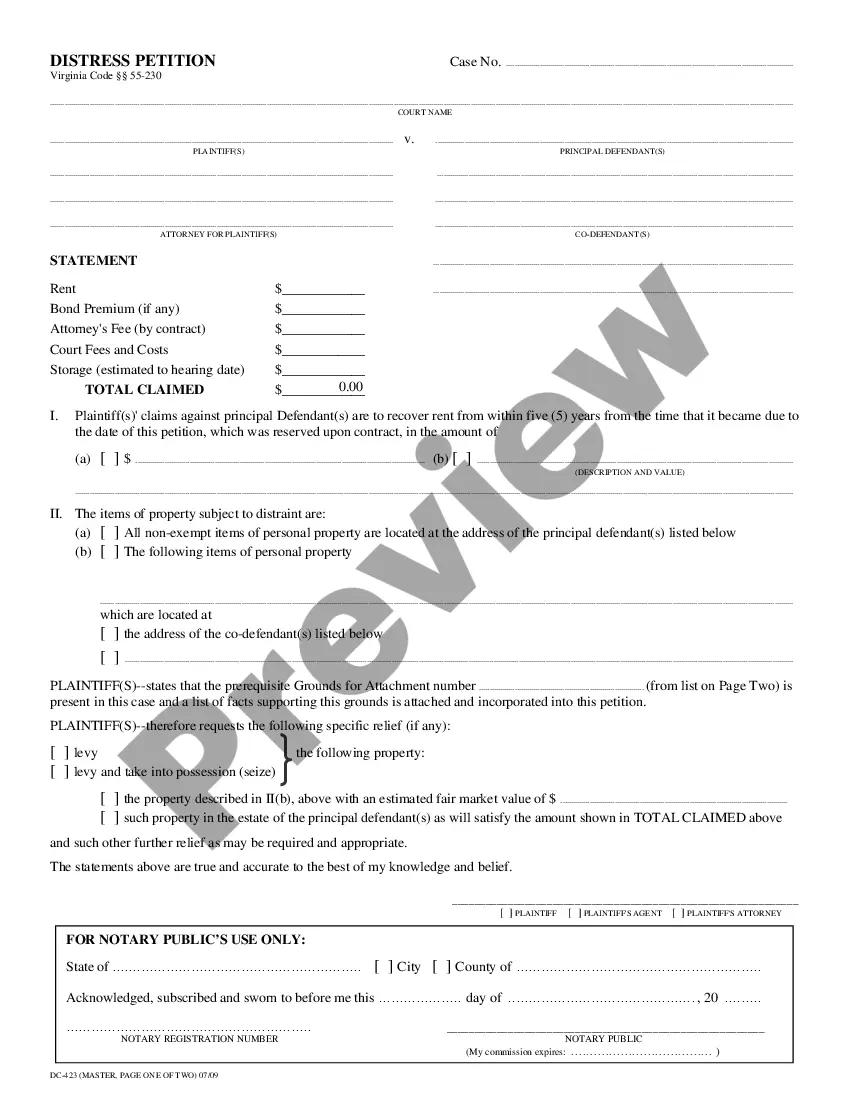
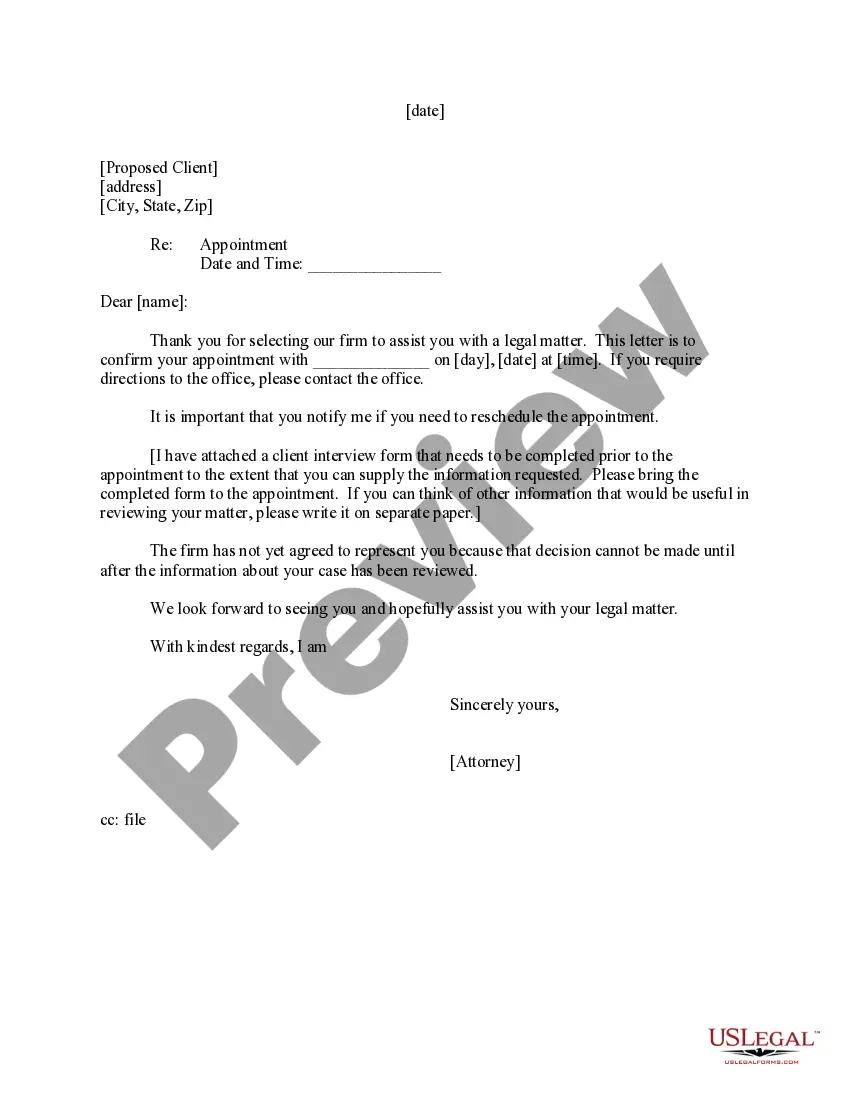
- Step 2. Use the Preview option to review the form's content. Don’t forget to read the description.
