Loading
Get Firewall Documentation Template
How it works
-
Open form follow the instructions
-
Easily sign the form with your finger
-
Send filled & signed form or save
How to fill out the Firewall Documentation Template online
Filling out the Firewall Documentation Template is essential for establishing a robust firewall system. This guide offers a clear, step-by-step process to help users complete the template effectively, ensuring comprehensive documentation of their firewall configuration.
Follow the steps to complete the Firewall Documentation Template
- Click the ‘Get Form’ button to access the template and open it in your preferred online editor.
- Begin by entering the organization’s name and contact details in the designated fields, ensuring accuracy for future reference.
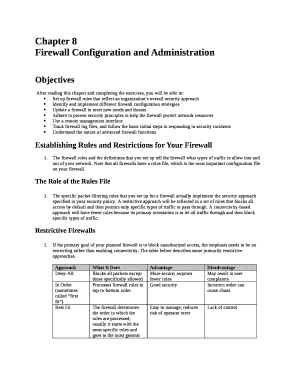
- In the firewall rules section, outline the specific packet-filtering rules you intend to implement, reflecting your organization’s security policy.
- Indicate the type of approach your firewall will take, either restrictive or connectivity-based, and explain your rationale in the provided space.
- Document the scalability features of the firewall by detailing how it will adapt to your organization’s networking needs over time.
- Include information on the remote management interface used for configuring and monitoring the firewall, emphasizing its importance.
- Review all fields for completeness and accuracy before finalizing. Ensure that the documentation adheres to the organization’s policy and best practices.
- Once satisfied, save your changes, then download, print, or share the completed form as needed for your documentation.
Start filling out your Firewall Documentation Template online today to enhance your network security!
A firewall policy defines how an organization's firewalls should handle inbound and outbound network traffic for specific IP addresses and address ranges, protocols, applications, and content types based on the organization's information security policies.
Industry-leading security and compliance
US Legal Forms protects your data by complying with industry-specific security standards.
-
In businnes since 199725+ years providing professional legal documents.
-
Accredited businessGuarantees that a business meets BBB accreditation standards in the US and Canada.
-
Secured by BraintreeValidated Level 1 PCI DSS compliant payment gateway that accepts most major credit and debit card brands from across the globe.


