Vendor Hipaa Agreement With Oracle
Description
How to fill out HIPAA Business Associates Agreement?
Whether for business purposes or for individual matters, everybody has to deal with legal situations at some point in their life. Filling out legal paperwork demands careful attention, beginning from choosing the proper form sample. For instance, when you choose a wrong edition of a Vendor Hipaa Agreement With Oracle, it will be rejected when you send it. It is therefore important to get a dependable source of legal papers like US Legal Forms.
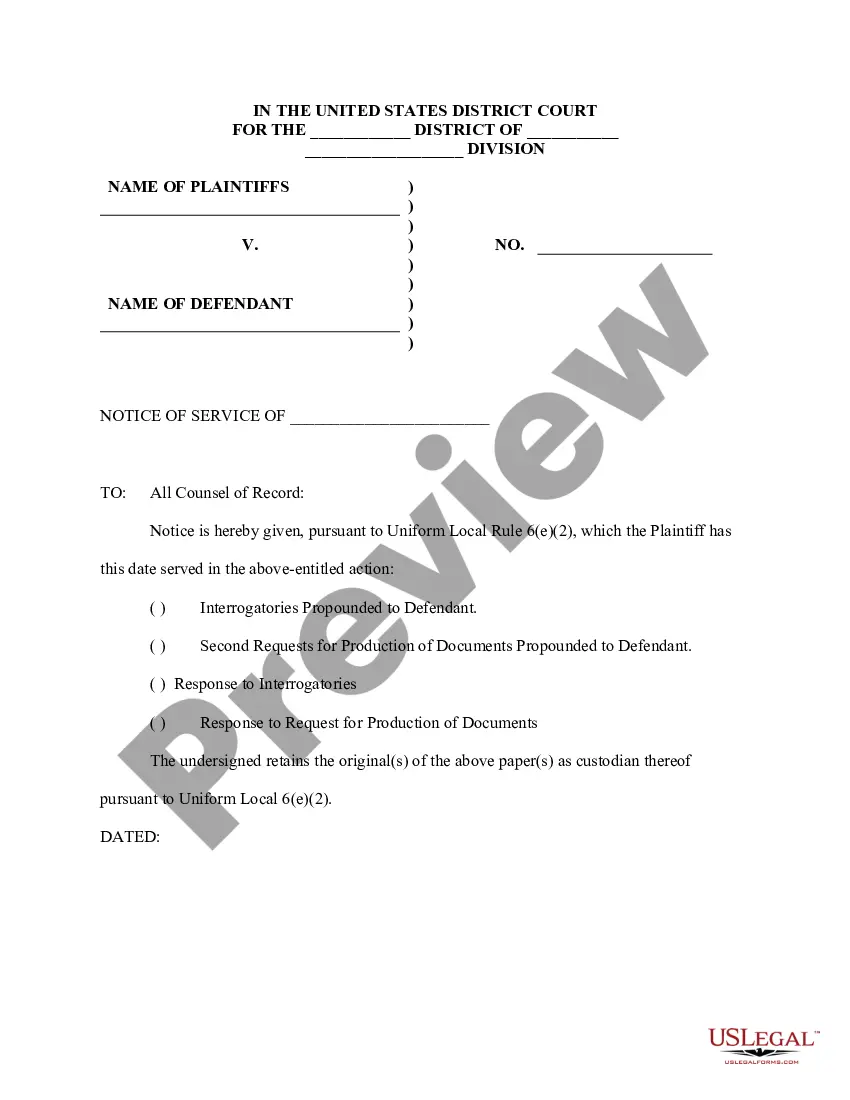
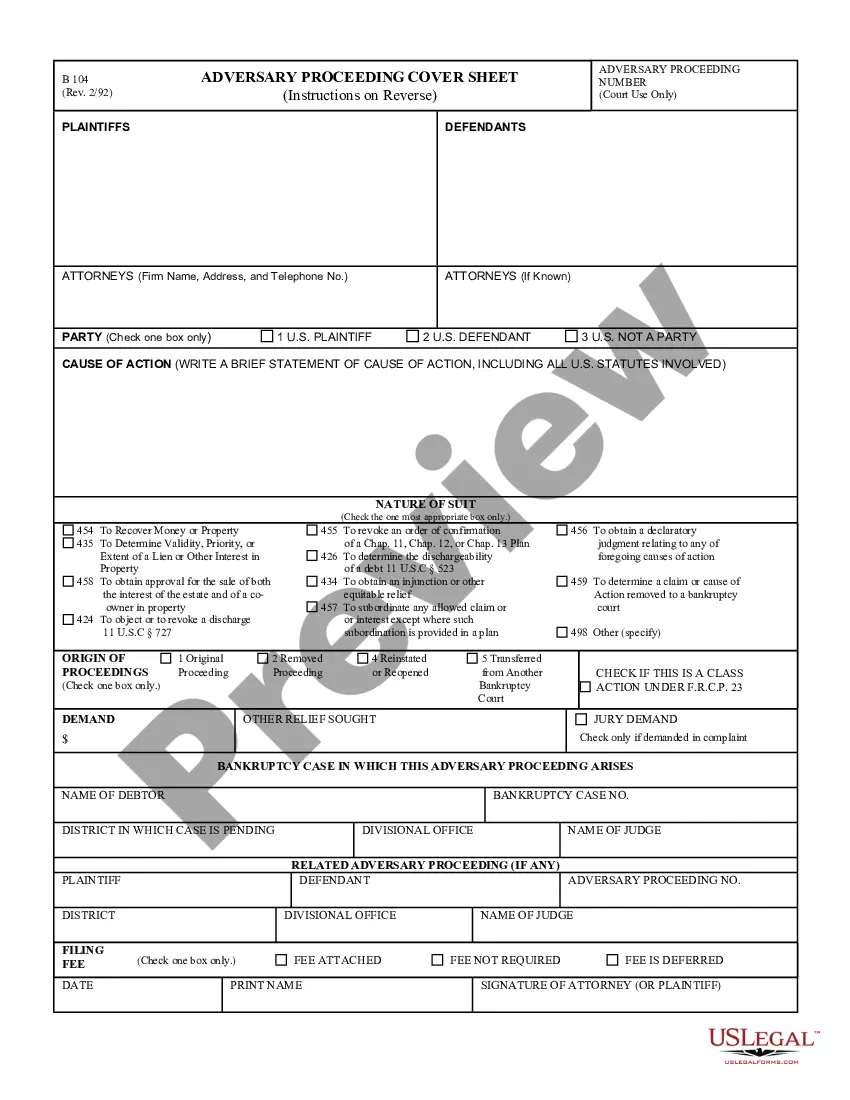
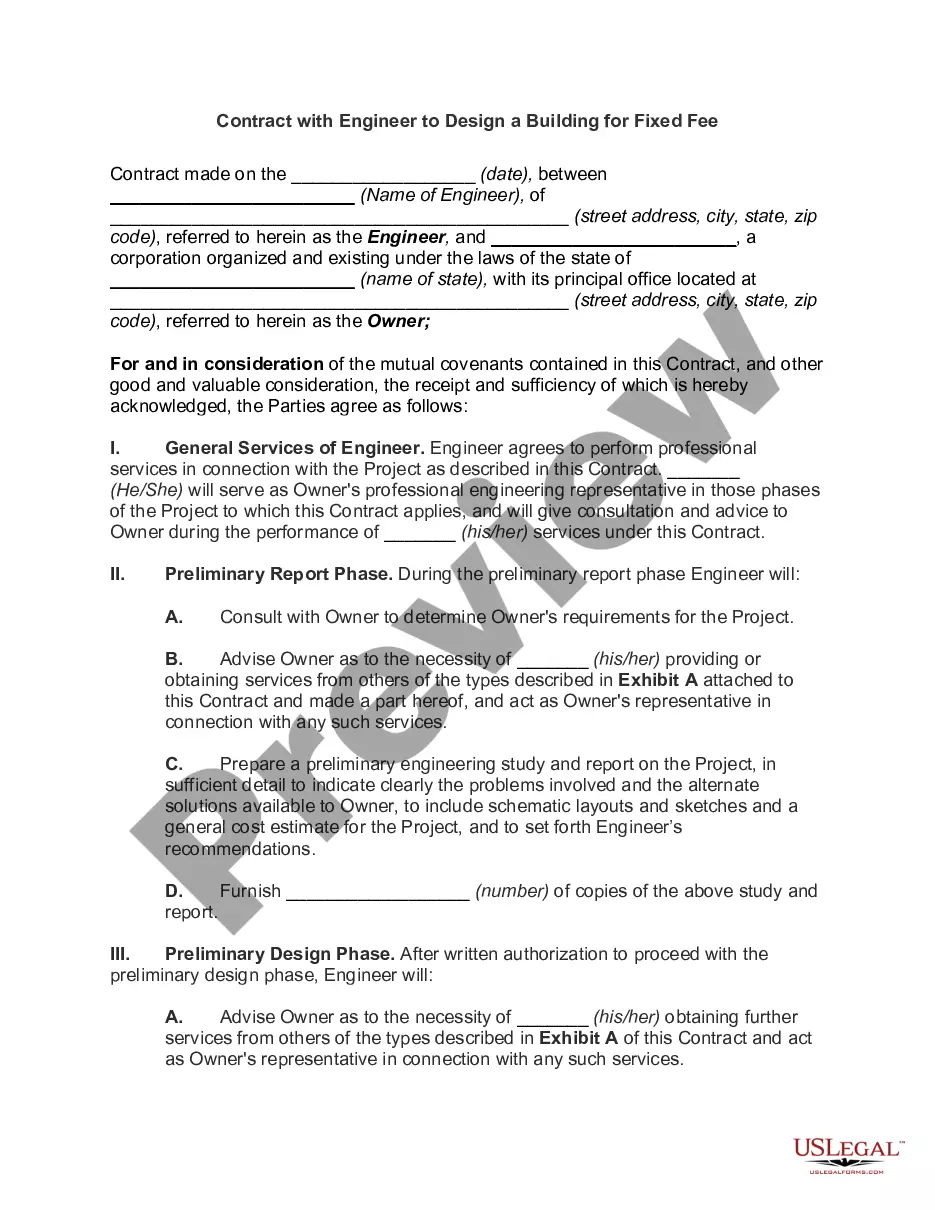
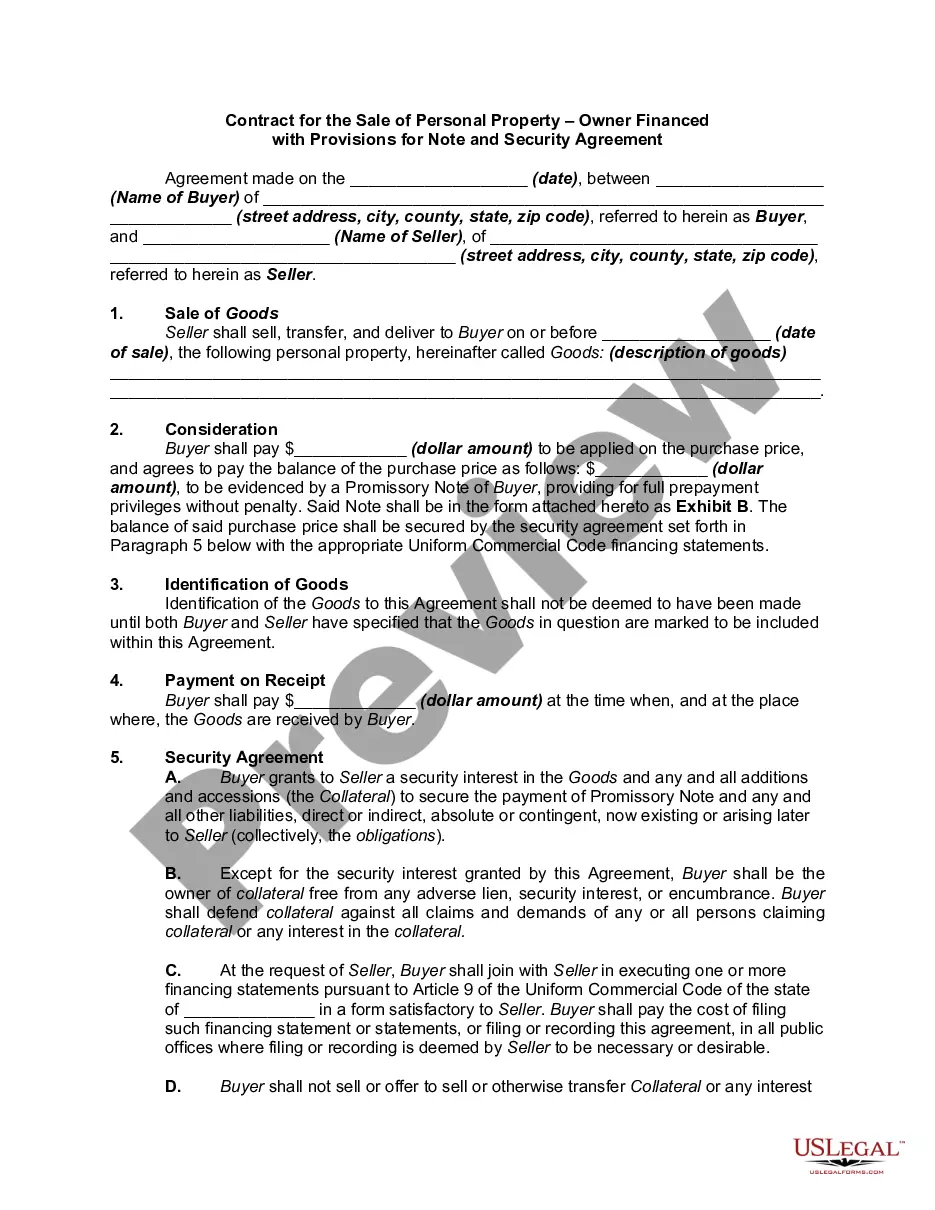
If you need to obtain a Vendor Hipaa Agreement With Oracle sample, follow these simple steps:
