- US Legal Forms
- Form Library
- More Forms
- More Multi-State Forms
- Breaking The Security Myths Of
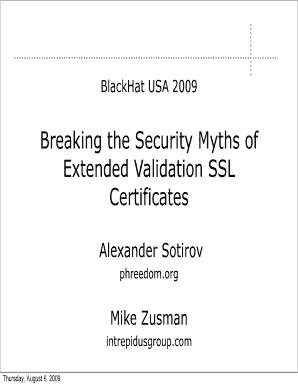
Get Breaking The Security Myths Of
L certificate authorities have been thoroughly broken in the last year or two EV-SSL is often seen as a stronger assurance of site security If SSL is broken, can we trust EV-SSL? No! A rogue non-EV certificate can be used to do MITM attacks against EV sites Thursday, August 6, 2009 Organization State of the SSL PKI EV to the rescue Breaking EV certificates mixed content attacks same origin attacks SSL rebinding cache poisoning Fixing this mess.
How It Works
-
Open form follow the instructions
-
Easily sign the form with your finger
-
Send filled & signed form or save
Tips on how to fill out, edit and sign Comodo online
How to fill out and sign Popups online?
Get your online template and fill it in using progressive features. Enjoy smart fillable fields and interactivity. Follow the simple instructions below:
Getting a authorized expert, making a scheduled visit and coming to the workplace for a personal meeting makes doing a Breaking The Security Myths Of from beginning to end tiring. US Legal Forms enables you to quickly generate legally-compliant documents according to pre-built browser-based samples.
Prepare your docs within a few minutes using our straightforward step-by-step instructions:
- Get the Breaking The Security Myths Of you want.
- Open it with online editor and begin editing.
- Fill out the blank areas; involved parties names, places of residence and phone numbers etc.
- Customize the blanks with unique fillable fields.
- Add the day/time and place your electronic signature.
- Click on Done following twice-checking everything.
- Save the ready-produced papers to your device or print it out as a hard copy.
Quickly create a Breaking The Security Myths Of without needing to involve specialists. We already have more than 3 million users benefiting from our rich library of legal documents. Join us right now and gain access to the #1 library of browser-based samples. Test it yourself!
How to edit Spoofing: customize forms online
Say goodbye to an old-fashioned paper-based way of executing Spoofing. Have the form completed and signed in minutes with our professional online editor.
Are you challenged to modify and complete Spoofing? With a robust editor like ours, you can complete this task in only minutes without having to print and scan papers back and forth. We provide completely customizable and simple form templates that will become a start and help you complete the required form online.
All files, by default, include fillable fields you can execute once you open the document. However, if you need to improve the existing content of the form or add a new one, you can choose from a number of editing and annotation options. Highlight, blackout, and comment on the document; include checkmarks, lines, text boxes, images and notes, and comments. Moreover, you can easily certify the document with a legally-binding signature. The completed form can be shared with others, stored, imported to external apps, or transformed into any popular format.
You’ll never make a wrong decision using our web-based tool to execute Spoofing because it's:
- Easy to set up and use, even for those who haven’t completed the documents online in the past.
- Robust enough to accommodate multiple modifying needs and form types.
- Safe and secure, making your editing experience protected every time.
- Available for different devices, making it stress-free to complete the form from just about anywhere.
- Capable of creating forms based on ready-drafted templates.
- Friendly to various file formats: PDF, DOC, DOCX, PPT and JPEG etc.
Don't waste time completing your Spoofing the old-fashioned way - with pen and paper. Use our feature-rich solution instead. It offers you a comprehensive suite of editing options, built-in eSignature capabilities, and ease of use. What makes it stand out is the team collaboration options - you can collaborate on forms with anyone, build a well-structured document approval workflow from A to Z, and a lot more. Try our online solution and get the best value for your money!
Experience a faster way to fill out and sign forms on the web. Access the most extensive library of templates available.
PKI Related content
-
The myths and truths of wireless security
by A Loo · 2008 · Cited by 15 — They might decide it is not worthwhile to break into...
Learn more -
Security Myths and Passwords - CERIAS - Purdue...
If any of the other attack methods succeed, the password needs to be changed immediately...
