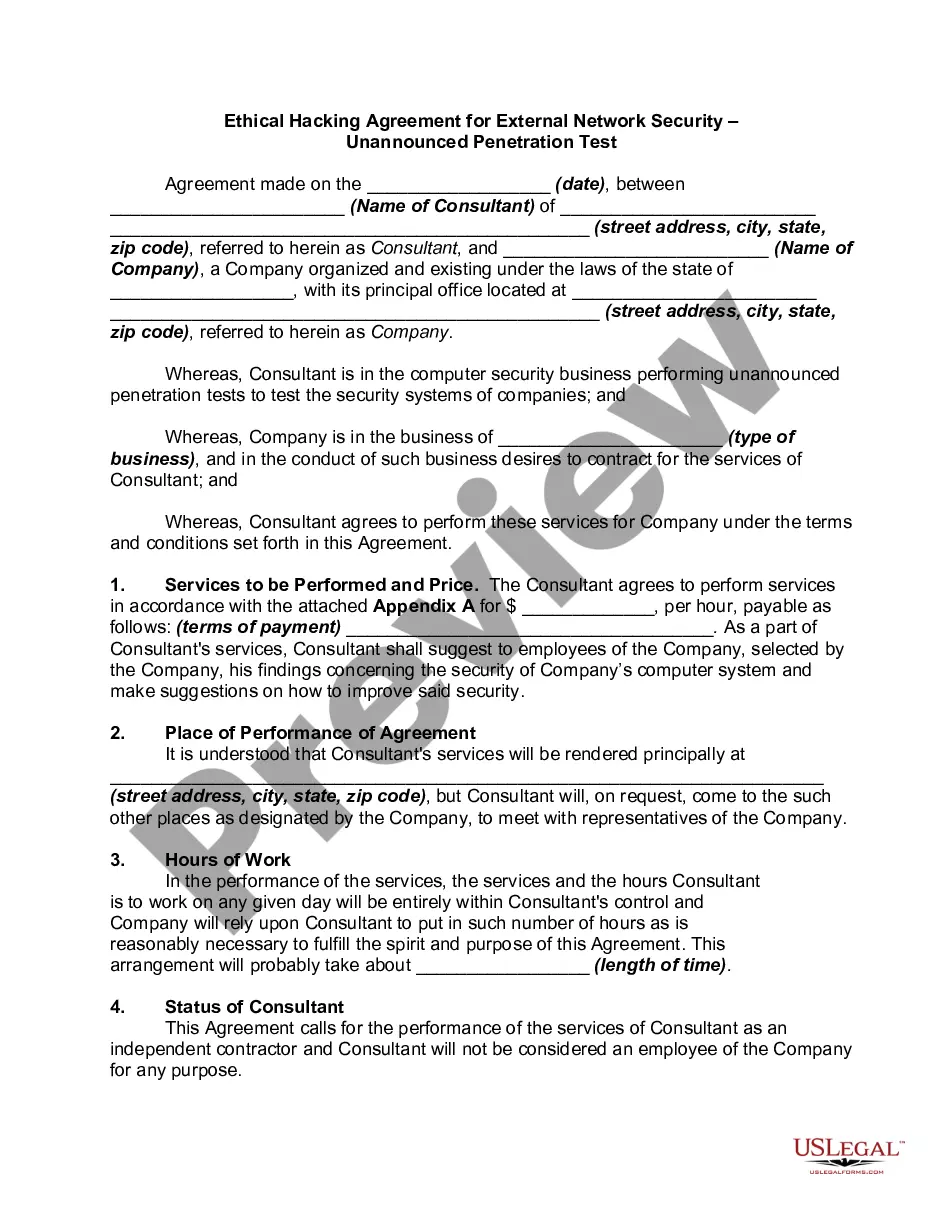
Arizona Ethical Hacking Agreement for External Network Security - Unannounced Penetration Test
Description
Get your form ready online
Our built-in tools help you complete, sign, share, and store your documents in one place.
Make edits, fill in missing information, and update formatting in US Legal Forms—just like you would in MS Word.
Download a copy, print it, send it by email, or mail it via USPS—whatever works best for your next step.
Sign and collect signatures with our SignNow integration. Send to multiple recipients, set reminders, and more. Go Premium to unlock E-Sign.
If this form requires notarization, complete it online through a secure video call—no need to meet a notary in person or wait for an appointment.
We protect your documents and personal data by following strict security and privacy standards.
Make edits, fill in missing information, and update formatting in US Legal Forms—just like you would in MS Word.
Download a copy, print it, send it by email, or mail it via USPS—whatever works best for your next step.
