Invasion Transmit Privacy With Technology
Description
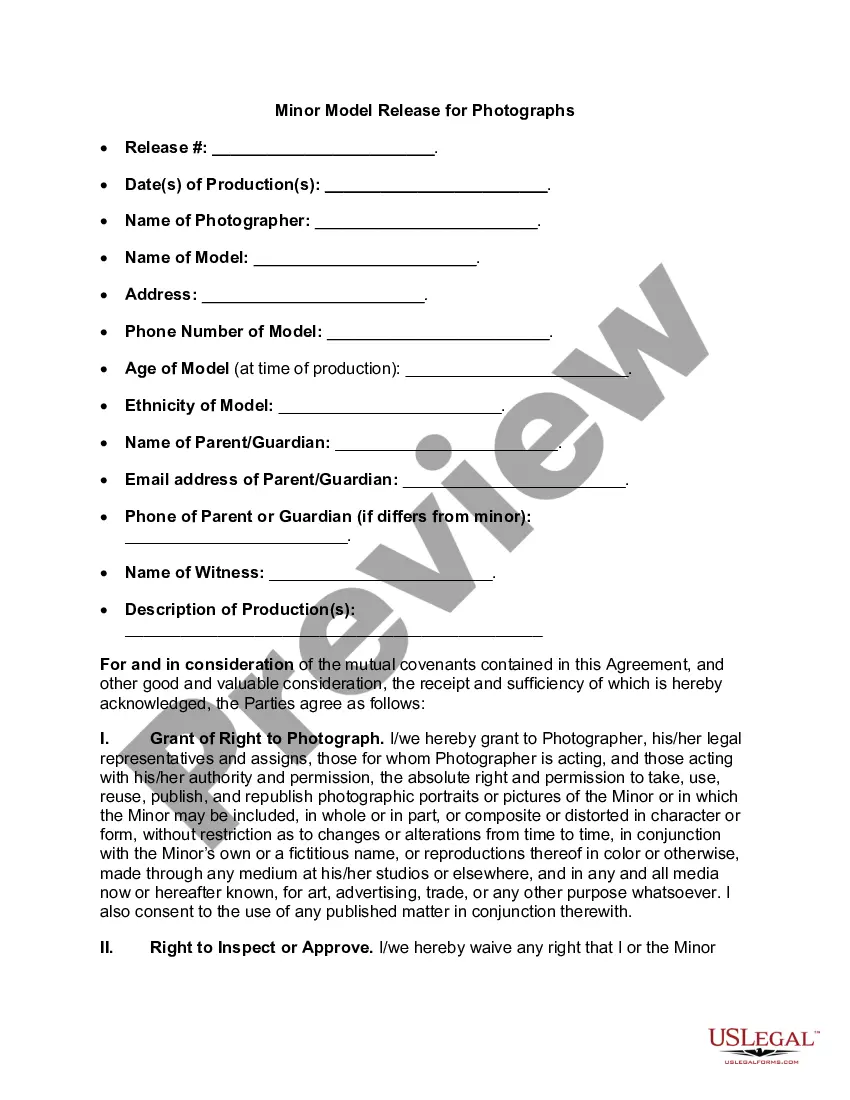
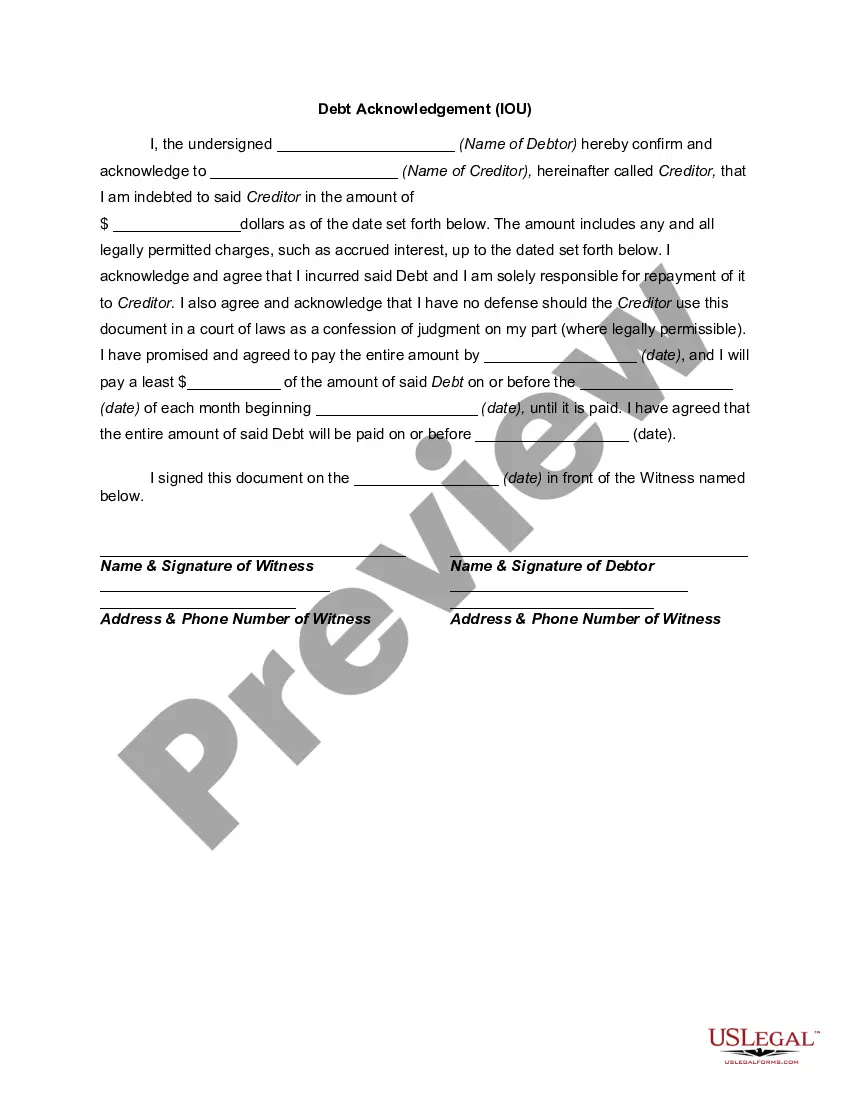