Learn more -
The Three Myths of Firewalls
1. We've got the place surrounded. Firewalls make the assumption that the only way in or...
Learn more -
Dispelling the Myths
What is the Protect America Act? Dispelling the Myths ... "Peaceful groups that dissent...
Learn more -
8 Myths About Cybersecurity Careers
Dec 8, 2023 — Is cybersecurity a good career? The definitive answer is yes. No company...
Learn more -
Fact vs Fiction: The Truth About Hackers
Myth #3: Hackers can guess your password easily Reality: Breaking into a computer is...
Learn more -
The Myth of Cyberwar Erik Gartzke
by E Gartzke · 2013 · Cited by 461 — the myth of a cyber pearl harbor. The air strikes...
Learn more -
(PDF) The myths and facts behind cyber security...
The myths and facts behind cyber security risks for industrial control systems. ... The...
Learn more -
Lessons from Lockpicking: Perfect security is a...
Jun 1, 2012 — Because, a lock is only strong until someone learns how to pick it or...
Learn more -
Dispelling the Myths about Information Sharing...
In the case of correctional facilities, HIPAA permits health information to be shared with...
Learn more -
Dispelling the Myths
The Supreme Court has expressly recognized that detaining aliens may be appropriate in...
Learn more -
Dispelling the Myths about Information Sharing...
As systems get beyond the myths regarding sharing of information under HIPAA, it will be...
Learn more -
Clean Slate Act Myths and Facts
Clean Slate does not lessen sentences or penalties and does not affect orders of...
Learn more -
Mental Health Myths and Facts
Apr 24, 2023 — Myth: Mental health issues can't affect me. · Myth: Children don't...
Learn more -
Myths and Reality of an SBOM
Jun 2, 2021 — Any process requiring a distinct step involving humans is bound to break...
Learn more -
The Myth of Revolutionary Technologies
early 19th century in the form of coded, wooden, card ... breaking German military codes...
Learn more -
Privacy and security in the era of digital health...
by BL Filkins · 2016 · Cited by 200 — Working through some of these myths can enhance...
Learn more -
Election Security Rumor vs. Reality
Rumor: People can easily violate the integrity of the mail-in/absentee ballot request...
Learn more -
debunking national myths: Topics by ...
... myths should be examined. These myths include suggestions that nonstandard dialects...
Learn more -
Dispelling the Myths
The Supreme Court has expressly recognized that detaining aliens may be appropriate in...
Learn more -
Employers and the ADA: Myths and Facts
Myth: Under the ADA, an employer cannot fire an employee who has a disability. Fact:...
Learn more -
Dispelling the Myths about Information Sharing...
As systems get beyond the myths regarding sharing of information under HIPAA, it will be...
Learn more -
Clean Slate Act Myths and Facts
Clean Slate does not lessen sentences or penalties and does not affect orders of...
Learn more -
Mental Health Myths and Facts
Apr 24, 2023 — Myth: Mental health issues can't affect me. · Myth: Children don't...
Learn more -
Myths and Reality of an SBOM
Jun 2, 2021 — Any process requiring a distinct step involving humans is bound to break...
Learn more -
The Myth of Revolutionary Technologies
early 19th century in the form of coded, wooden, card ... breaking German military codes...
Learn more -
Privacy and security in the era of digital health...
by BL Filkins · 2016 · Cited by 200 — Working through some of these myths can enhance...
Learn more -
Election Security Rumor vs. Reality
Rumor: People can easily violate the integrity of the mail-in/absentee ballot request...
Learn more -
debunking national myths: Topics by ...
... myths should be examined. These myths include suggestions that nonstandard dialects...
Learn more -
Employers and the ADA: Myths and Facts
Myth: Under the ADA, an employer cannot fire an employee who has a disability. Fact:...
Learn more -
The myths and truths of wireless security
by A Loo · 2008 · Cited by 15 — They might decide it is not worthwhile to break into...
Learn more -
The Three Myths of Firewalls
1. We've got the place surrounded. Firewalls make the assumption that the only way in or...
Learn more -
Security Myths and Passwords - CERIAS - Purdue...
If any of the other attack methods succeed, the password needs to be changed immediately...
Learn more -
8 Myths About Cybersecurity Careers
8 Dec 2023 — Is cybersecurity a good career? The definitive answer is yes. No company or...
Learn more -
Top 10 Myths About Identity Theft
11 Nov 2016 — Myth 5: Identity theft criminals don't know their victims. While...
Learn more -
Roland Barthes' Mythologies
Invented forms are very rare: a few sets of blocks, which appeal to the spirit of...
