Alabama Ethical Hacking Agreement for External Network Security - Unannounced Penetration Test
Description
Get your form ready online
Our built-in tools help you complete, sign, share, and store your documents in one place.
Make edits, fill in missing information, and update formatting in US Legal Forms—just like you would in MS Word.
Download a copy, print it, send it by email, or mail it via USPS—whatever works best for your next step.
Sign and collect signatures with our SignNow integration. Send to multiple recipients, set reminders, and more. Go Premium to unlock E-Sign.
If this form requires notarization, complete it online through a secure video call—no need to meet a notary in person or wait for an appointment.
We protect your documents and personal data by following strict security and privacy standards.
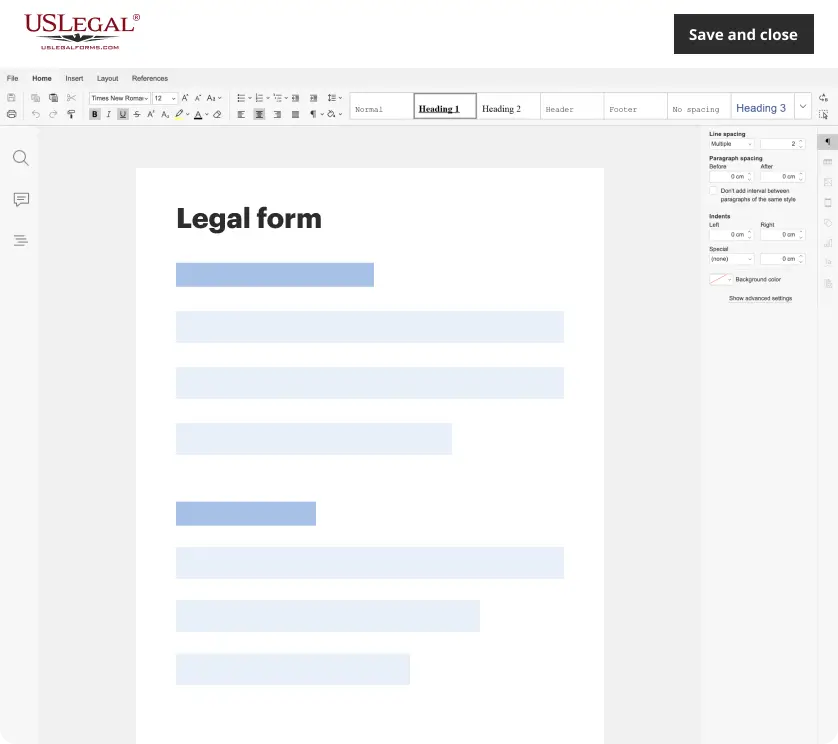
Make edits, fill in missing information, and update formatting in US Legal Forms—just like you would in MS Word.
Download a copy, print it, send it by email, or mail it via USPS—whatever works best for your next step.
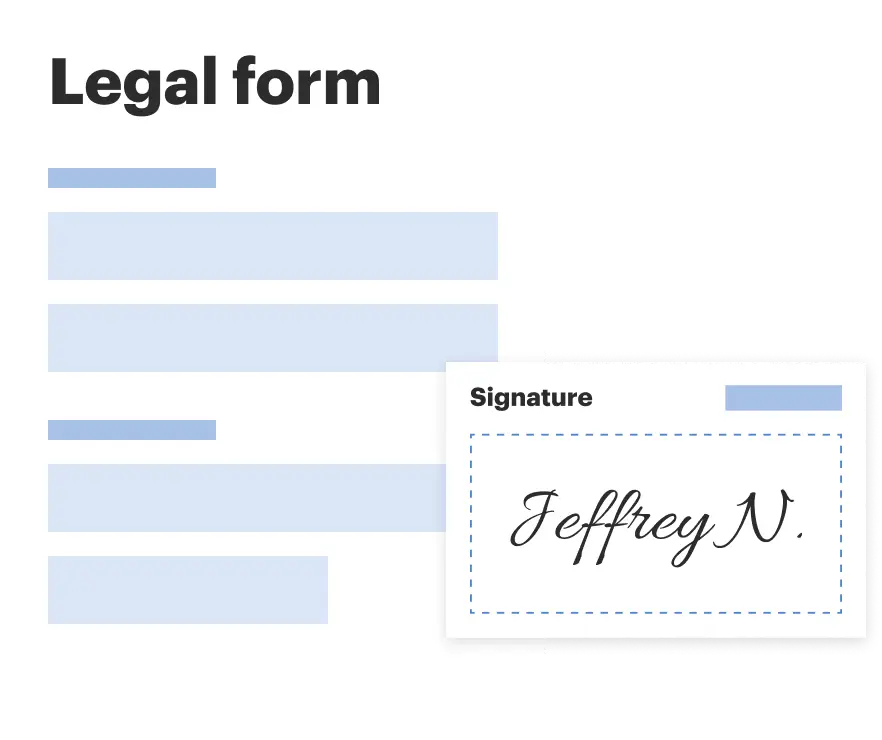
Sign and collect signatures with our SignNow integration. Send to multiple recipients, set reminders, and more. Go Premium to unlock E-Sign.