Sign and collect signatures with our SignNow integration. Send to multiple recipients, set reminders, and more. Go Premium to unlock E-Sign.
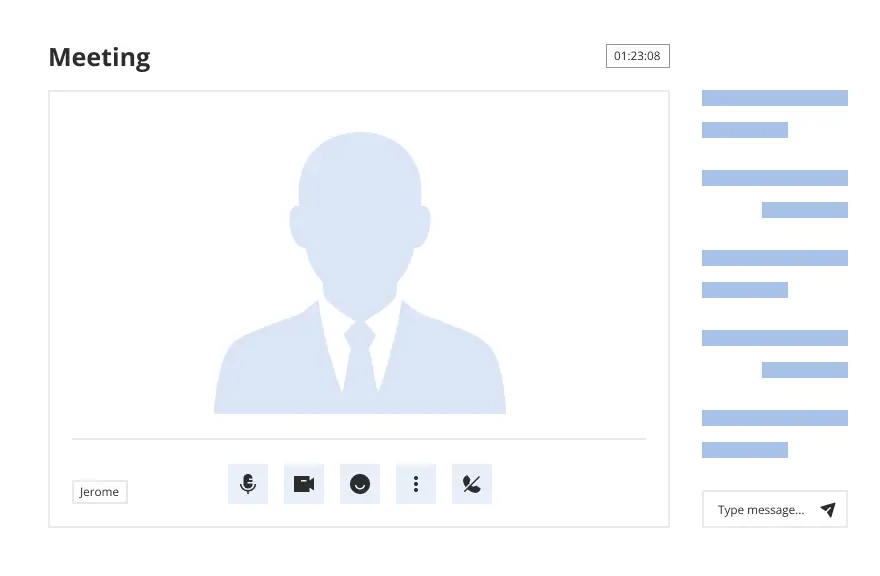
If this form requires notarization, complete it online through a secure video call—no need to meet a notary in person or wait for an appointment.
We protect your documents and personal data by following strict security and privacy standards.
Looking for another form?
How to fill out Ethical Hacking Agreement For External Network Security - Unannounced Penetration Test?
US Legal Forms - one of the largest collections of legal documents in the USA - provides a range of legal document templates that you can download or print.
By utilizing the website, you can access a multitude of forms for business and personal use, categorized by types, states, or keywords.
You can find the latest versions of forms such as the Arizona Ethical Hacking Agreement for External Network Security - Unannounced Penetration Test within seconds.
