Loading
Get Cyber Branch Questionnaire 2016-2026
How it works
-
Open form follow the instructions
-
Easily sign the form with your finger
-
Send filled & signed form or save
How to fill out the Cyber Branch Questionnaire online
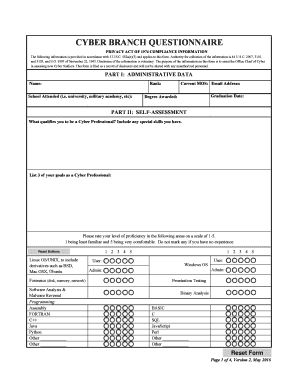
Completing the Cyber Branch Questionnaire online is essential for providing necessary information to assist the Office Chief of Cyber in evaluating new Cyber Soldiers. This guide offers clear step-by-step instructions to help users fill out the form accurately and effectively.
Follow the steps to complete the Cyber Branch Questionnaire with ease.
- Press the ‘Get Form’ button to access the questionnaire and open it in your preferred online editor.
- Begin with Part I: Administrative Data. Fill in your full name, current Military Occupational Specialty (MOS), email address, rank, name of the school you attended, graduation date, and the degree awarded. It is crucial to provide accurate information to reflect your qualifications.
- Proceed to Part II: Self-Assessment. Describe what qualifies you to be a Cyber Professional by highlighting your skills and experience. List three professional goals you intend to achieve in this field and assess your proficiency in specified technical areas using a scale from 1 to 5. Only mark areas where you have experience.
- Move to Part III: Technical Assessment. Start by listing any internships or relevant industry experience. Share any personal hobbies or interests that relate to technology or cybersecurity. Answer the technical problem-solving questions provided, which may involve command definitions, logical evaluations, and problem-solving scenarios.
- Continue answering the remaining technical assessment questions, including technical command analysis and examining scenarios related to operating systems and network commands.
- After completing the questionnaire, review all sections to ensure accuracy and completeness. Correct any missing information or errors before submission.
- Finally, save your changes, and opt to download, print, or share the completed Cyber Branch Questionnaire as needed.
Start filling out the Cyber Branch Questionnaire online today to ensure your application is completed and submitted on time.
We defend military networks, secure Army weapons platforms, and protect critical U.S. infrastructure. Army Cyber forces are deployed globally, conducting defensive and offensive cyber operations 24/7.