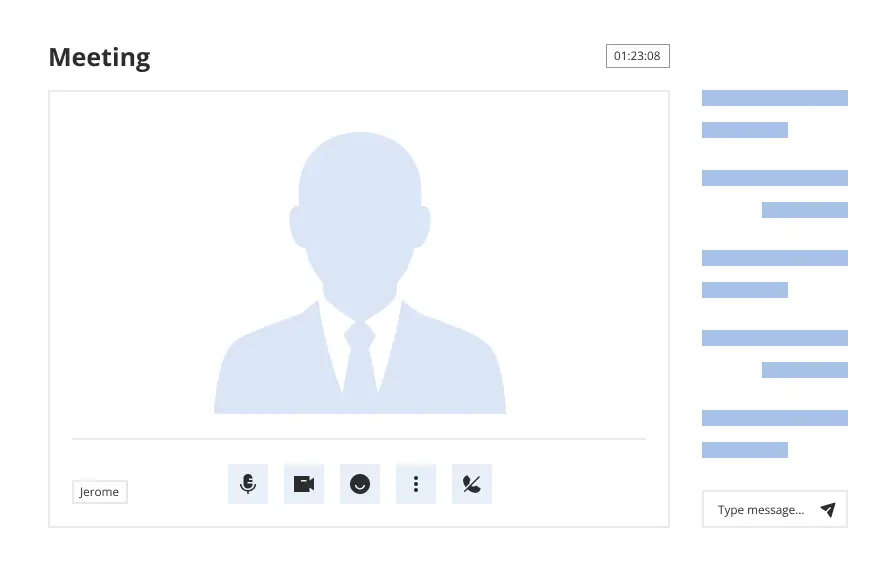
If this form requires notarization, complete it online through a secure video call—no need to meet a notary in person or wait for an appointment.
We protect your documents and personal data by following strict security and privacy standards.
Looking for another form?
How to fill out Ethical Hacking Agreement For External Network Security - Unannounced Penetration Test?
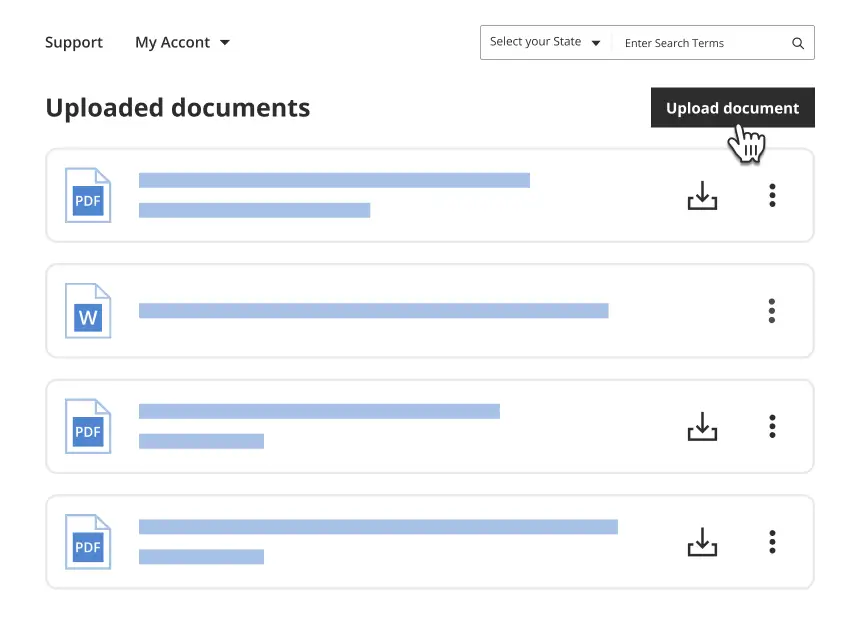
If you desire to thoroughly, download, or print legal document templates, utilize US Legal Forms, the largest collection of legal forms available online.
Take advantage of the site's user-friendly search functionality to find the documents you need.
Various templates for business and individual purposes are sorted by categories and states, or keywords.
Step 4. Once you have found the form you need, click the Buy now button. Select the payment plan you prefer and enter your information to register for the account.
Step 5. Process the transaction. You may use your credit card or PayPal account to complete the payment.
