- US Legal Forms
- Form Library
- More Forms
- More Multi-State Forms
- Customer Details Token / Password Request Add / Edit Authorised ...
Get Customer Details Token / Password Request Add / Edit Authorised ...
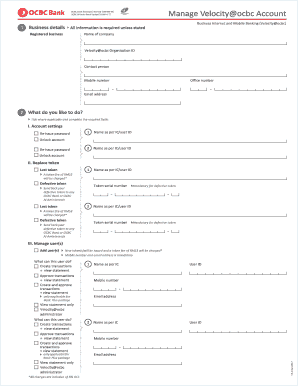
S Internet and Mobile Banking (Velocity ocbc) Name of company Velocity ocbc Organisation ID Contact person Mobile number Office number Email address 2 What do you like to do? Tick where applicable and complete the required fields I. Account settings Re-issue password 1 Name as per IC/user ID 2 Name as per IC/user ID 1 Name as per IC/user ID Unlock account Re-issue password Unlock account II. Replace token Lost token A token fee of RM53 will be charged* Defective token Token seri.
How It Works
-
Open form follow the instructions
-
Easily sign the form with your finger
-
Send filled & signed form or save
How to fill out and sign RM53 online?
Get your online template and fill it in using progressive features. Enjoy smart fillable fields and interactivity. Follow the simple instructions below:
Choosing a legal expert, making an appointment and coming to the business office for a personal meeting makes finishing a Customer Details Token / Password Request Add / Edit Authorised ... from start to finish exhausting. US Legal Forms allows you to quickly generate legally binding documents based on pre-created online templates.
Perform your docs within a few minutes using our straightforward step-by-step guide:
- Get the Customer Details Token / Password Request Add / Edit Authorised ... you need.
- Open it with online editor and start altering.
- Complete the empty fields; involved parties names, places of residence and phone numbers etc.
- Change the template with unique fillable areas.
- Put the day/time and place your e-signature.
- Click on Done after twice-checking all the data.
- Save the ready-made record to your gadget or print it like a hard copy.
Rapidly generate a Customer Details Token / Password Request Add / Edit Authorised ... without having to involve specialists. We already have over 3 million customers benefiting from our unique library of legal forms. Join us today and gain access to the top catalogue of web templates. Give it a try yourself!
Experience a faster way to fill out and sign forms on the web. Access the most extensive library of templates available.
LLP FAQ
-
Step 1: Set authorization parameters. Step 2: Redirect to Google's OAuth 2.0 server. Step 3: Google prompts user for consent. Step 4: Handle the OAuth 2.0 server response. Step 5: Exchange authorization code for refresh and access s.
-
To create a new auth : In the top-right corner of the Console, open the Profile menu and then click User Settings to view the details. On the Auth s page, click Generate . Enter a friendly description for the auth .
-
How Does -based Authentication Work? Most people have used -based process in some form. For example, gaining access to an online account by entering a code sent as a one-time password, using a fingerprint to unlock a mobile phone, and accessing a website through a Facebook login are all common examples.
-
To get the Client Access for an app, do the following: Sign into your developer account. On the Apps page, select an app to open the dashboard for that app. On the Dashboard, navigate to Settings > Advanced > Security > Client .
-
Get Access s To request an access , make a POST call to the URL. When a user authenticates, you request an access and include the target audience and scope of access in your request. ... In only one specific instance, access s can have multiple target audiences.
-
The following section describes the steps for obtaining the access and refresh using the authorization code grant mechanism: Step 1: Authenticate a User and Create a User Session. Step 2: [Optional] Generating Client Credentials. Step 3: Generate Authorization Code. Step 4: Exchange Auth Code for a .
-
Get Access s To request an access , make a POST call to the URL. When a user authenticates, you request an access and include the target audience and scope of access in your request. ... In only one specific instance, access s can have multiple target audiences.
-
The Authorization Code grant type is used by confidential and public clients to exchange an authorization code for an access . After the user returns to the client via the redirect URL, the application will get the authorization code from the URL and use it to request an access .
