Loading
Get Fraud Checklist Sample
How it works
-
Open form follow the instructions
-
Easily sign the form with your finger
-
Send filled & signed form or save
How to use or fill out the Fraud Checklist Sample online
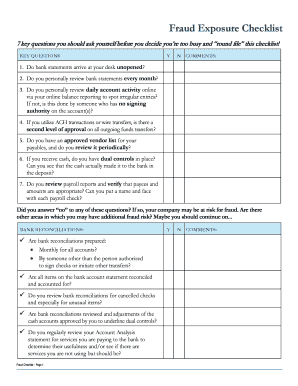
The Fraud Checklist Sample is an essential tool for evaluating your organization's internal controls and identifying potential fraud risks. This guide will provide clear and supportive instructions on how to fill out the checklist effectively online to enhance your fraud prevention measures.
Follow the steps to complete the Fraud Checklist Sample online.
- Press the ‘Get Form’ button to access the Fraud Checklist Sample and open it in your preferred online editor.
- Begin by reviewing each of the key questions listed in the checklist. Answer each question with a 'Yes' or 'No' and provide comments to clarify your responses.
- Move to the bank reconciliations section. Ensure you answer the questions regarding the preparation and review of bank reconciliations, including who is responsible for them.
- Proceed to the A/R and A/P controls section. Confirm that all necessary controls are in place and provide information as needed.
- In the cash receipts section, validate that cash handling procedures are satisfied and added comments where relevant.
- Review the check stock section. Make sure that all necessary checks and balances are indicated in your responses.
- Complete the electronic banking section by answering questions pertaining to your online banking practices and security measures.
- Finally, review the miscellaneous section to ensure all additional fraud prevention measures are documented.
- Once you have completed all sections, save your changes. You may download, print, or share the completed form as needed.
Take action now by completing your Fraud Checklist Sample online.
The Fraud Triangle hypothesizes that if all three components are present — unshareable financial need, perceived opportunity and rationalization — a person is highly likely to pursue fraudulent activities.