Examine the form summary to confirm you have selected the correct one.
If the form does not meet your needs, use the Search field at the top of the screen to find the one that does.
- If you already have an account, Log In and retrieve the Arizona Ethical Hacking Agreement for External Network Security - Unannounced Penetration Test from the US Legal Forms library.
- The Download button will appear on each form you view.
- You also have access to all previously downloaded forms under the My documents section of your account.
- If you are using US Legal Forms for the first time, here are some basic instructions to help you get started.
- Ensure you have selected the correct form for your area/county.
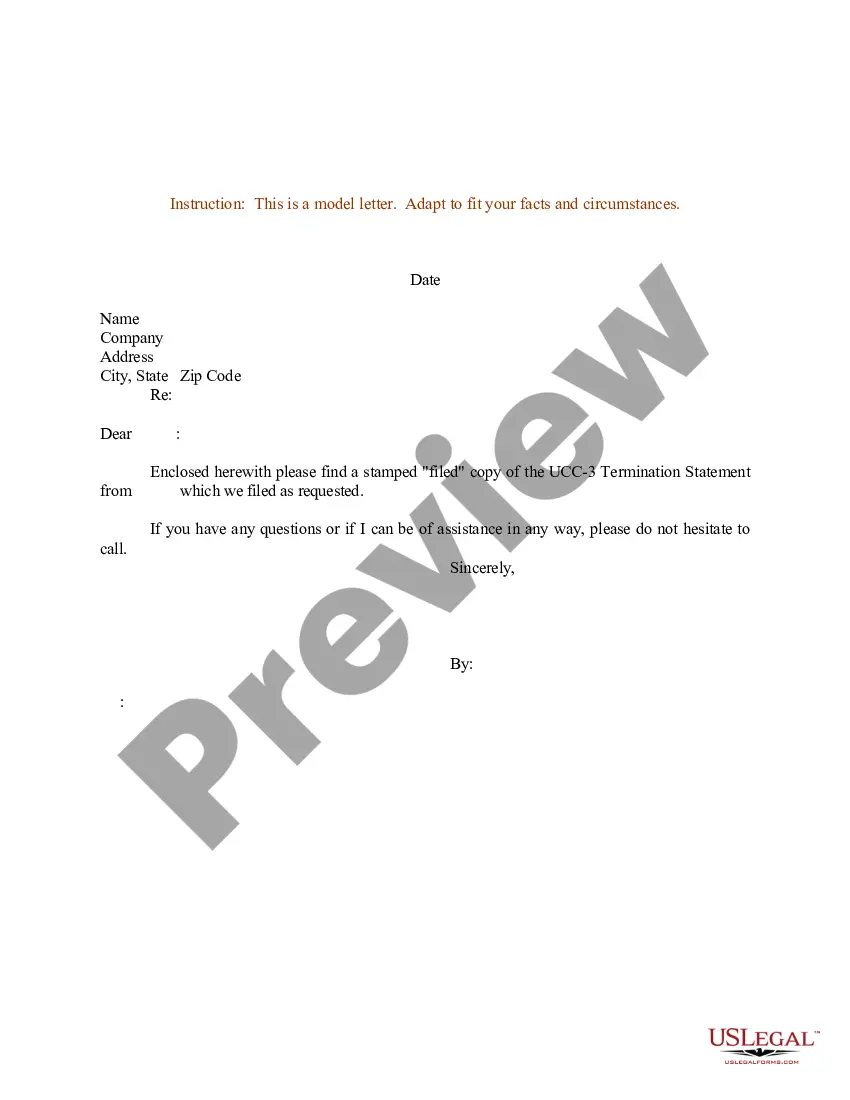
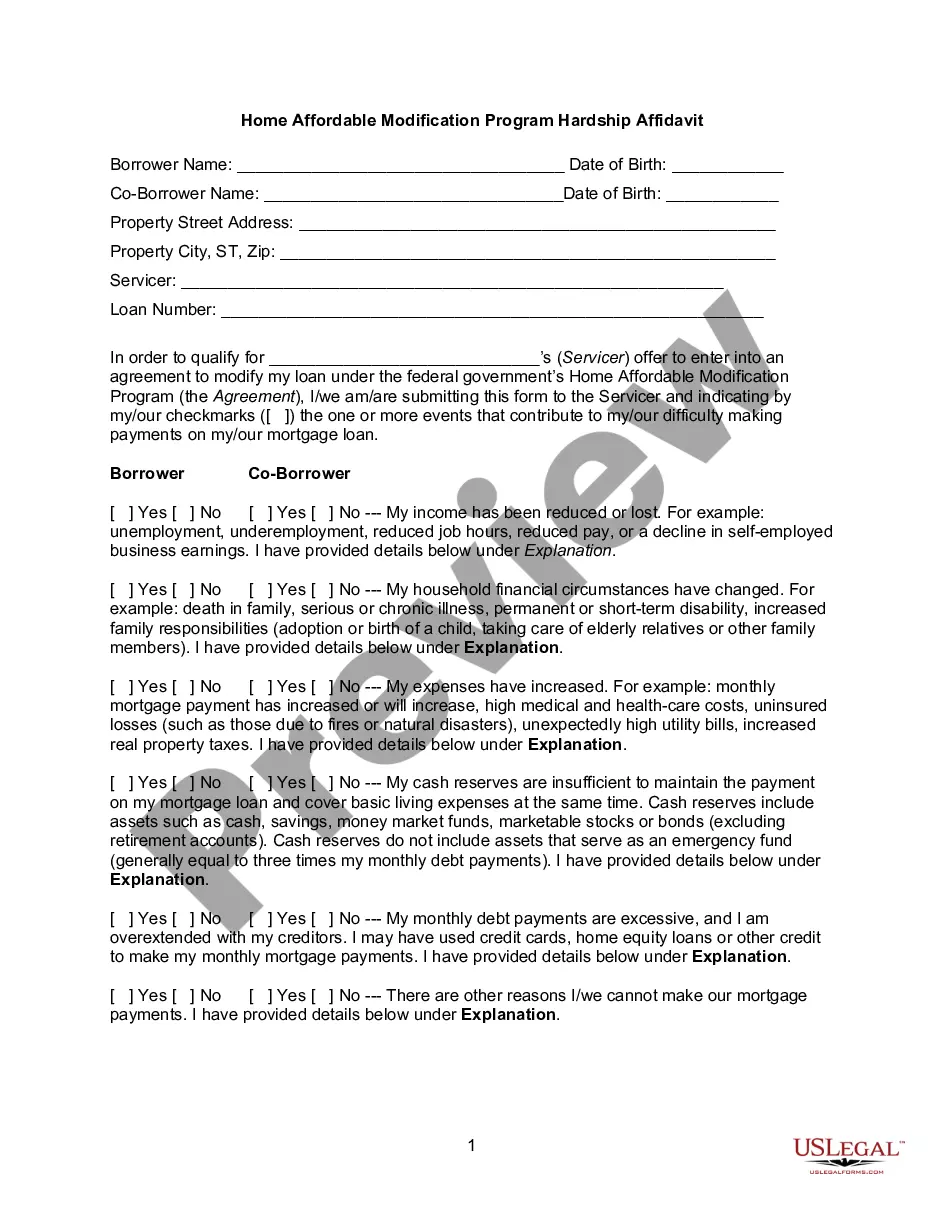
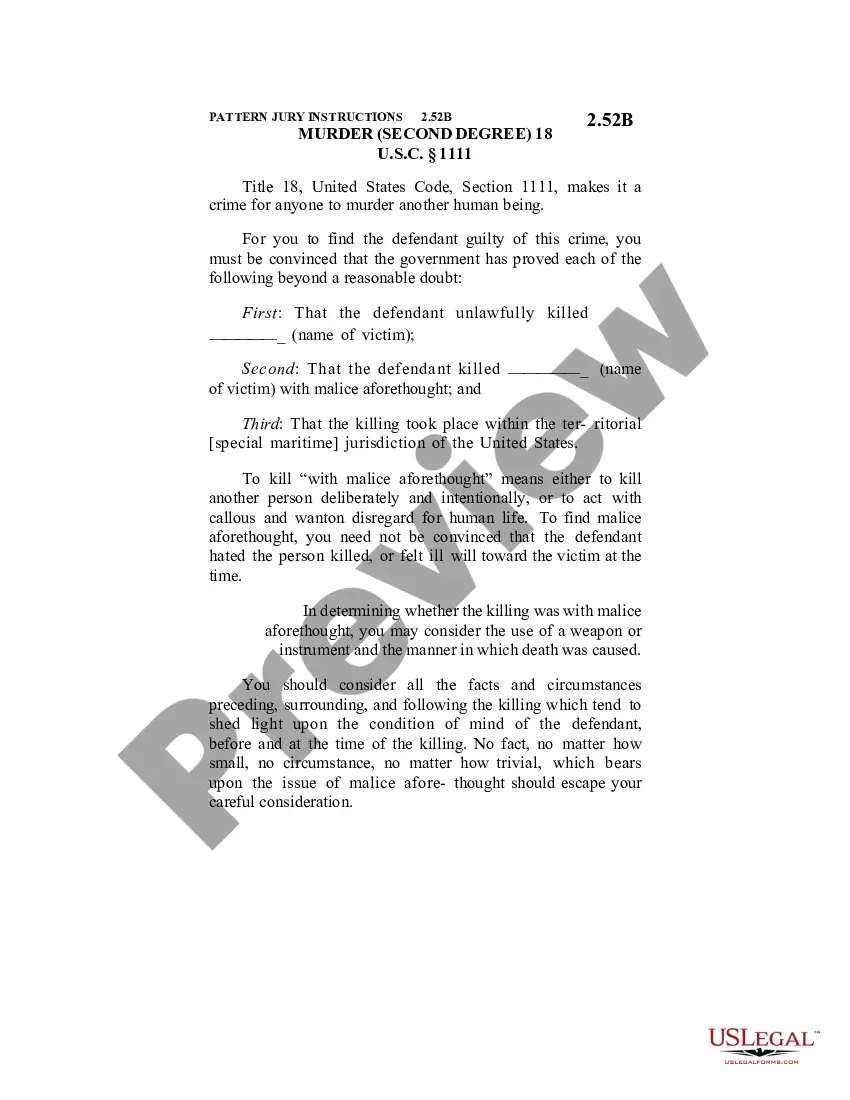
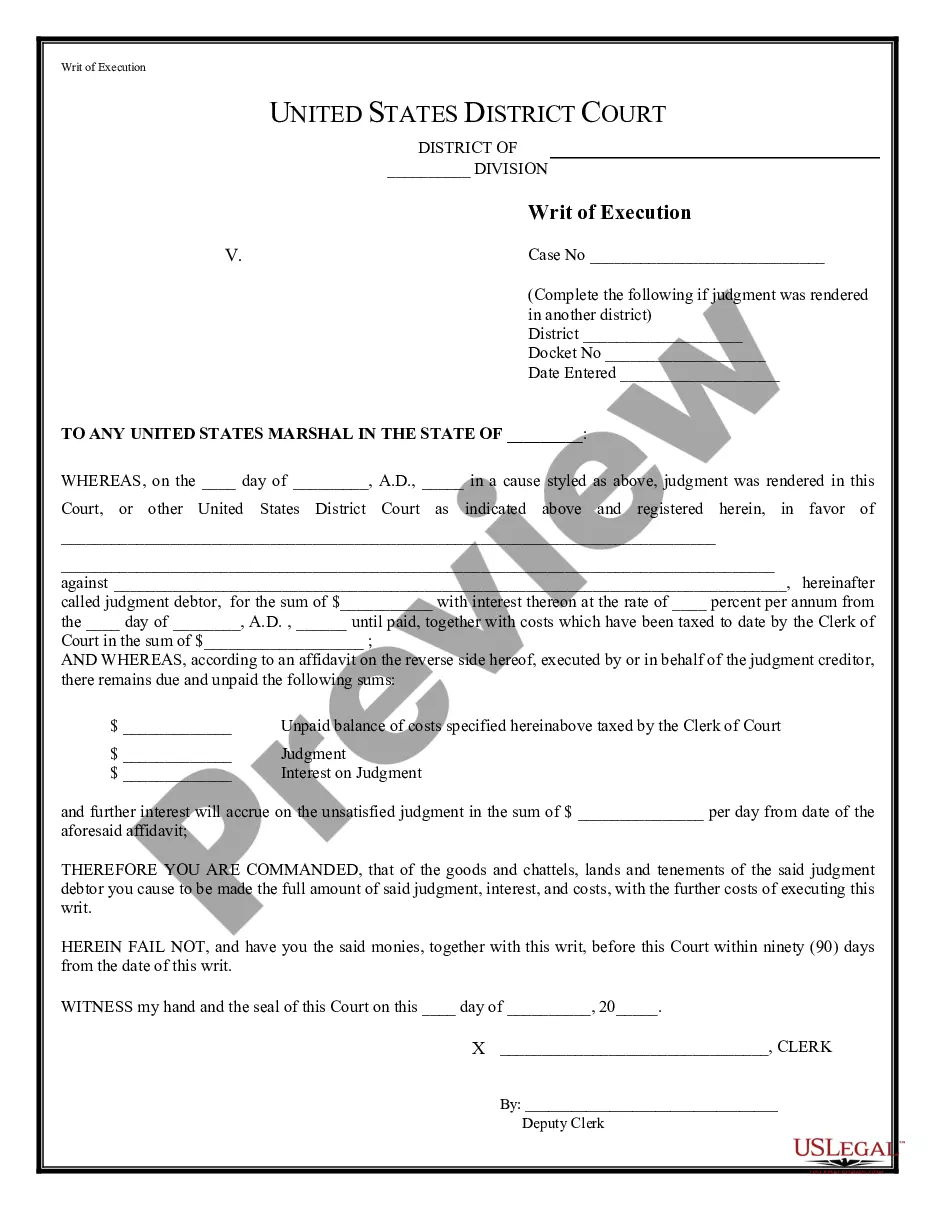
- Review the Preview option to check the form's details.
Form popularity
FAQ