- Utilize US Legal Forms to acquire the Alabama Ethical Hacking Agreement for External Network Security - Unannounced Penetration Test in just a few clicks.
- If you are currently a US Legal Forms user, sign in to your account and click on the Download button to retrieve the Alabama Ethical Hacking Agreement for External Network Security - Unannounced Penetration Test.
- You can also access forms you previously downloaded in the My documents section of your account.
- If you are using US Legal Forms for the first time, follow the instructions below.
- Step 1. Ensure you have selected the correct form for your city/state.
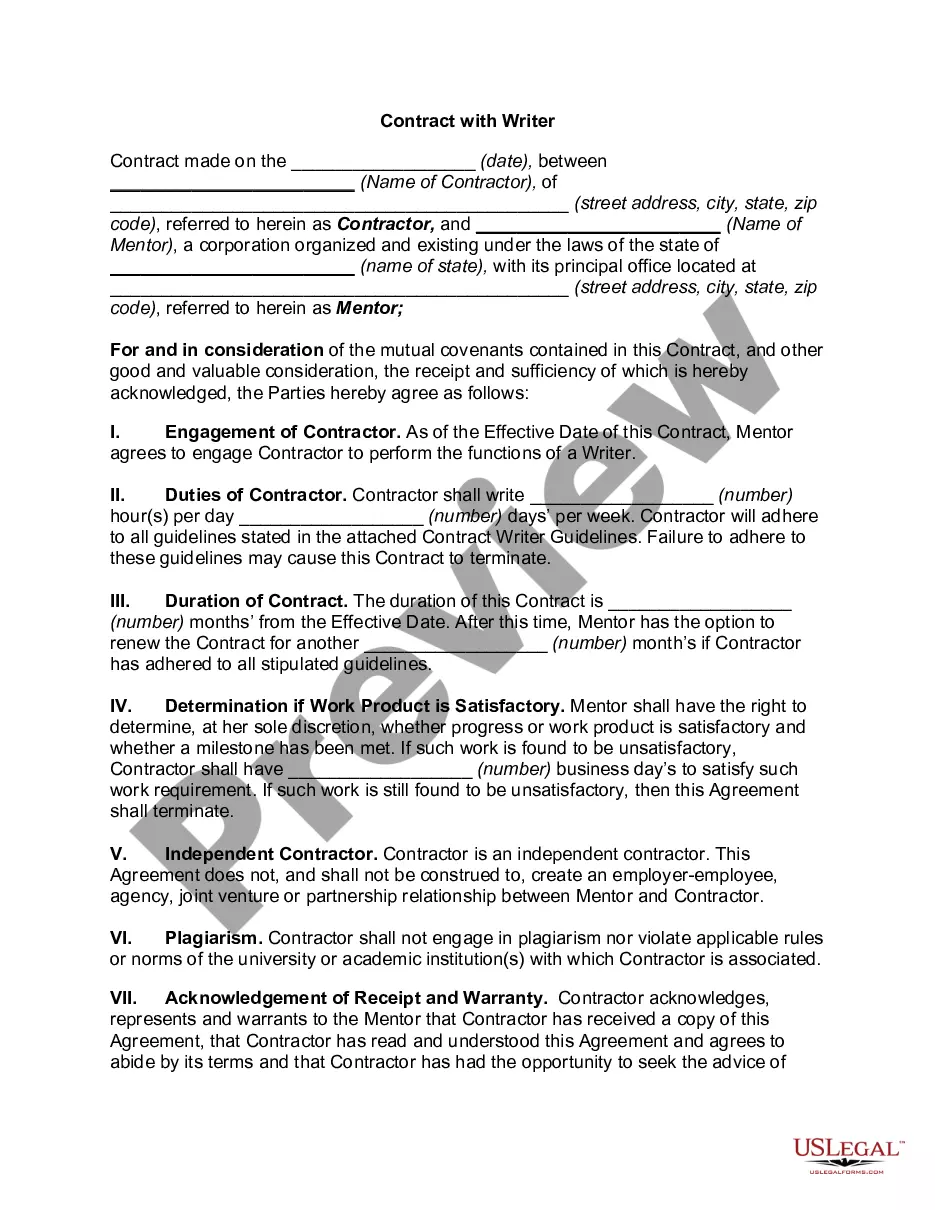
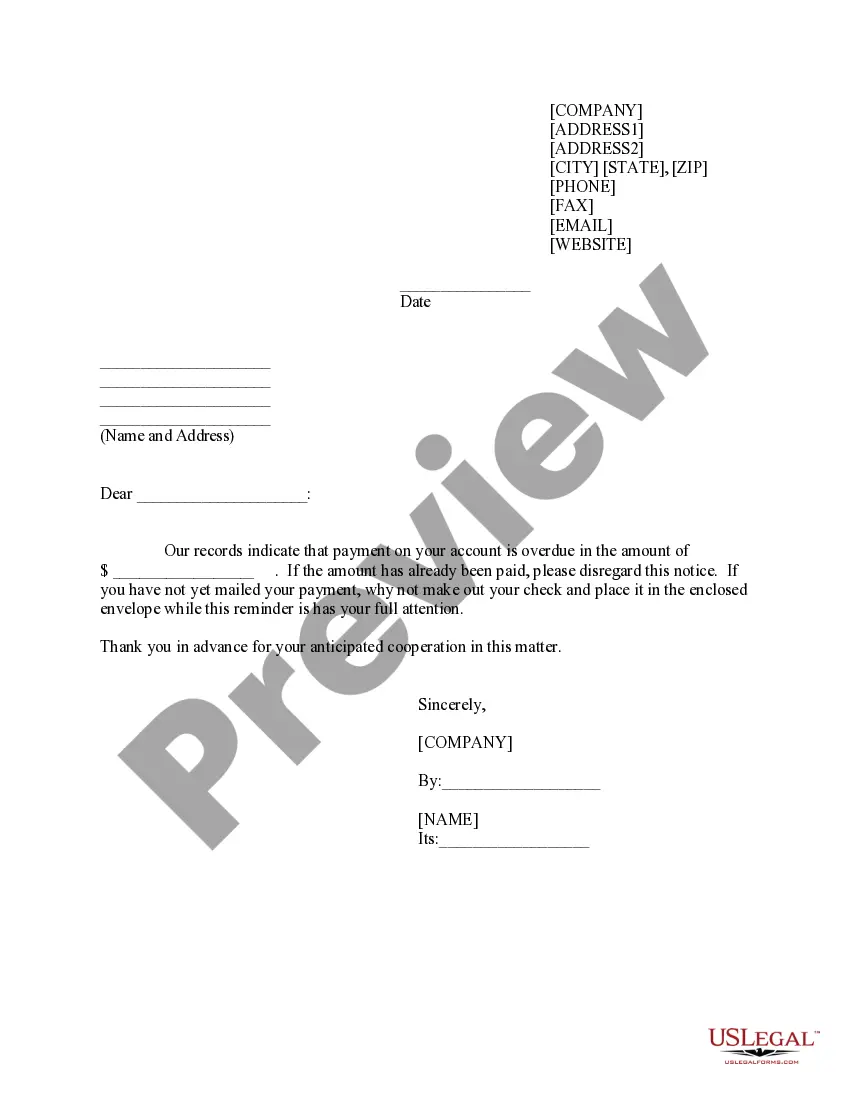
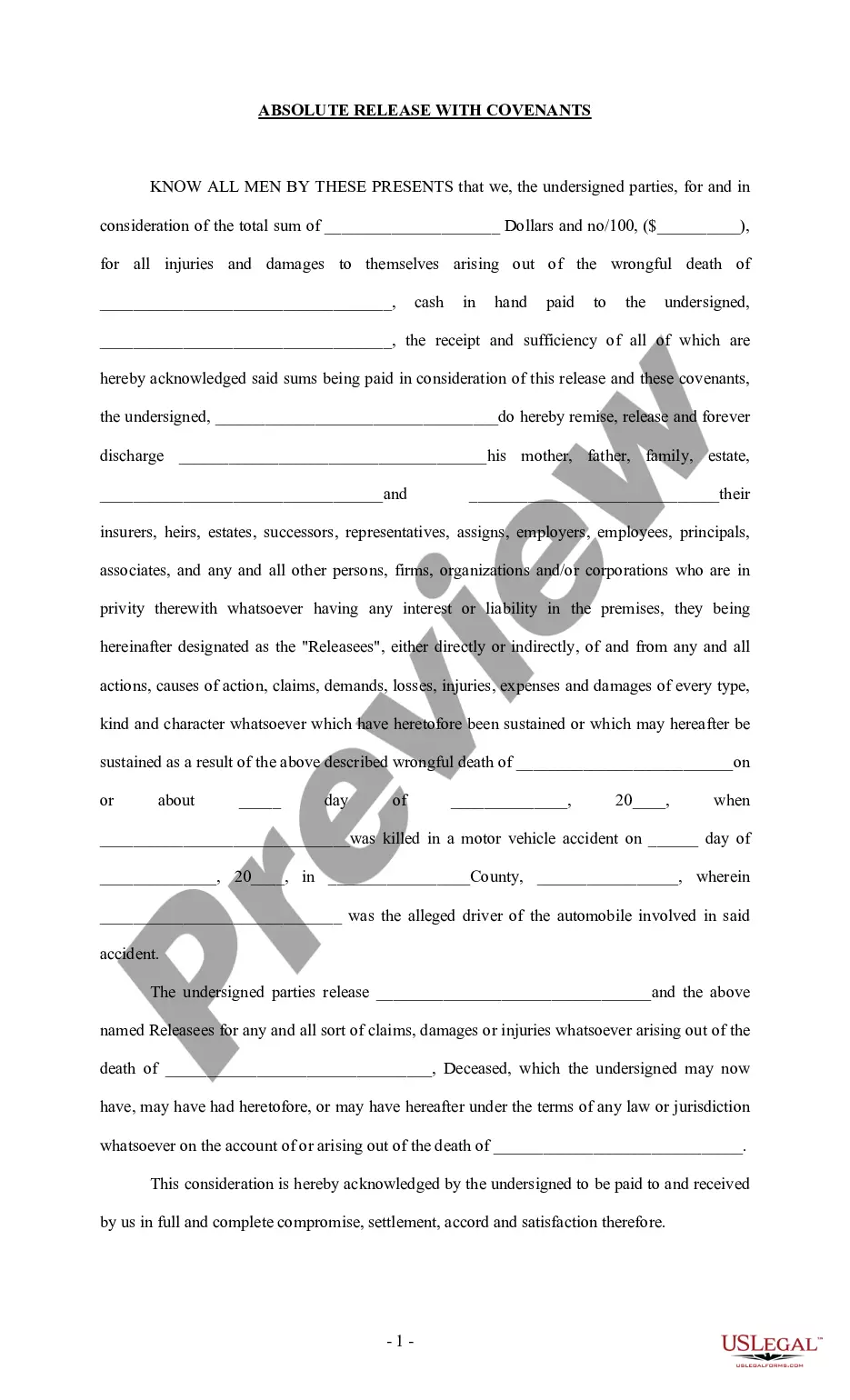
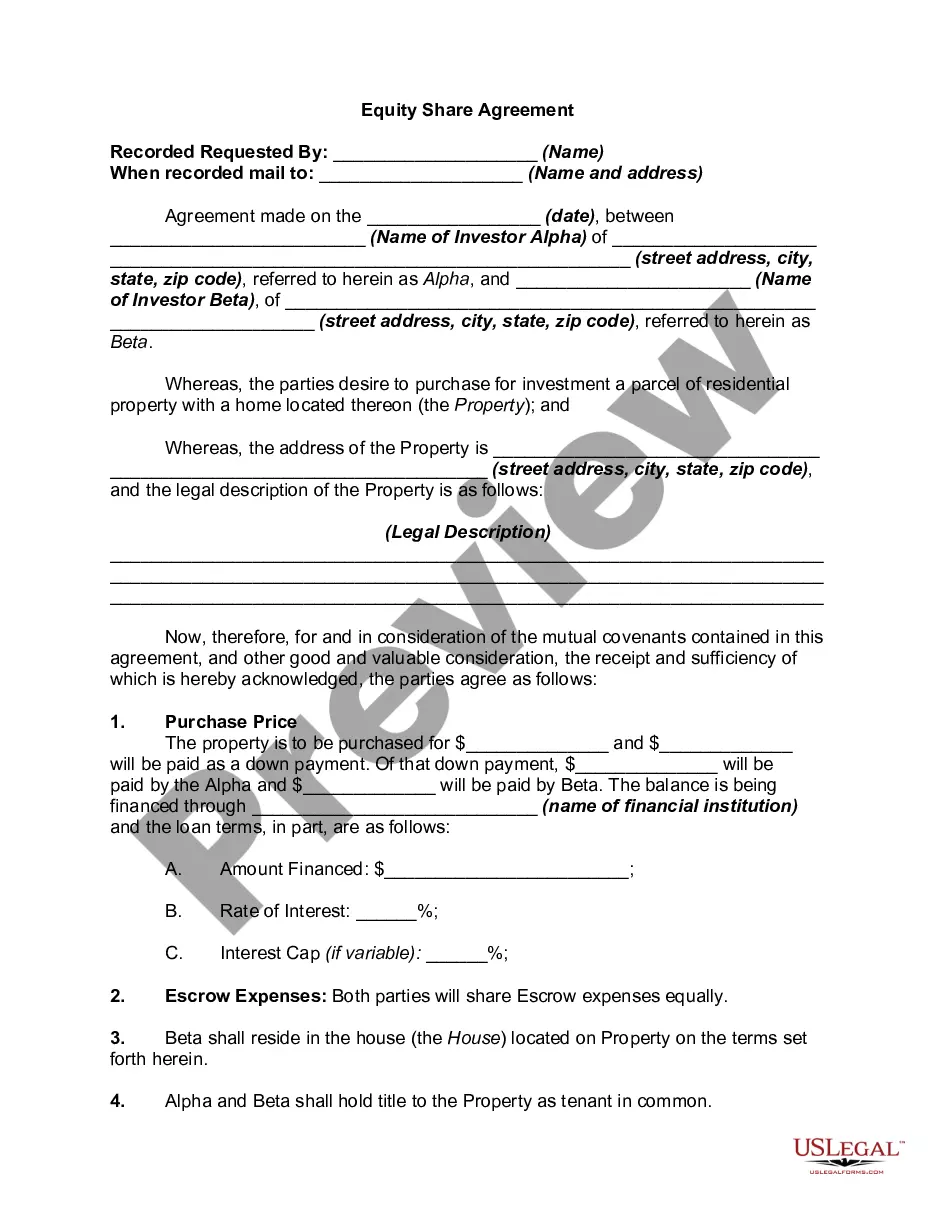
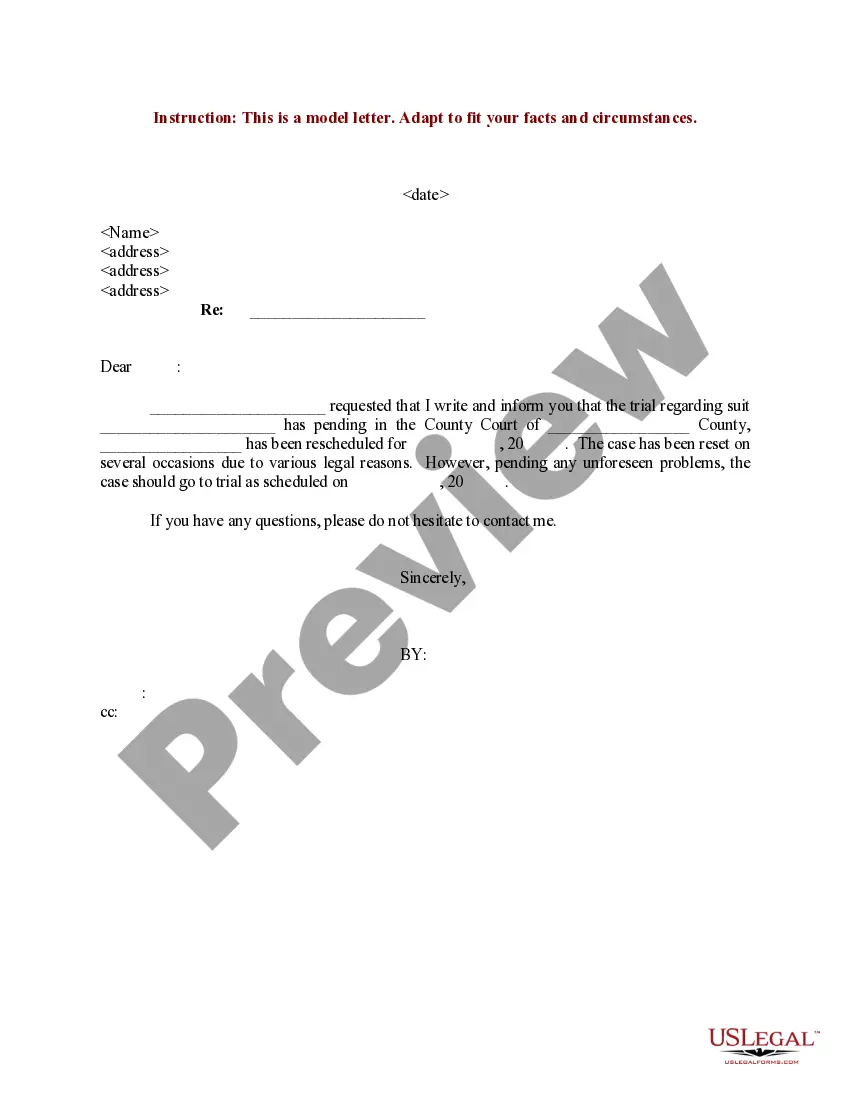