- Step 3. If you are dissatisfied with the form, utilize the Search field at the top of the screen to find alternative versions of the legal form template.
- Step 4. Once you find the form you require, click on the Get Now button. Select your preferred pricing plan and enter your credentials to register for an account.
Form popularity
FAQ
Ethical hacking and testing serve different purposes in the realm of cybersecurity. Ethical hacking aims to proactively identify vulnerabilities by simulating real-world attacks, which adheres to the guidelines of the New Hampshire Ethical Hacking Agreement for External Network Security - Unannounced Penetration Test. On the other hand, testing typically focuses on assessing the functionality or performance of a system. While both processes aim to enhance security, ethical hacking provides deeper insights into potential threats.
Ethical hacking involves five key steps that ensure a thorough examination of network security. First, you define the scope of the New Hampshire Ethical Hacking Agreement for External Network Security - Unannounced Penetration Test. Next, you gather information to understand the system’s vulnerabilities. Then, you conduct the tests to simulate a potential attack. After this, you analyze the findings to identify security weaknesses. Finally, you report the results, providing actionable recommendations to strengthen security measures.
To conduct a penetration test legally, an ethical hacker requires a signed agreement detailing the scope, limitations, and potential impact of their activities. This formal documentation protects both parties and establishes trust. A New Hampshire Ethical Hacking Agreement for External Network Security - Unannounced Penetration Test addresses these requirements comprehensively.
An ethical hacker can commence testing only after receiving explicit authorization from the organization. This ensures there is no misunderstanding about the scope and objectives. The New Hampshire Ethical Hacking Agreement for External Network Security - Unannounced Penetration Test outlines the timeline and parameters to ensure a smooth start.
Ethical considerations include honesty, integrity, and respect for user privacy. Legally, ethical hackers must comply with laws and regulations regarding unauthorized access. Adhering to a New Hampshire Ethical Hacking Agreement for External Network Security - Unannounced Penetration Test ensures that all actions taken are both ethical and lawful.
To become an ethical hacker, one typically needs knowledge of networking, programming, and security protocols. Certifications like Certified Ethical Hacker (CEH) are often advantageous. Engaging in a New Hampshire Ethical Hacking Agreement for External Network Security - Unannounced Penetration Test equips ethical hackers with practical experience and enhances their credibility.
Yes, ethical hackers must have permission to conduct tests on a network. Without explicit consent, their actions can be considered illegal. A formal New Hampshire Ethical Hacking Agreement for External Network Security - Unannounced Penetration Test clearly outlines the scope of work and protects both parties involved.
Network enumeration is the process of discovering all the devices on a network. This step provides a hacker with vital information about devices, their configurations, and potential vulnerabilities. By employing a New Hampshire Ethical Hacking Agreement for External Network Security - Unannounced Penetration Test, organizations can conduct thorough assessments to ensure their networks are secure.
Yes, hackers can exploit vulnerabilities to gain unauthorized access. However, having a robust security system reduces the risk significantly. Implementing a New Hampshire Ethical Hacking Agreement for External Network Security - Unannounced Penetration Test helps identify these weaknesses before an attacker can.
Testing and ethical hacking share similarities, but they are not entirely the same. Testing mainly focuses on verifying system functionality without delving into security vulnerabilities. In contrast, ethical hacking involves identifying, exploiting, and recommending fixes for security flaws under a New Hampshire Ethical Hacking Agreement for External Network Security. By having clear objectives, both approaches play essential roles in an organization's overall security strategy.