An ethical hacker can commence testing after securing explicit permission from the organization. It is critical to establish an Arizona Ethical Hacking Agreement for External Network Security - Unannounced Penetration Test, outlining the scope, objectives, and timeline for the testing. Preparing an agreement beforehand helps ensure clarity and sets the right expectations for all parties involved.
The best certification for ethical hacking often depends on your current experience and future aspirations. Popular choices include CEH, OSCP, and CompTIA PenTest+. Each certification offers a unique perspective and expertise useful for conducting an Arizona Ethical Hacking Agreement for External Network Security - Unannounced Penetration Test. Evaluate your skills and choose the certification that aligns best with your career map.
Yes, ethical hacking testing is legal provided it's conducted with proper authorization. Engaging in an Arizona Ethical Hacking Agreement for External Network Security - Unannounced Penetration Test requires written consent from the network or system owners. Adhering to legal standards is crucial to ensure that ethical hacking efforts yield beneficial results without crossing any legal boundaries.
Choosing between the Offensive Security Certified Professional (OSCP) and the Certified Ethical Hacker (CEH) often depends on your career goals. The OSCP focuses more on hands-on experience, while the CEH offers a broad overview of ethical hacking concepts. If you aim to perform an Arizona Ethical Hacking Agreement for External Network Security - Unannounced Penetration Test, the certification you choose should align with your skill level and desired expertise.
Yes, the Certified Ethical Hacker (CEH) certification remains valuable in today’s cybersecurity landscape. It provides essential knowledge and skills needed to mitigate risks and respond to security breaches effectively. For those considering an Arizona Ethical Hacking Agreement for External Network Security - Unannounced Penetration Test, obtaining a CEH credential can enhance your credibility and marketability in the field.
