Loading
Get Hacking Agreement
How it works
-
Open form follow the instructions
-
Easily sign the form with your finger
-
Send filled & signed form or save
How to fill out the Hacking Agreement online
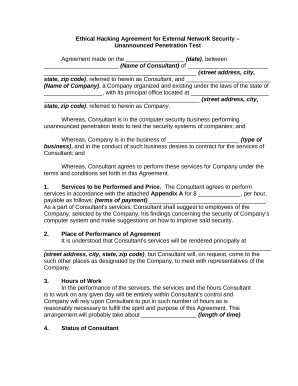
Completing the Hacking Agreement online is a straightforward process that ensures the necessary contractual obligations are established between the consultant and the company. This guide provides clear, step-by-step instructions tailored to support every user, regardless of prior legal experience.
Follow the steps to complete the Hacking Agreement online.
- Click ‘Get Form’ button to obtain the form and open it in the editor.
- Enter the date in the designated section where it states 'Agreement made on the __________________ (date)'. This specifies when the agreement will take effect.
- Input the name of the consultant where it mentions '_______________________ (Name of Consultant)'. This identifies the individual responsible for conducting the hacking tests.
- Provide the consultant's full address in the format: '_______________________________________________ (street address, city, state, zip code)'. Accurate address information ensures proper communication.
- Fill in the name of the company in the section marked '__________________________ (Name of Company)', which formally identifies the entity contracting the consultant's services.
- Specify the state where the company is organized in the blank space following 'under the laws of the state of _______________'. This is essential for legal jurisdiction.
- Repeat the address requirement for the company's principal office in 'with its principal office located at ________________________ (street address, city, state, zip code)'.
- In section 1, enter the agreed-upon price for services in the blank space '$ _____________, per hour'. This defines the financial terms for the agreement.
- Describe the terms of payment in the section that states '(terms of payment) ____________________________________'. Clear payment terms help prevent disputes.
- Continue filling in the 'Place of Performance of Agreement' by providing any additional locations where the services may be rendered.
- In the 'Hours of Work' section, indicate the expected length of time for the services in 'this arrangement will probably take about _________________ (length of time)'.
- Complete sections regarding 'Status of Consultant', 'Subcontracts', 'No Waiver', 'Governing Law', and any other relevant sections, ensuring to fill every designated blank according to your agreement specifics.
- Review the entire document for accuracy before signing. Inform all signatory parties to provide their printed names and signatures in the designated areas.
- Finally, save changes to the document, download, print, or share the agreement as necessary to finalize the process.
Complete your Hacking Agreement online now for streamlined processing and documentation.
Hacking is identifying and exploiting weaknesses in computer systems and/or computer networks. Cybercrime is committing a crime with the aid of computers and information technology infrastructure. Ethical Hacking is about improving the security of computer systems and/or computer networks. Ethical Hacking is legal.