GST Related content
-
Identity & Access Frequently Asked Questions...
Sep 18, 2021 — I&A allows you to create one account to access NPPES, PECOS, and EHR...
Learn more -
Understand and utilize EDGAR CIKs, passphrases...
Apr 6, 2023 — Follow these steps to reset your CCC at either the EDGAR Filing or EDGAR...
Learn more -
Authentication and Access to Financial Institution...
This Guidance sets forth risk management principles and practices that can support a...
Learn more -
MHPD User Manual - New York State Office of Mental...
A User with Provider access can submit Change Requests,. Administrative Actions and EZPARs...
Learn more -
Services Online and Login.gov
Submit your information below and one of our Customer Service Specialists will begin...
Learn more -
Privacy Act; System of Records
Sep 14, 2023 — User administration activities: Added user, Deleted user, Set license...
Learn more -
Security Management System (SMS) Manual...
16-Mar-2022 — This manual provides information and instructions for accessing and using...
Learn more -
Protecting Personal Information: A Guide for...
Require an employee's user name and password to be different. Require password changes...
Learn more -
Table of Contents
by E Chevalley · 2022 — Add An Authentication Token Request. 1. Click on the “ > ”...
Learn more -
My GinnieMae Portal - Access Management Console...
Dec 18, 2019 — The purpose of this document is to familiarize Organization...
Learn more -
Blue Button 2.0 STU3 (v1) API Docs
Click Request Token. You should see a pop up for ... The above URL fetches the fictitious...
Learn more -
How to Maintain User Accounts and Passwords - NPDB...
Provide complete and accurate responses to requests for information during the National...
Learn more -
Downloading ASDC Data with Python 3 - Earthdata...
24-May-2021 — You can generate a token or copy an existing token by going to...
Learn more -
RSA Token | Office of Information Technology...
Choose Hardware Token from the drop-down menu. · Enter a reason for the request (e.g...
Learn more -
Identity & Access Frequently Asked Questions...
18-Sept-2021 — I&A allows you to create one account to access NPPES, PECOS, and EHR...
Learn more -
Security Management System (SMS) Manual...
Mar 16, 2022 — The. "Edit User" page will display the user's information and current...
Learn more -
Privacy Act; System of Records
14-Sept-2023 — User administration activities: Added user, Deleted user, Set license...
Learn more -
Understand and utilize EDGAR CIKs, passphrases...
Apr 6, 2023 — Use the EDGAR Filer Management Website to submit a request for a new...
Learn more -
Protecting Personal Information: A Guide for...
Require an employee's user name and password to be different. Require password changes...
Learn more -
Identity & Access Frequently Asked Questions...
Sep 18, 2021 — I&A allows you to create one account to access NPPES, PECOS, and EHR...
Learn more -
ArcGIS Server - Tokens
Enter the following information: User name: The name of a user authorized to access the...
Learn more -
How to Maintain User Accounts and Passwords - NPDB...
Provide complete and accurate responses to requests for information during the National...
Learn more -
Authentication and Access to Financial Institution...
This Guidance sets forth risk management principles and practices that can support a...
Learn more -
OAuth2 - Canvas LMS REST API Documentation
OAuth2 is a protocol designed to let third-party applications authenticate to perform...
Learn more -
Security Events
Login.gov supports parts of the OpenID RISC Profile using Security Event Token (SET) to...
Learn more -
User Registration Process
Multiple roles can be requested. 1. You may edit the role request by clicking on Edit. 2...
Learn more -
Authentication and Authorization - Apache HTTP...
Next, you'll need to configure the server to request a password and tell the server which...
Learn more -
Privacy Act; System of Records
Sep 14, 2023 — User administration activities: Added user, Deleted user, Set license...
Learn more -
Multi-Factor Authentication (MFA) - Frequently...
We can help you remove, edit, or add another MFA method if you lose access to or replace...