To become an ethical hacker specializing in the Arizona Ethical Hacking Agreement for External Network Security - Unannounced Penetration Test, you need a blend of skills and certifications. Typically, a strong foundation in networking, system administration, and security principles is crucial. Additionally, obtaining certifications like Certified Ethical Hacker (CEH) can significantly enhance your credibility. It's also important to understand the legal implications of hacking to ensure that your activities align with the law.
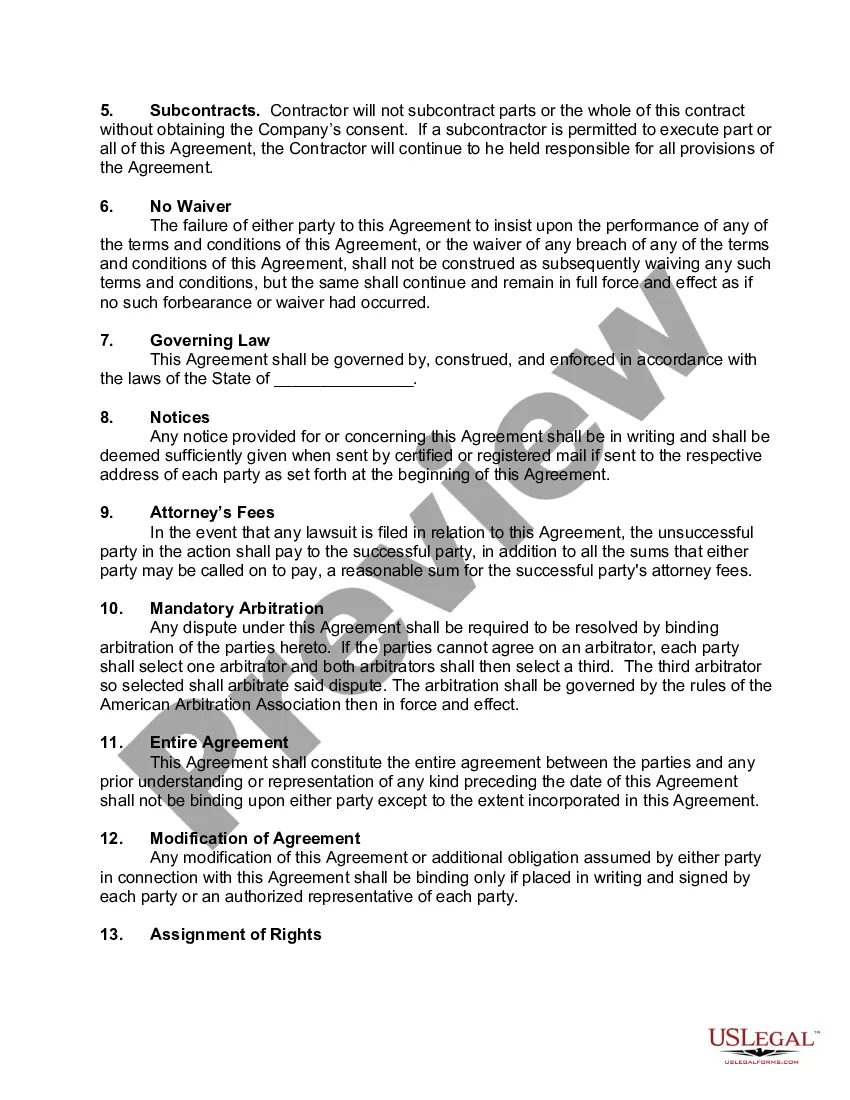
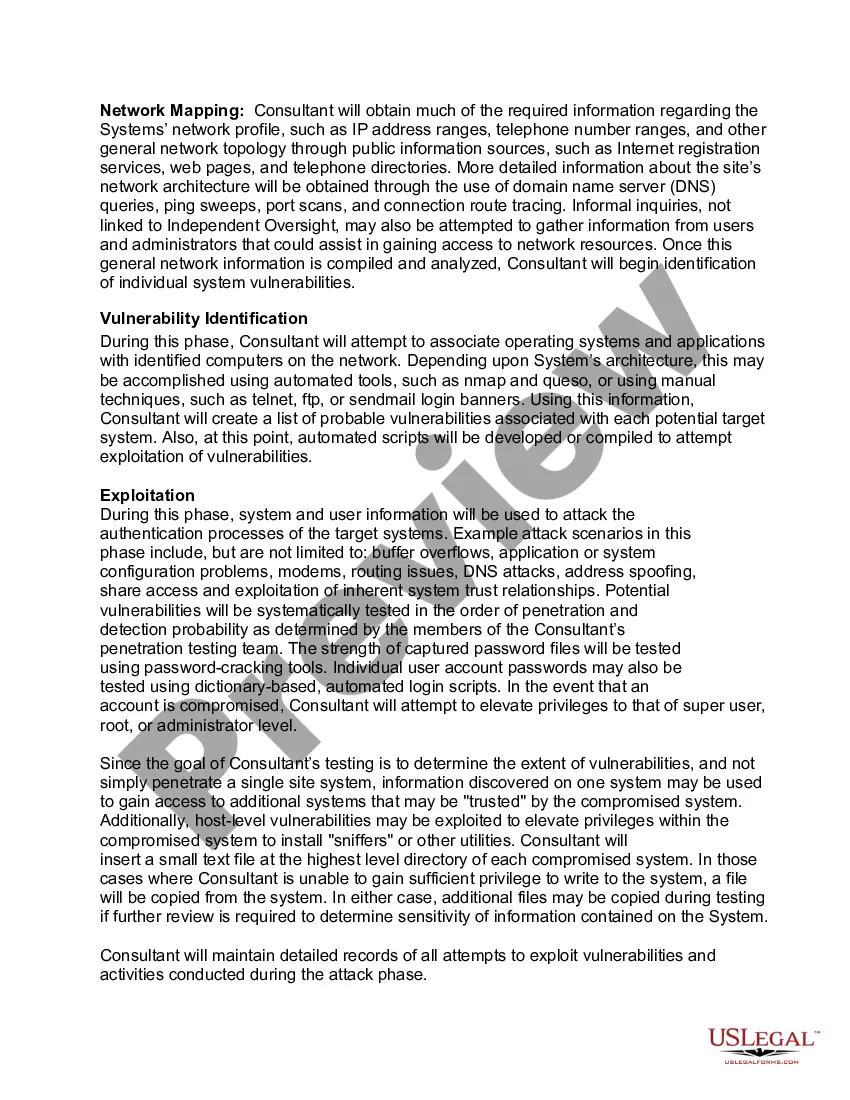
When conducting an unannounced penetration test under the Arizona Ethical Hacking Agreement for External Network Security, ethical and legal considerations are vital. It's essential to have proper authorization from the organization