Loading
Get Cyber Security Risk Assessment For Msae
How it works
-
Open form follow the instructions
-
Easily sign the form with your finger
-
Send filled & signed form or save
How to fill out the Cyber Security Risk Assessment For MSAE online
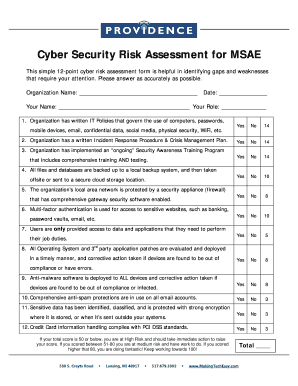
The Cyber Security Risk Assessment for MSAE is a concise tool designed to identify potential gaps in your organization's cybersecurity practices. This guide will provide you with step-by-step instructions to effectively complete the assessment online, ensuring your organization remains secure.
Follow the steps to successfully complete the Cyber Security Risk Assessment for MSAE.
- Click ‘Get Form’ button to obtain the Cyber Security Risk Assessment for MSAE document and open it in your preferred editing tool.
- Begin by entering your organization's name in the designated field. This identifies the entity undergoing the assessment.
- Next, fill in the current date to indicate when the assessment is being completed.
- Provide your name in the appropriate section. This allows the assessment to be attributed to a specific individual.
- Indicate your role within the organization. This helps contextualize your perspective when answering the subsequent questions.
- Proceed to answer each of the 12 questions in the assessment, using the provided 'Yes' or 'No' options to reflect your organization’s cybersecurity practices.
- For each question, provide any relevant comments or explanations if prompted, to ensure clarity about your responses.
- After completing all sections and questions, review your answers for accuracy.
- Finally, save changes, download a copy, print if necessary, or share the completed assessment with relevant stakeholders.
Complete your Cyber Security Risk Assessment for MSAE online today to enhance your organization's security posture.
A cybersecurity risk assessment evaluates the organization's vulnerabilities and threats to identify the risks it faces. It also includes recommendations for mitigating those risks. A risk estimation and evaluation are usually performed, followed by the selection of controls to treat the identified risks.
Industry-leading security and compliance
US Legal Forms protects your data by complying with industry-specific security standards.
-
In businnes since 199725+ years providing professional legal documents.
-
Accredited businessGuarantees that a business meets BBB accreditation standards in the US and Canada.
-
Secured by BraintreeValidated Level 1 PCI DSS compliant payment gateway that accepts most major credit and debit card brands from across the globe.


