Loading
Get Doc Code: - Integrity Ip
How it works
-
Open form follow the instructions
-
Easily sign the form with your finger
-
Send filled & signed form or save
How to fill out the Doc Code: - Integrity IP online
This guide provides comprehensive instructions on how to fill out the Doc Code: - Integrity IP online. It is designed to assist users, including those with limited legal experience, in navigating the form with ease and confidence.
Follow the steps to successfully complete the form
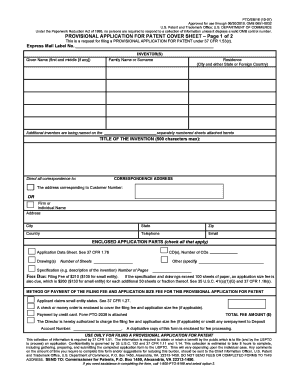
- Click the ‘Get Form’ button to obtain the Provisional Application for Patent Cover Sheet and open it in your preferred editing tool.
- Begin by filling in the express mail label number, if applicable. Then, provide the given name(s) of the inventor(s), including their family name or surname.
- Include the residence of the inventor(s), specifying the city along with either the state or foreign country.
- If there are additional inventors, indicate that on separately numbered sheets attached to the application.
- Fill in the title of the invention. Ensure that the title does not exceed 500 characters.
- Provide the correspondence address, which should include the customer number, name (firm or individual), address, city, state, zip, country, telephone, and email.
- Check all applicable enclosed application parts. These can include an application data sheet, drawings, CDs, the number of sheets, specification, or any other necessary parts.
- Specify the method of payment for the filing fee and application size fee, if applicable. Indicate if you are claiming small entity status and indicate the total fee amount.
- Complete the authorization for charging the fees to a deposit account, if this is your chosen method of payment.
- Sign and date the form, providing your typed or printed name. Include any applicable registration number and telephone number along with a docket number.
- Once all sections are completed, review the form for accuracy. You can then save changes, download, print, or share the form as needed.
Begin the process by completing the Doc Code: - Integrity IP online today!
Code integrity is a threat protection feature that checks the drivers and system files on your device for signs of corruption or malicious software. For code integrity to work on your device, another security feature called Secure Boot must be enabled.
Industry-leading security and compliance
US Legal Forms protects your data by complying with industry-specific security standards.
-
In businnes since 199725+ years providing professional legal documents.
-
Accredited businessGuarantees that a business meets BBB accreditation standards in the US and Canada.
-
Secured by BraintreeValidated Level 1 PCI DSS compliant payment gateway that accepts most major credit and debit card brands from across the globe.