Learn more -
(PDF) The myths and facts behind cyber security...
The myths and facts behind cyber security risks for industrial control systems. ... The...
Learn more -
4 common myths of maintenance agreements
The origins of modern maintenance agreements start in the 1980s. Ron. Smith, a service...
Learn more -
The Myth of Cyberwar Erik Gartzke
by E Gartzke · 2013 · Cited by 461 — 4. The Myth of Cyberwar. The Myth of Cyberwar...
Learn more -
Big Data Lab
Jan 31, 2024 — Commercial bribery is a form of bribery, which involves corrupt dealing...
Learn more -
Dispelling the Myths
What is the Protect America Act? Dispelling the Myths ... "Peaceful groups that dissent...
Learn more -
Shattered Dreams Program Guide - Grand County
This guide is free for use by any school or community interested in conducting a Shattered...
Learn more -
The Myths and Realities of the Internet Kill...
by SM Ruggiero · 2017 · Cited by 13 — 22 Few regula- tory laws exist that provide...
Learn more -
Mission:Blood Begets Blood - Part Two: An Ivory...
Sorceress Serene has gone to great lengths to ensure that her power goes unchecked in...
Learn more -
Mental Health Myths and Facts
24 Apr 2023 — Myth: People with mental health conditions are violent. Fact: Most...
Learn more -
Oilcraft: The Myths of Scarcity and Security that...
11 Mar 2021 — The book questions deeply held beliefs about the role of oil in US foreign...
Learn more -
Mochimanoban Author's page
Deliah was a small sentient contraption built by Vyktyr Strutheo of Meskaovania using a...
Learn more -
The Myth of Revolutionary Technologies
4 The Myth of Revolutionary Technologies. 10 NetTop Eight ... breaking German military...
Learn more -
Human Practices | Cornell - iGEM 2022
We believe that through intentional outreach and conscious education, our project can...
Learn more -
Dispelling the Myths
What is the Protect America Act? Dispelling the Myths ... "Peaceful groups that dissent...
Learn more -
Claude/Lore
Claude is the rightful king of Kelkale, a once prosperous kingdom below the floating...
Learn more -
the myths of scarcity and security that haunt U.S...
A bracing corrective to the myths that have shaped economic, military, and diplomatic...
Learn more -
The Stories Bodies Tell - Archaeology Wiki
Jun 16, 2021 — The Stories Bodies Tell is an inclusive interdisciplinary symposium...
Learn more -
Privacy and security in the era of digital health...
by BL Filkins · 2016 · Cited by 200 — Working through some of these myths can enhance...
Learn more -
Laura Brunetti
Jan 8, 2024 — These ancient myths ... These swirling crimson sands are enchanted to form...
Learn more -
debunking national myths: Topics by ...
... myths and refuting those myths ... This myth may contribute to a potentially dangerous...
Learn more -
Myths and Reality of an SBOM
2 Jun 2021 — An SBOM is not a piece of product security by itself. It is a set of...
Learn more -
Myths and Facts about Children and Fire
Myth: If you take a child to the burn unit to see burn survivors, he/she will stop...
Learn more -
5 MYTHS ABOUT UNDOCUMENTED IMMIGRANTS
MYTH #1: Anyone who enters the country illegally is a criminal. Facts: Being an...
Learn more -
Exposing the myths of household water insecurity...
by K Meehan · 2020 · Cited by 129 — Safe and secure water is a cornerstone of modern...
Learn more -
Roland Barthes' Mythologies
In this way Einstein fulfils all the conditions of myth, which could not care less about...
Learn more -
4 common myths of maintenance agreements
Breaking down while under a maintenance agreement is the worst possible scenario. It...
Learn more -
Song of Sword and Wings of Lost Paradise
Jan 12, 2024 — A land said to be abandoned by the very stars themselves. There the...
Learn more -
Half Loop - Severance Wiki
Graner runs over from Security and begins to lead ... Break Room. ... While Dylan and...
Learn more -
A Look At The Myths And Facts Behind Ghosttracker...
A Look At The Myths And Facts Behind Ghosttracker ... This device is designed to prevent...