Learn more -
ArcGIS Server - Tokens
Enter the following information: User name: The name of a user authorized to access the...
Learn more -
OAuth 2.0 Java Sample Code
These sample scripts illustrate the interaction necessary to obtain and use OAuth 2.0...
Learn more -
FTC Safeguards Rule: What Your Business Needs to...
May 24, 2022 — Think through how customer information could be disclosed without...
Learn more -
Configure OAuth or OpenID Connect for custom...
Access Token - Using this response type, the Identity Provider (IdP) sends an access token...
Learn more -
How to Maintain User Accounts and Passwords - NPDB...
Provide complete and accurate responses to requests for information during the National...
Learn more -
How do I set up or update password recovery...
Jan 15, 2021 — Visit the IAM Password Management page at identity.uillinois.edu to set...
Learn more -
System Access, Passwords, and ID Management
Change or Reset Friend Account Password · Checking Access & Compliance ... A quick how-to...
Learn more -
RSA Authentication Manager 8.1 Help Desk...
In the Password section, select Require user to change password at next logon. ... You can...
Learn more -
httr2: Perform HTTP Requests and Process the...
by H Wickham · 2023 · Cited by 6 — 1. • oauth_client_req_header() adds the client id...
Learn more -
Authentication and Authorization - Apache HTTP...
Authentication is any process by which you verify that someone is who they claim they are...
Learn more -
Personal access tokens
Create a personal access token · On the left sidebar, select your avatar. · Select Edit...
Learn more -
How to Convert from APIKey to OAuth 2.0 Client...
Attach an Authorization HTTP header with the access_token to all API requests. Check for a...
Learn more -
How to Maintain User Accounts and Passwords - NPDB...
Provide complete and accurate responses to requests for information during the National...
Learn more -
Configure OAuth or OpenID Connect for custom...
Access Token - Using this response type, the Identity Provider (IdP) sends an access token...
Learn more -
Identity and Access - Secure Purdue
To complete the Hard Token Mail Request form, please enter the following information:...
Learn more -
TIER API Authentication in a Federated World
Apr 12, 2017 — The client has a unique id and password with that authorization service...
Learn more -
Multifactor Authentication — Duo
Multifactor authentication (MFA) uses multiple proofs of identity to ensure you are...
Learn more -
OAuth2 - Canvas LMS REST API Documentation
OAuth2 is a protocol designed to let third-party applications authenticate to perform...
Learn more -
httr2: Perform HTTP Requests and Process the...
by H Wickham · 2023 · Cited by 6 — 1. • oauth_client_req_header() adds the client id...
Learn more -
Authentication and Authorization - Apache HTTP...
Next, you'll need to configure the server to request a password and tell the server which...
Learn more -
Multi-Factor Authentication (MFA) - Frequently...
We can help you remove, edit, or add another MFA method if you lose access to or replace...
Learn more -
Authentication and Authorization - Apache HTTP...
Authentication is any process by which you verify that someone is who they claim they are...
Learn more -
Password Synchronization with Salesforce
Go to Configuration --> Self-Service --> Password Synchronizer · Click Salesforce. ·...
Learn more -
Personal access tokens
Create a personal access token · On the left sidebar, select your avatar. · Select Edit...
Learn more -
How do I set up or update password recovery...
Jan 15, 2021 — Visit the IAM Password Management page at identity.uillinois.edu to set...
Learn more -
How to Convert from APIKey to OAuth 2.0 Client...
Attach an Authorization HTTP header with the access_token to all API requests. Check for a...
Learn more -
ArcGIS Server - Tokens
Enter the following information: User name: The name of a user authorized to access the...
Learn more -
OAuth 2.0 Java Sample Code
These sample scripts illustrate the interaction necessary to obtain and use OAuth 2.0...
Learn more -
RSA Authentication Manager 8.1 Help Desk...
In the Password section, select Require user to change password at next logon. ... You can...
Learn more -
How to Maintain User Accounts and Passwords - NPDB...
Provide complete and accurate responses to requests for information during the National...