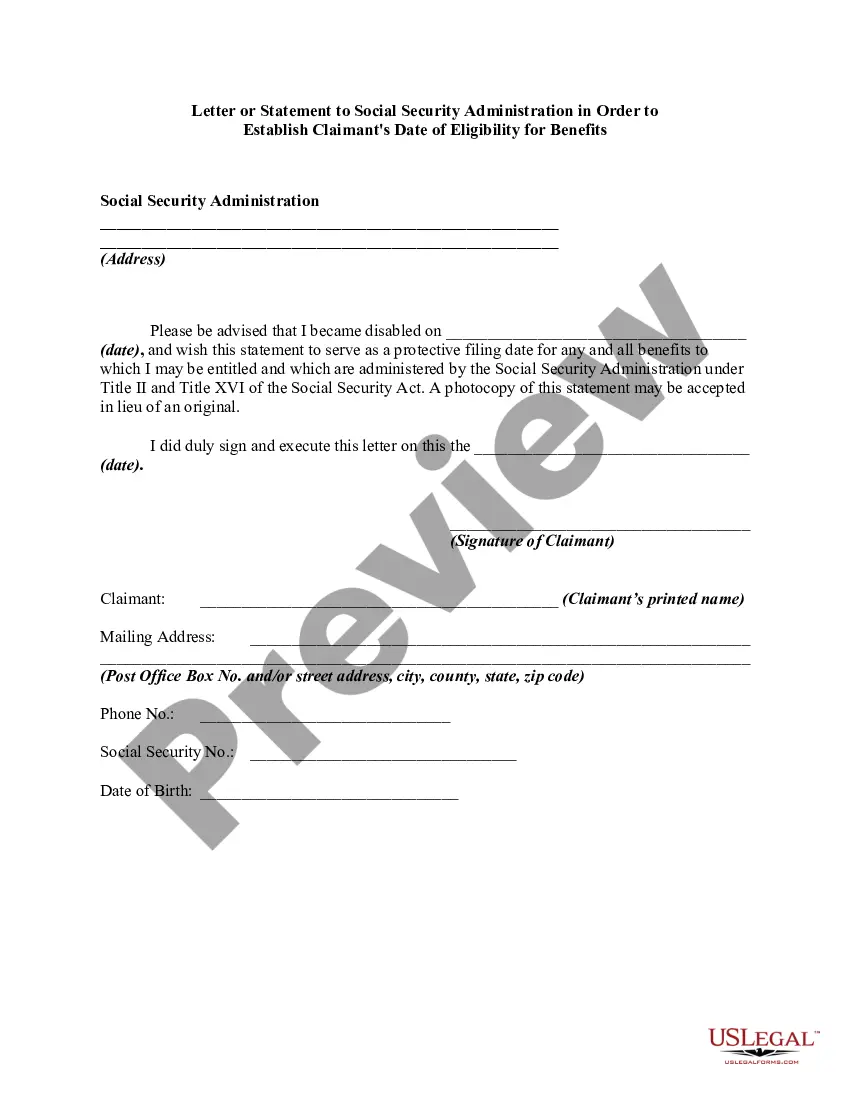
How to fill out Release By Model For Images Included In Web Site?