Learn more -
American Coalition for Clean Coal Electricity...
American Coalition for Clean Coal Electricity (ACCCE) is a coal industry front group...
Learn more -
The Myth of Male Power (book)
Jul 23, 2021 — The Myth of Male Power is the most famous MRA book, published in 1993 by...
Learn more -
New study debunks myth of Cahokia's Native...
Jan 28, 2020 — By the 1400s, Cahokia had been abandoned due to floods, droughts...
Learn more -
Cadao Kestrel
Late last night, Akarist's warded safe house was broken into, his guards incapacitated...
Learn more -
scientific argumentation
by V SAMPSON · 2016 — nature of science: Dispelling the myths of ... less secure than...
Learn more -
Roland Barthes' Mythologies
In this way Einstein fulfils all the conditions of myth, which could not care less about...
Learn more -
4 common myths of maintenance agreements
Breaking down while under a maintenance agreement is the worst possible scenario. It...
Learn more -
Cadao Kestrel
In our myths she was the former lover of Ermeeth, the god who taught our people the magic...
Learn more -
Mochimanoban Author's page
Just a fun little article as a creative break from polishing articles ready for the World...
Learn more -
Half Loop - Severance Wiki
Graner runs over from Security and begins to lead ... Break Room. ... While Dylan and...
Learn more -
Claude/Lore
Claude is the rightful king of Kelkale, a once prosperous kingdom below the floating...
Learn more -
Robert Falcon Scott
Captain Robert Falcon Scott, CVO, RN (6 June 1868 – 29 March 1912) was a British Royal...
Learn more -
A Look At The Myths And Facts Behind Ghosttracker...
A Look At The Myths And Facts Behind Ghosttracker ... This device is designed to prevent...
Learn more -
Treasure Trails/Guide/Cryptic clues
Jun 29, 2022 — Cryptic clues are common riddle clues that can be found in all tiers of...
Learn more -
Monochrome Inc.
In this cooperative game, you and your team will break into Monochrome Inc. ... 402:...
Learn more -
Roland Barthes' Mythologies
The form of myth is not a symbol: the Negro who salutes is not the symbol of the French...
Learn more -
4 common myths of maintenance agreements
The origins of modern maintenance agreements start in the 1980s. Ron. Smith, a service...
Learn more -
Mochimanoban Author's page
Deliah was a small sentient contraption built by Vyktyr Strutheo of Meskaovania using a...
Learn more -
Big Data Lab
Jan 31, 2024 — Unlike most myths ... Commonly used to make hand-woven items, the inside...
Learn more -
Mission:Blood Begets Blood - Part Two: An Ivory...
Sorceress Serene has gone to great lengths to ensure that her power goes unchecked in...
Learn more -
Security for Industrial Automation and Control...
Oct 22, 2010 — Byres, Eric; Lowe, Justin; The Myths and Facts behind Cyber Security...
Learn more -
Human Practices | Cornell - iGEM 2022
We believe that through intentional outreach and conscious education, our project can...
Learn more -
Robert Falcon Scott
Captain Robert Falcon Scott, CVO, RN (6 June 1868 – 29 March 1912) was a British Royal...
Learn more -
Emilyarmstrong Author's page
A Horror Anthology of Eldritch Space, Myth Monsters & Forest Frights. Available now in...
Learn more -
Herodotus Helpline: 2024 Seminars - Archaeology...
Jan 18, 2024 — A mix of traditional seminar format, 'retrospective' sessions, and...
Learn more -
Dispelling the Myths
What is the Protect America Act? Dispelling the Myths ... "Peaceful groups that dissent...
Learn more -
Dispelling the Myths
WAGING THE WAR ON TERROR. For decades, terrorists have waged war against U.S. interests...
Learn more -
Mental Health Myths and Facts
Apr 24, 2023 — Myth: Mental health issues can't affect me. · Myth: Children don't...
Learn more -
Cybersecurity
There are many cybersecurity myths that persist that can put our personal and IHS data at...
Learn more -
Dispelling the Myths about Information Sharing...
As systems get beyond the myths regarding sharing of information under HIPAA, it will be...
Learn more -
Clean Slate Act Myths and Facts
Myth: Sealing records encourages people to commit more crimes. Fact: As people secure...
