Loading
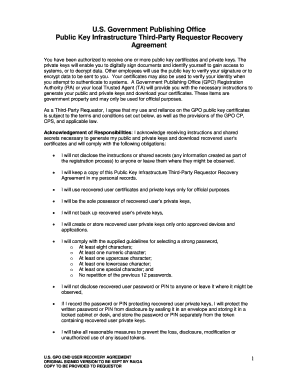
Get Gpo Public Key Infrastructure Third-party Requestor Recovery Agreement 2018-2025
How it works
-
Open form follow the instructions
-
Easily sign the form with your finger
-
Send filled & signed form or save
How to fill out the GPO Public Key Infrastructure Third-Party Requestor Recovery Agreement online
This guide will provide you with comprehensive instructions on how to complete the GPO Public Key Infrastructure Third-Party Requestor Recovery Agreement online. Following these steps will ensure that you can accurately fill out the necessary fields and understand your responsibilities as a third-party requestor.
Follow the steps to accurately complete the agreement.
- Click ‘Get Form’ button to obtain the form and open it in the online editor.
- Review the introduction section where you will find crucial information regarding the agreement. Ensure you understand the purpose and significance of the public key certificates and private keys involved.
- Complete the acknowledgment of responsibilities section by reading each statement carefully. Confirm that you understand and accept each condition related to the use of certificates and private keys.
- Fill in your name, date, and telephone number in the appropriate fields as required in the final sections of the agreement.
- If applicable, have a witness present while signing. The witness should also fill in their details as stated in the document.
- Review the entire form to ensure that all information is accurate and complete before submission.
- Once you are satisfied with the completed form, proceed to save, download, print, or share the form as needed.
Complete the GPO Public Key Infrastructure Third-Party Requestor Recovery Agreement online today.
Parenting classes can help parents learn more about what to expect in the coming years and prepare for each developmental stage. Since confident, decisive parents tend to raise confident, secure children, parenting classes can give you a much-needed skill set and help decrease your feelings of anxiety.
Industry-leading security and compliance
US Legal Forms protects your data by complying with industry-specific security standards.
-
In businnes since 199725+ years providing professional legal documents.
-
Accredited businessGuarantees that a business meets BBB accreditation standards in the US and Canada.
-
Secured by BraintreeValidated Level 1 PCI DSS compliant payment gateway that accepts most major credit and debit card brands from across the globe.


