Get Pairings In Trusted Computing. Pairings Have Now Been Used For Constructive Applications In
How it works
-
Open form follow the instructions
-
Easily sign the form with your finger
-
Send filled & signed form or save
Tips on how to fill out, edit and sign Pairings In Trusted Computing. Pairings Have Now Been Used For Constructive Applications In online
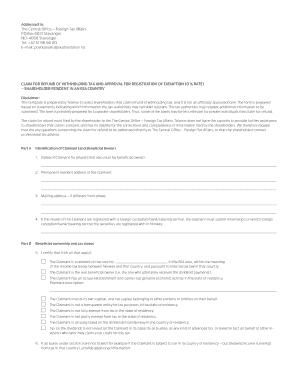
How to fill out and sign Pairings In Trusted Computing. Pairings Have Now Been Used For Constructive Applications In online?
Get your online template and fill it in using progressive features. Enjoy smart fillable fields and interactivity.Follow the simple instructions below:
The days of terrifying complicated tax and legal forms have ended. With US Legal Forms the entire process of filling out official documents is anxiety-free. The best editor is directly close at hand providing you with a wide variety of advantageous instruments for filling out a Pairings In Trusted Computing. Pairings Have Now Been Used For Constructive Applications In. These guidelines, together with the editor will assist you through the entire process.
- Select the Get Form button to start editing.
- Switch on the Wizard mode on the top toolbar to have additional tips.
- Fill every fillable field.
- Ensure that the data you add to the Pairings In Trusted Computing. Pairings Have Now Been Used For Constructive Applications In is updated and accurate.
- Include the date to the document using the Date function.
- Click on the Sign tool and make a digital signature. You can find 3 available alternatives; typing, drawing, or capturing one.
- Re-check every field has been filled in correctly.
- Select Done in the top right corne to save the file. There are various options for getting the doc. An attachment in an email or through the mail as a hard copy, as an instant download.
We make completing any Pairings In Trusted Computing. Pairings Have Now Been Used For Constructive Applications In much easier. Use it now!
How to edit Pairings In Trusted Computing. Pairings Have Now Been Used For Constructive Applications In: customize forms online
Use our comprehensive editor to transform a simple online template into a completed document. Keep reading to learn how to edit Pairings In Trusted Computing. Pairings Have Now Been Used For Constructive Applications In online easily.
Once you find an ideal Pairings In Trusted Computing. Pairings Have Now Been Used For Constructive Applications In, all you have to do is adjust the template to your needs or legal requirements. Apart from completing the fillable form with accurate details, you might need to remove some provisions in the document that are irrelevant to your circumstance. On the other hand, you might like to add some missing conditions in the original form. Our advanced document editing tools are the best way to fix and adjust the form.
The editor lets you modify the content of any form, even if the file is in PDF format. You can add and erase text, insert fillable fields, and make extra changes while keeping the initial formatting of the document. You can also rearrange the structure of the form by changing page order.
You don’t have to print the Pairings In Trusted Computing. Pairings Have Now Been Used For Constructive Applications In to sign it. The editor comes along with electronic signature functionality. The majority of the forms already have signature fields. So, you only need to add your signature and request one from the other signing party via email.
Follow this step-by-step guide to create your Pairings In Trusted Computing. Pairings Have Now Been Used For Constructive Applications In:
- Open the preferred form.
- Use the toolbar to adjust the template to your preferences.
- Complete the form providing accurate details.
- Click on the signature field and add your eSignature.
- Send the document for signature to other signers if necessary.
After all parties complete the document, you will receive a signed copy which you can download, print, and share with other people.
Our solutions let you save tons of your time and minimize the risk of an error in your documents. Enhance your document workflows with efficient editing tools and a powerful eSignature solution.
Industry-leading security and compliance
-
In businnes since 199725+ years providing professional legal documents.
-
Accredited businessGuarantees that a business meets BBB accreditation standards in the US and Canada.
-
Secured by BraintreeValidated Level 1 PCI DSS compliant payment gateway that accepts most major credit and debit card brands from across the globe.