Learn more -
The Myth of Revolutionary Technologies
4 The Myth of Revolutionary Technologies. 10 NetTop Eight ... breaking German military...
Learn more -
Myths and Reality of an SBOM
Jun 2, 2021 — An SBOM is not a piece of product security by itself. It is a set of...
Learn more -
Fact-Checking President Biden's Myth-Filled Plan...
Oct 11, 2023 — Myth: Title II will protect innovative offerings. Fact: The Title II...
Learn more -
Myth vs. Fact: DHS Zero-Tolerance Policy
Jun 18, 2018 — Myth. DHS separates families who entered at the ports of entry and who...
Learn more -
Security Myths and Passwords - CERIAS - Purdue...
Cracking is when an intermediate form of the password (e.g., an encrypted form stored in...
Learn more -
The Three Myths of Firewalls
3. Sticks and Stones may break my bones, but words will never hurt me. ... This myth may...
Learn more -
Dispelling the Myths about Information Sharing...
As systems get beyond the myths regarding sharing of information under HIPAA, it will be...
Learn more -
8 Myths About Cybersecurity Careers
Dec 8, 2023 — Is cybersecurity a good career? The definitive answer is yes. No company...
Learn more -
(PDF) Budgam Breaking the myth of excessive force...
Budgam: Breaking the myth of excessive force by security forces in Kashmir. It is relevant...
Learn more -
The Myth of the Privacy Paradox - Scholarly...
by DJ Solove · 2020 · Cited by 310 — In this Article, Professor Daniel Solove...
Learn more -
The Myth of Cyberwar Erik Gartzke
by E Gartzke · 2013 · Cited by 461 — Schweller, “Neorealism's Status-Quo Bias: What...
Learn more -
Capability Myths Demolished
by MS Miller · Cited by 200 — We address three common misconceptions about...
Learn more -
Top 10 Myths About Identity Theft
Nov 11, 2016 — Myth 5: Identity theft criminals don't know their victims. While...
Learn more -
7 Myths of Leadership in Business
by R Bogosian — The employee culture forms opinions about leaders based on what they see...
Learn more -
Security Myths and Passwords - CERIAS - Purdue...
If any of the other attack methods succeed, the password needs to be changed immediately...
Learn more -
The Three Myths of Firewalls
3. Sticks and Stones may break my bones, but words will never hurt me. ... This myth may...
Learn more -
8 Myths About Cybersecurity Careers
Dec 8, 2023 — Is cybersecurity a good career? The definitive answer is yes. No company...
Learn more -
Dispelling the Myths about Information Sharing...
As systems get beyond the myths regarding sharing of information under HIPAA, it will be...
Learn more -
The Myth of the Privacy Paradox - Scholarly...
by DJ Solove · 2020 · Cited by 310 — In this Article, Professor Daniel Solove...
Learn more -
Fact vs Fiction: The Truth About Hackers
Myth #3: Hackers can guess your password easily. Reality: Breaking into a computer is no...
Learn more -
The Myth of Cyberwar Erik Gartzke
by E Gartzke · 2013 · Cited by 461 — Schweller, “Neorealism's Status-Quo Bias: What...
Learn more -
(PDF) The myths and facts behind cyber security...
The myths and facts behind cyber security risks for industrial control systems.
Learn more -
The Myths and Realities of the Internet Kill...
by SM Ruggiero · 2017 · Cited by 13 — 22 Few regula- tory laws exist that provide...
Learn more -
7 Myths of Leadership in Business
by R Bogosian — The employee culture forms opinions about leaders based on what they see...
Learn more
Use professional pre-built templates to fill in and sign documents online faster. Get access to thousands of forms.
Keywords relevant to Breaking The Security Myths Of
- JavaScript
- Rebinding
- phishing
- paypalobjects
- Popup
- blahblahblah
- MD5
- PKI
- Comodo
- Webtrust
- analytics
- popups
- Spoofing
- iframe
- OSCP
USLegal fulfills industry-leading security and compliance standards.
-

VeriSign secured
#1 Internet-trusted security seal. Ensures that a website is free of malware attacks.
-
Accredited Business
Guarantees that a business meets BBB accreditation standards in the US and Canada.
-

TopTen Reviews
Highest customer reviews on one of the most highly-trusted product review platforms.