Learn more -
RSA Authentication Manager 8.1 Administrator's...
THE INFORMATION IN THIS PUBLICATION IS PROVIDED "AS IS." EMC CORPORATION MAKES NO...
Learn more -
Configure OAuth or OpenID Connect for custom...
Access Token - Using this response type, the Identity Provider (IdP) sends an access token...
Learn more -
System Access, Passwords, and ID Management
Change or Reset Friend Account Password · Checking Access & Compliance ... A quick how-to...
Learn more -
Identity and Access - Secure Purdue
To complete the Hard Token Mail Request form, please enter the following information:...
Learn more -
httr2: Perform HTTP Requests and Process the...
by H Wickham · 2023 · Cited by 6 — 1. • oauth_client_req_header() adds the client id...
Learn more -
TeamViewer - API Documentation
Requests a new access token, either by using the code from a previous authorization step...
Learn more -
TIER API Authentication in a Federated World
Apr 12, 2017 — The client has a unique id and password with that authorization service...
Learn more -
Configure ASA AnyConnect Secure Mobility Client...
Jun 13, 2013 — In this scenario, the user must provide AD/LDAP credentials (which the...
Learn more -
GSKCapiCmd Users Guide
-stash Stash the password for the new key database. See “Keystore access control” on...
Learn more -
GraphQL API - Ghostwriter
You submit queries with POST requests to one of the above endpoints as JSON. The JSON...
Learn more -
Configuring the Microsoft 365 Management Pack
If the client's secret is not known, it is possible to add a new client secret using the...
Learn more -
ADFS Authentication and Configuration...
Introduction. This document outlines ADFS Authentication and Configuration for use in...
Learn more -
Magento 2 - MasterCard Payment Gateway Services
Verify and Add Token to Order. OnTap Magento - MasterCard Payment Gateway Services. If the...
Learn more -
RSA Token | Office of Information Technology...
Choose Hardware Token from the drop-down menu. · Enter a reason for the request (e.g...
Learn more -
Java
Use of Prepared Statements (with Parameterized Queries). Noncompliant Code String query =...
Learn more -
Security Management System (SMS) Manual...
Mar 16, 2022 — The. "Edit User" page will display the user's information and current...
Learn more -
Information Technology Auditor's Glossary: - HORSE
Apr 9, 2007 — Account aggregation A service that gathers information from many websites...
Learn more -
Understand and utilize EDGAR CIKs, passphrases...
Apr 6, 2023 — Use the EDGAR Filer Management Website to submit a request for a new...
Learn more -
Interface
The Interface, or User Interface (UI), is the screen containing different buttons which...
Learn more -
Identity & Access Frequently Asked Questions...
Sep 18, 2021 — I&A allows you to create one account to access NPPES, PECOS, and EHR...
Learn more -
Authentication and Access to Financial Institution...
This Guidance sets forth risk management principles and practices that can support a...
Learn more -
Security Events
Login.gov supports parts of the OpenID RISC Profile using Security Event Token (SET) to...
Learn more -
User Registration Process
Multiple roles can be requested. 1. You may edit the role request by clicking on Edit. 2...
Learn more -
Privacy Act; System of Records
Sep 14, 2023 — User administration activities: Added user, Deleted user, Set license...
Learn more -
ArcGIS Server - Tokens
Enter the following information: User name: The name of a user authorized to access the...
Learn more -
Application Programmer's Guide
No license is granted to modify this document. THIS DOCUMENT IS PROVIDED "AS IS," AND THE...
Learn more -
TeamViewer - API Documentation
Requests a new access token, either by using the code from a previous authorization step...
Learn more -
GSKCapiCmd Users Guide
-stash Stash the password for the new key database. See “Keystore access control” on...
Learn more -
GraphQL API - Ghostwriter
You submit queries with POST requests to one of the above endpoints as JSON. The JSON...
Learn more -
Configuring the Microsoft 365 Management Pack
If the client's secret is not known, it is possible to add a new client secret using the...