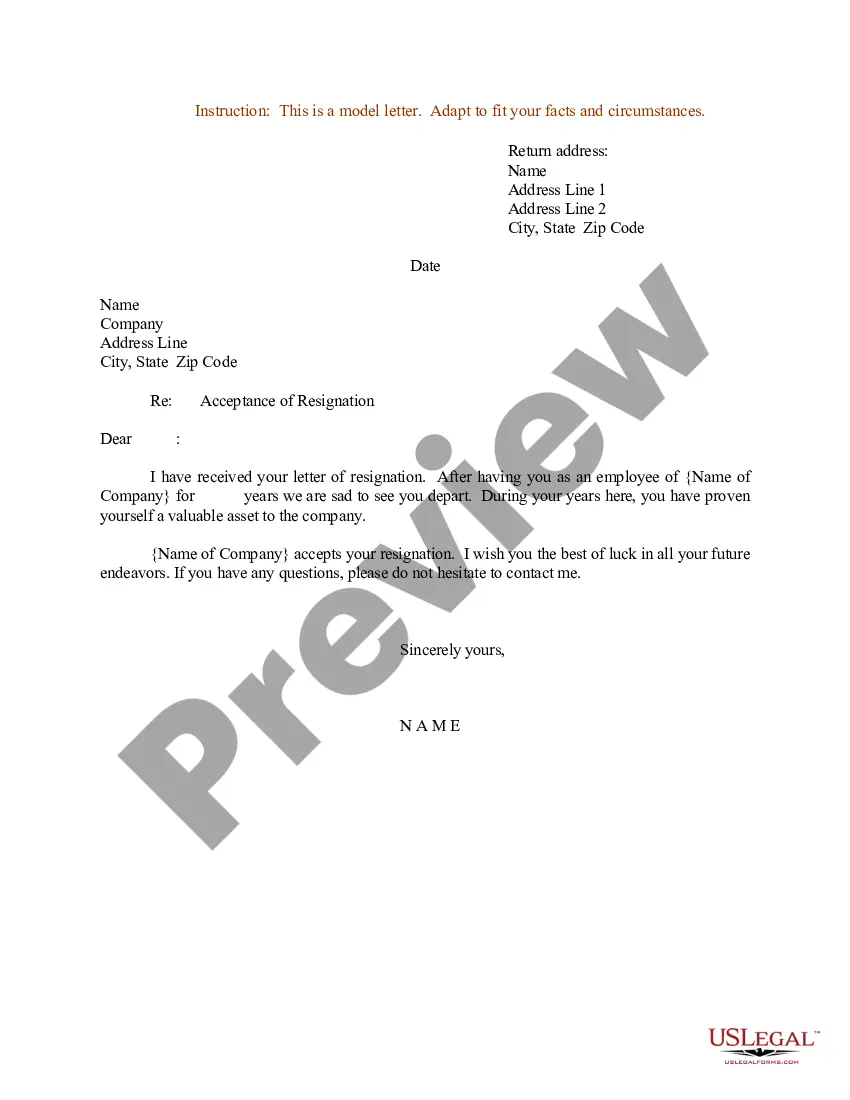
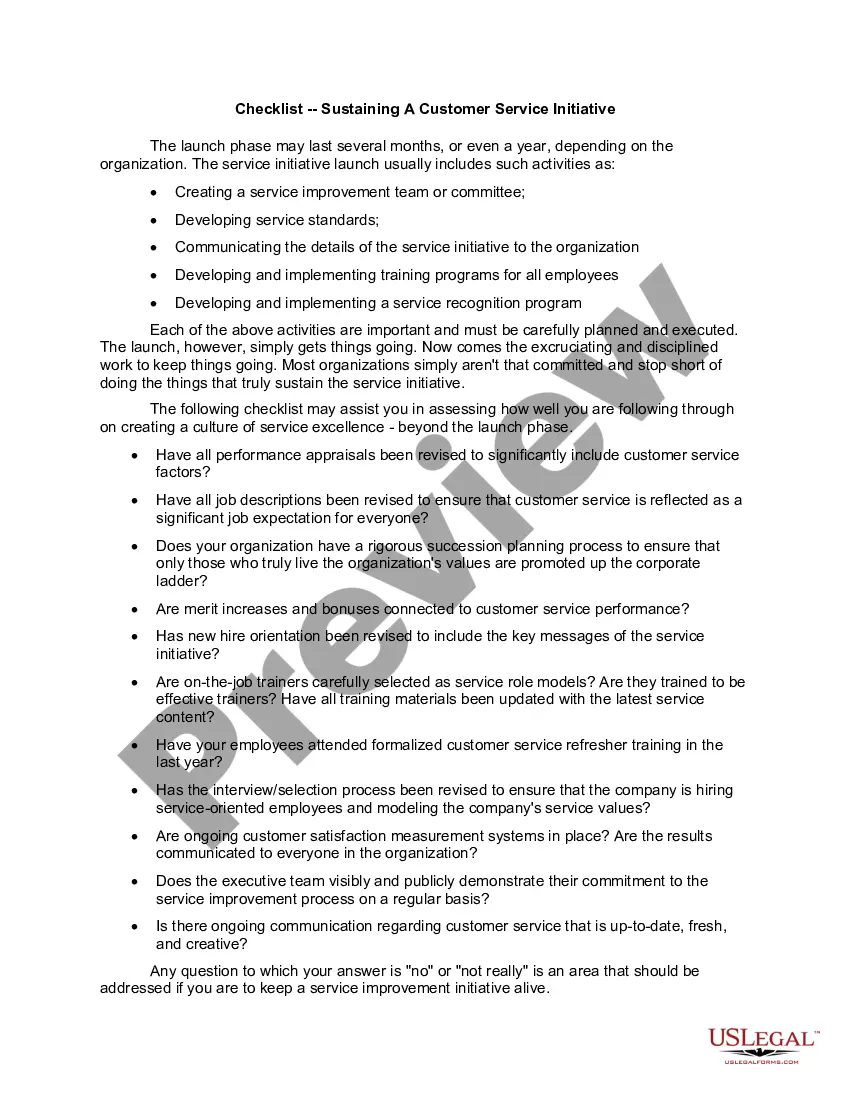
- Step 2. Utilize the Preview option to review the content of the form. Be sure to read the description.