It’s clear that you cannot instantly become a legal expert, nor can you swiftly learn how to draft Invasion Transmit Privacy With Technology without a specialized skill set.
Creating legal documents is a lengthy endeavor that necessitates specific training and expertise.
So why not entrust the preparation of the Invasion Transmit Privacy With Technology to the professionals.
Preview it (if this option is available) and review the accompanying description to see if Invasion Transmit Privacy With Technology is what you are seeking.
Begin your search again if you need another template. Sign up for a free account and select a subscription plan to buy the template. Click Buy now. After the payment is processed, you can download the Invasion Transmit Privacy With Technology, complete it, print it, and send or mail it to the necessary individuals or organizations. You can access your documents again from the My documents tab at any time. If you are an existing customer, you can simply Log In and find and download the template from the same tab. Regardless of the purpose of your forms—whether financial, legal, or personal—our website has you covered. Try US Legal Forms today!
- With US Legal Forms, one of the most extensive legal template collections, you can access everything from court documents to templates for internal corporate communications.
- We understand how vital compliance and adherence to federal and local regulations are.
- That’s why, on our site, all templates are location-specific and current.
- Here’s how to start with our website and obtain the form you need in just a few minutes.
- Find the document you require using the search bar at the top of the page.
Form popularity
FAQ
Technology can invade privacy in numerous ways, such as through surveillance cameras, tracking software, or data breaches. These tools can gather, store, and share personal information without consent, often leading to significant privacy violations. As our world becomes more digital, recognizing the potential risks is essential. US Legal provides insights into your rights and how to address privacy issues effectively.
To establish a case for invasion of privacy, you need to provide evidence of the intrusion and demonstrate that it caused harm or distress. This often involves showing a reasonable expectation of privacy in the situation. Additionally, understanding how technology can transmit privacy violations is key to building your case. US Legal offers resources to help you compile necessary documentation and navigate legal complexities.
Invasion of privacy occurs when someone violates your personal space or privacy rights without your consent. This can include unauthorized surveillance, sharing private information, or using technology to monitor your actions. Each situation is unique, and understanding how technology can invade privacy is crucial. Seeking legal guidance through US Legal can help clarify your specific circumstances.
To prove invasion of privacy, you must demonstrate that someone intentionally intruded upon your private affairs, which would be considered highly offensive. This can involve collecting evidence such as communications, photographs, or witness statements. In cases where technology is involved, you may need to show how devices or software facilitated this invasion. Utilizing platforms like US Legal can guide you through the legal process to assert your rights.
Technology invades our privacy in various ways, often without our awareness. Devices like smartphones and smart home systems collect personal data that can be accessed by companies or hackers. Additionally, social media platforms track our online behavior, leading to targeted ads that may feel intrusive. To protect your privacy, it's crucial to understand these risks and utilize tools that help safeguard your information, such as those offered by US Legal Forms.
Various methods, including pseudonymization, obfuscation and data masking, can be used to replace or obscure sensitive information by interchanging sensitive data with fictitious, distracting or misleading data. This is a common practice used by businesses to protect users' sensitive data and comply with privacy laws.
Technological innovation has outpaced our privacy protections. As a result, our digital footprint can be tracked by the government and corporations in ways that were once unthinkable. This digital footprint is constantly growing, containing more and more data about the most intimate aspects of our lives.
For example, if you tape a private customer conversation without approval and use the remarks on your website, you could face an invasion of privacy lawsuit. Portraying someone in a false light. This occurs if something you say or publish puts a person in a negative light.
A virtual private network (VPN) encrypts your internet traffic so that no one can track what you do or see where you've been. Using a VPN can also protect you from hackers when using public Wi-Fi networks. Here's how you can protect your privacy while browsing online: Use a VPN when off of your home network.
Examples of PETs include the following: Pseudonymization: A data management and de-identification procedure by which fields containing information that enables the identification of an individual (identifiers) are replaced by one or more artificial identifiers, or pseudonyms.