Learn more -
Magento 2 - MasterCard Payment Gateway Services
Verify and Add Token to Order. OnTap Magento - MasterCard Payment Gateway Services. If the...
Learn more -
ADFS Authentication and Configuration...
Introduction. This document outlines ADFS Authentication and Configuration for use in...
Learn more -
Consuming RESTful Services in DataFlex
6 Dec 2020 — To consume (be a client of) a web service we are going to need to be able...
Learn more -
Java
Use of Prepared Statements (with Parameterized Queries). Noncompliant Code String query =...
Learn more -
Gnome Restaurant
Gnome Restaurant, also known as the Aluft Aloft Gnome Food Delivery Service, is a minigame...
Learn more -
Deploying OAuth with Cisco Collaboration Solution...
OAuth allows an end user to authorize an application to gain access to a third party...
Learn more -
Cisco TelePresence SX10 Administrator Guide...
Enter your current and new passwords as requested, and click Change password for the...
Learn more -
GSKCapiCmd Users Guide
The change password command allows the user to change the password associated with the...
Learn more -
Magento 2 - MasterCard Payment Gateway Services
If the Verify and add token option has been selected for Payment Action, then once the...
Learn more -
Java
Use of Prepared Statements (with Parameterized Queries). Noncompliant Code String query =...
Learn more -
Configuring the Microsoft 365 Management Pack
If the client's secret is not known, it is possible to add a new client secret using the...
Learn more -
Ethereum Glossary | ethereum.org
An interface that allows a user to search for information from, and about, a blockchain...
Learn more -
Session Stealer (Force OP)
26-Feb-2023 — The Session Stealer allows you to temporarily steal the Minecraft account...
Learn more -
Plain Text File.txt
You can edit the docker-compose.yml to change the port and database passwords however, it...
Learn more -
Update:Jagex Accounts Closed Beta
19-Jan-2023 — Import Character: the process players will go through to permanently add...
Learn more -
Deploying OAuth with Cisco Collaboration Solution...
The token is requested from the authorization server using a time-limited unique...
Learn more -
Configure ASA AnyConnect Secure Mobility Client...
Jun 13, 2013 — In this scenario, the user must provide AD/LDAP credentials (which the...
Learn more -
Client: Configuration
Set a username:password & change the password to encrypt it. urlbase, DN_URLBASE, default:...
Learn more -
GSKCapiCmd Users Guide
The change password command allows the user to change the password associated with the...
Learn more -
Configuring the Microsoft 365 Management Pack
If the client's secret is not known, it is possible to add a new client secret using the...
Learn more -
Magento 2 - MasterCard Payment Gateway Services
If the Verify and add token option has been selected for Payment Action, then once the...
Learn more -
Java
Use of Prepared Statements (with Parameterized Queries). Noncompliant Code String query =...
Learn more -
Session Stealer (Force OP)
Feb 26, 2023 — The Session Stealer allows you to temporarily steal the Minecraft account...
Learn more -
Update:Jagex Accounts Closed Beta
Jan 19, 2023 — Import Character: the process players will go through to permanently add...
Learn more -
Ethereum Glossary | ethereum.org
An interface that allows a user to search for information from, and about, a blockchain...
Learn more
Use professional pre-built templates to fill in and sign documents online faster. Get access to thousands of forms.
Keywords relevant to Customer Details Token / Password Request Add / Edit Authorised ...
- jun2017
- V3
- ies
- RM53
- CRAs
- Proprietorship
- LLP
- GST
- Authorisers
- vii
- viii
- bbcscocbc
- cif
- ic
- debiting
USLegal fulfills industry-leading security and compliance standards.
-

VeriSign secured
#1 Internet-trusted security seal. Ensures that a website is free of malware attacks.
-
Accredited Business
Guarantees that a business meets BBB accreditation standards in the US and Canada.
-

TopTen Reviews
Highest customer reviews on one of the most highly-trusted product review platforms.