Loading
Get Penetration Testing Agreement - It Security Amp Policy Office - Itsecurity Uiowa
How it works
-
Open form follow the instructions
-
Easily sign the form with your finger
-
Send filled & signed form or save
How to fill out the Penetration Testing Agreement - IT Security Amp Policy Office - Itsecurity Uiowa online
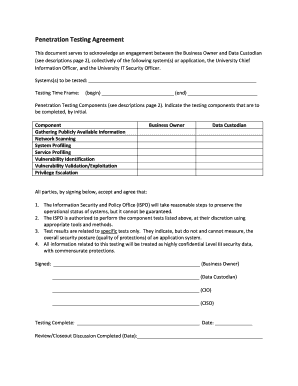
This guide provides a clear and systematic approach to completing the Penetration Testing Agreement facilitated by the IT Security and Policy Office at the University of Iowa. By following these instructions, users will be able to navigate the form efficiently and ensure all necessary details are accurately captured.
Follow the steps to successfully complete the agreement form.
- Click the ‘Get Form’ button to access and download the Penetration Testing Agreement document, allowing you to open it in your preferred online editor.
- Fill in the section for 'Systems(s) to be tested' by providing the name(s) of the application or systems that will undergo penetration testing.
- Specify the 'Testing Time Frame' by indicating the start and end dates for the testing process in the designated fields.
- Review the list of Penetration Testing Components provided. For each component that will be utilized during the testing phase, indicate your selection by initialing in the corresponding area.
- Ensure that both the Business Owner and Data Custodian sections are completed with the names and signatures of the respective individuals responsible for authorizing and overseeing the testing process.
- The Chief Information Officer (CIO) and the Chief Information Security Officer (CISO) must review and sign the document as well, confirming their involvement and agreement.
- Once all sections are complete, review your inputs for accuracy, and then save your changes. You may also choose to download, print, or share the finalized agreement as needed.
Complete your Penetration Testing Agreement online today!
Purpose. A penetration testing policy framework document provides guidance for managing a penetration testing program and performing penetration testing activities with the goal of improving defensive IT security for {Company Name}'s infrastructure, systems, services, and applications.
Industry-leading security and compliance
US Legal Forms protects your data by complying with industry-specific security standards.
-
In businnes since 199725+ years providing professional legal documents.
-
Accredited businessGuarantees that a business meets BBB accreditation standards in the US and Canada.
-
Secured by BraintreeValidated Level 1 PCI DSS compliant payment gateway that accepts most major credit and debit card brands from across the globe.