- Get the sample you need using the search field or catalog navigation.
- Check out the form’s description to ensure it suits your case, state, and region.
- Click on the form’s preview to see it.
- If it is the wrong document, get back to the search function to find the Vendor Hipaa Agreement With Oracle sample you need.
- Download the file when it matches your requirements.
- If you have a US Legal Forms account, click Log in to access previously saved files in My Forms.
- If you do not have an account yet, you can download the form by clicking Buy now.
- Choose the proper pricing option.
- Finish the account registration form.
- Choose your payment method: use a credit card or PayPal account.
- Choose the file format you want and download the Vendor Hipaa Agreement With Oracle.
- Once it is saved, you can fill out the form by using editing software or print it and finish it manually.
With a substantial US Legal Forms catalog at hand, you don’t need to spend time looking for the right sample across the web. Make use of the library’s straightforward navigation to find the correct form for any situation.
Form popularity
FAQ
How Do I Ensure My Website Meets the Department of Health and Human Services' HIPAA Regulations? Securing the website using an SSL certificate. Encrypting all web forms. Using HIPAA-compliant email encryption. Ensuring that third-party service providers sign a HIPAA business associate agreement (BAA)
Audit Logging: HIPAA compliant databases must log queries and access to PHI to detect potential malicious activity. Encryption: PHI must be encrypted both at-rest and in-transit. This means that data must be stored on encrypted volumes and transmitted over TLS/SSL.
Oracle staff utilizes dedicated systems and environments specifically designed to retain PHI. For example, any data stored on Oracle consulting laptops is encrypted; Oracle Support systems are regularly audited for compliance.
How to get HIPAA Certification Step 1: Select a Security & Privacy Officer within the organization. ... Step 2: Establish privacy policies within the organization. ... Step 3: Establish security procedures to protect PHI. ... Step 4: Establish Business Associate Agreements with vendors. ... Step 5: Train staff as per HIPAA guidelines.
You must continuously monitor for emerging vulnerabilities that could affect a vendor's compliance with HIPAA regulations. All vendor risks should be aggregated into a risk profile drawing data from security questionnaires, risk assessments, and security ratings.