- Step 3. If you are not satisfied with the template, use the Search area at the top of the screen to find alternative versions of the legal form format.
Form popularity
FAQ
The fees for an ethical hacking course can vary based on several factors, including the institution, the course format, and the depth of training. Typically, fees range from a few hundred to several thousand dollars. It's essential to choose a course that aligns with your goals, especially if you are looking to master the Alabama Ethical Hacking Agreement for External Network Security - Unannounced Penetration Test. By investing in quality training, you will gain the skills necessary for effective penetration testing and enhance your career prospects in cybersecurity.
Testing networks and systems without permission is illegal and can lead to severe consequences. Ethical hackers must always seek authorization before conducting tests to avoid any legal issues. Establishing agreements, like the Alabama Ethical Hacking Agreement for External Network Security - Unannounced Penetration Test, is crucial to ensure that all parties are on the same page and to prevent any misunderstandings.
Yes, a penetration tester, or pentester, is considered a type of hacker. However, pentesters operate within the confines of the law, aiming to improve security rather than exploit vulnerabilities. They help businesses identify weaknesses before they can be abused by malicious actors. An Alabama Ethical Hacking Agreement for External Network Security - Unannounced Penetration Test lays the foundation for this important activity.
Yes, ethical hacking can be entirely legal if conducted with the necessary permissions and in compliance with applicable laws. Organizations should always establish clear agreements and protocols to guide the testing process. Utilizing the Alabama Ethical Hacking Agreement for External Network Security - Unannounced Penetration Test clarifies roles and responsibilities, ensuring legal compliance throughout the engagement.
The average salary of a white hat hacker, or ethical hacker, varies based on experience and location. In the United States, it typically ranges from $70,000 to $120,000 per year. Organizations value these professionals for their skills in protecting data and systems. Leveraging an Alabama Ethical Hacking Agreement for External Network Security - Unannounced Penetration Test can ensure you find qualified candidates who adhere to best practices.
Ethical hacking testing is legal when performed with proper authorization. Organizations must obtain explicit consent to test their systems, ensuring compliance with laws and regulations. This process not only protects the ethical hacker but also establishes trust between parties. The Alabama Ethical Hacking Agreement for External Network Security - Unannounced Penetration Test is a helpful tool in formalizing such legal permissions.
Yes, ethical hackers conduct various types of testing to assess the security of networks and systems. They simulate potential attacks to identify vulnerabilities before malicious hackers can exploit them. This proactive approach is essential for organizations aiming to enhance their security posture. Utilizing an Alabama Ethical Hacking Agreement for External Network Security - Unannounced Penetration Test helps formalize these testing arrangements.
A thorough test should include extensive vulnerability assessments, exploitation attempts, and post-testing report generation. This ensures a clear understanding of security gaps and the necessary remediation steps. By adhering to the Alabama Ethical Hacking Agreement for External Network Security - Unannounced Penetration Test, organizations can effectively safeguard their systems and data.
The primary role of ethical hacking is to identify vulnerabilities within systems before malicious hackers can exploit them. Testing, on the other hand, provides a comprehensive assessment of an organization's overall security posture. In the context of the Alabama Ethical Hacking Agreement for External Network Security - Unannounced Penetration Test, both practices are crucial for enhancing security and protecting sensitive information.
A testing agreement generally includes sections on the scope of work, responsibilities of both parties, and confidentiality provisions. This structure ensures transparency and professionalism during the Alabama Ethical Hacking Agreement for External Network Security - Unannounced Penetration Test. Having defined sections helps prevent misunderstandings and establishes a solid foundation for collaboration.