you're testing. This agreement outlines the scope, ensuring that hackers do not access unauthorized areas, thus protecting both parties. Transparency and adherence to legal frameworks help prevent potential liability issues.
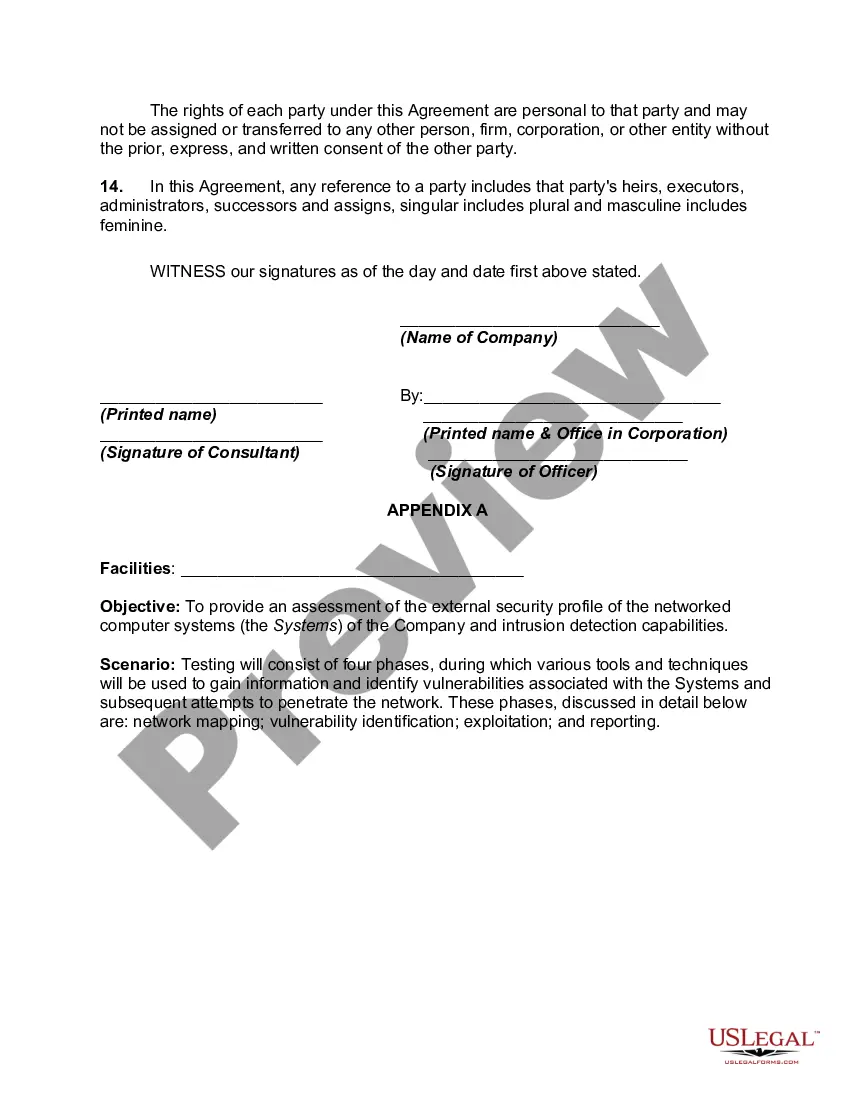
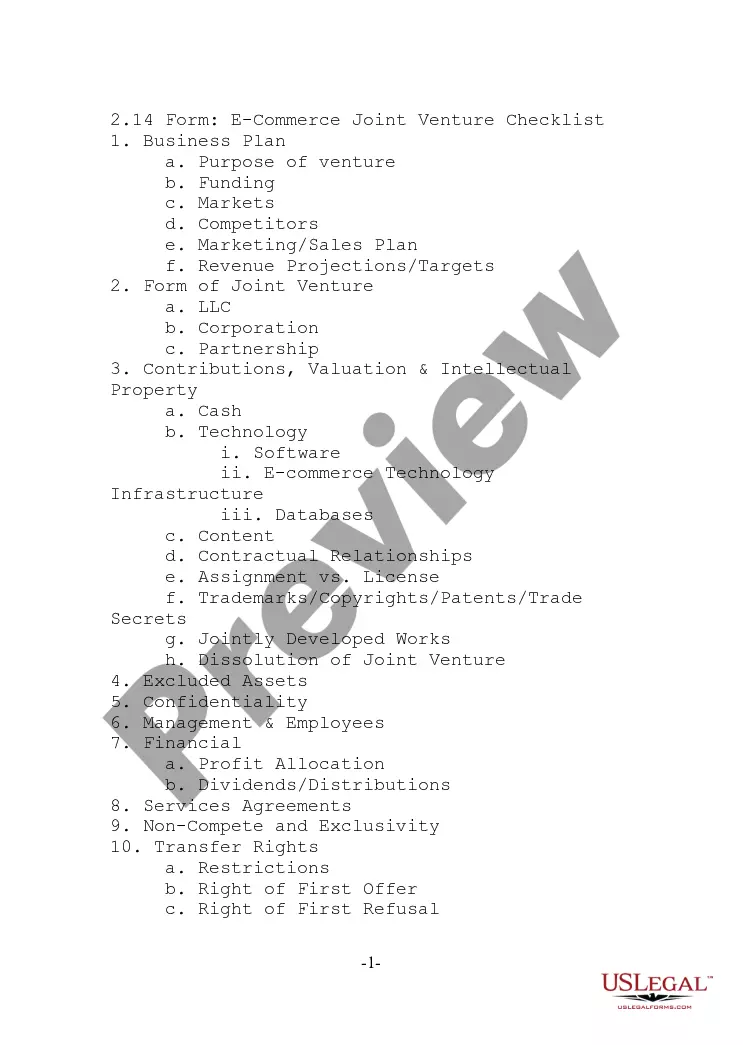
A test agreement is a contract that outlines the responsibilities and expectations of both the ethical hacker and the client undergoing testing. Specifically, in the context of an Arizona Ethical Hacking Agreement for External Network Security - Unannounced Penetration Test, it serves as a binding document that clarifies the scope, objectives, and legal implications of the engagement. This agreement is vital for maintaining a professional and accountable testing process.
A test contract should include key documents such as the signed agreement, a Statement of Work, and any necessary non-disclosure agreements. Incorporating these elements into your Arizona Ethical Hacking Agreement for External Network Security - Unannounced Penetration Test will create a comprehensive legal framework for the testing process. This ensures clear communication and mitigates the risk of misunderstandings.
A testing agreement often includes an introduction section outlining the purpose, a scope section detailing the extent of the testing to be performed, and a limitations section specifying any restrictions. In the context of an Arizona Ethical Hacking Agreement for External Network Security - Unannounced Penetration Test, these sections enable clarity and ensure that the testing is conducted within agreed-upon boundaries. Having a solid agreement safeguards both the tester and the organization.