This document is an important policy for a company that relies on its information assets and computer resources to conduct and support its business operations with its customers, employees and suppliers. It seeks to protect business development information, manufacturing and operation information, software and product development, and data security.
Kentucky Employee Policy for Information Security
Description
How to fill out Employee Policy For Information Security?
It is possible to invest hours on the Internet attempting to find the legitimate file template that meets the federal and state needs you want. US Legal Forms gives 1000s of legitimate kinds which are evaluated by pros. It is simple to down load or printing the Kentucky Employee Policy for Information Security from your service.
If you have a US Legal Forms accounts, you can log in and click on the Down load switch. Afterward, you can comprehensive, revise, printing, or indicator the Kentucky Employee Policy for Information Security. Every single legitimate file template you purchase is your own eternally. To acquire another duplicate associated with a purchased type, proceed to the My Forms tab and click on the related switch.
If you are using the US Legal Forms site initially, follow the straightforward directions listed below:
- Initially, ensure that you have chosen the best file template for the region/metropolis of your choice. Look at the type outline to ensure you have chosen the proper type. If offered, use the Preview switch to check from the file template as well.
- If you would like locate another edition of the type, use the Search industry to get the template that meets your requirements and needs.
- After you have located the template you desire, simply click Get now to continue.
- Pick the costs program you desire, type your accreditations, and sign up for a free account on US Legal Forms.
- Complete the financial transaction. You should use your charge card or PayPal accounts to cover the legitimate type.
- Pick the file format of the file and down load it to your product.
- Make adjustments to your file if possible. It is possible to comprehensive, revise and indicator and printing Kentucky Employee Policy for Information Security.
Down load and printing 1000s of file themes using the US Legal Forms website, that offers the largest collection of legitimate kinds. Use professional and state-certain themes to handle your business or specific requires.
Form popularity
FAQ
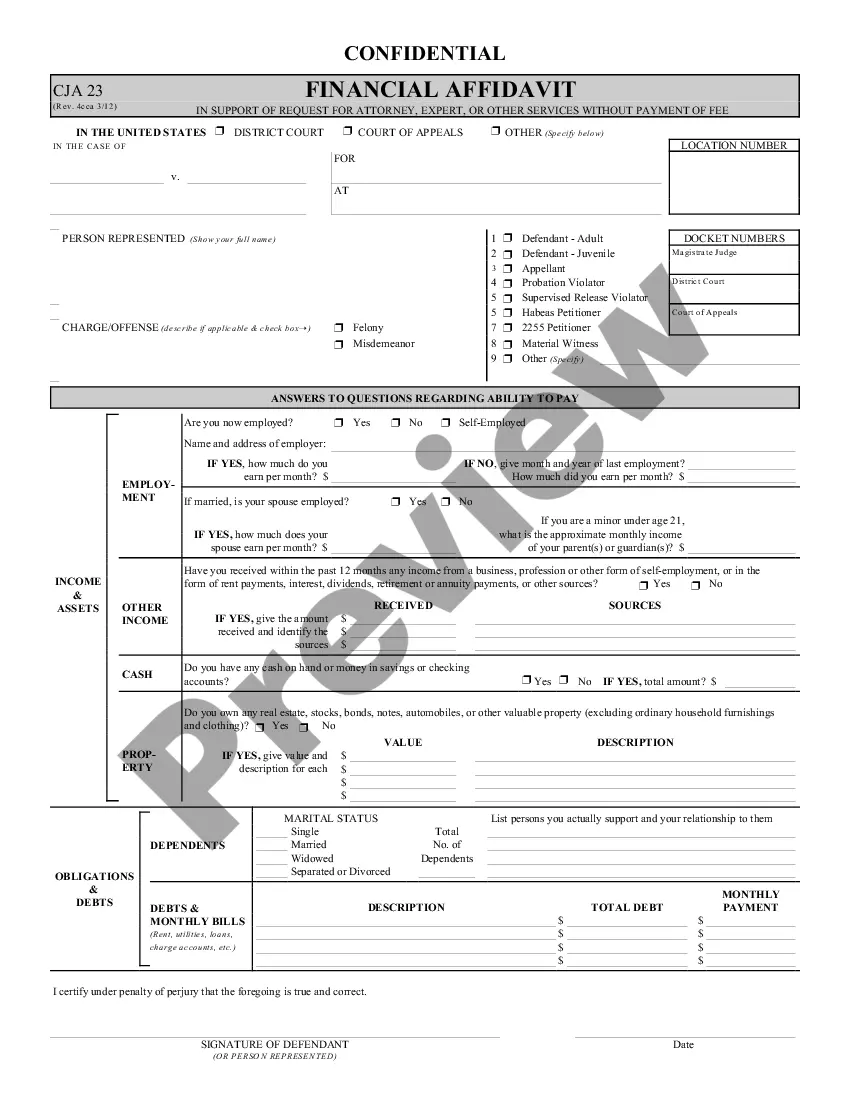
The basic tenets of information security are confidentiality, integrity and availability. Every element of the information security program must be designed to implement one or more of these principles. Together they are called the CIA Triad.
An IT Security Policy identifies the rules and procedures for all individuals accessing and using an organization's IT assets and resources. An Information Technology (IT) Security Policy identifies the rules and procedures for all individuals accessing and using an organization's IT assets and resources.
Minimizes the risk of security incidents ? An information security policy helps organizations define procedures for identifying and mitigating vulnerabilities and risks. It also details quick responses to minimize damage during a security incident.
An information security policy (ISP) is a set of rules, policies and procedures designed to ensure all end users and networks within an organization meet minimum IT security and data protection security requirements.
Information and cyber security policies ensure that IT resources efficiently serve the primary business functions, provide security for members' electronic data, and comply with federal and other regulations. Security policies are an integral and critical component of daily business.
A: Three types of security policies in common use are program policies, issue-specific policies, and system-specific policies.
Defining a cybersecurity policy Cybersecurity procedures explain the rules for how employees, consultants, partners, board members, and other end-users access online applications and internet resources, send data over networks, and otherwise practice responsible security.
An information security policy establishes an organisation's aims and objectives on various security concerns. For example, a policy might outline rules for creating passwords or state that portable devices must be protected when out of the premises.